Zero‑day surge strains enterprise resilience. AI‑driven detection and zero‑trust defenses rise. 🚨⚙️
Good morning, February 11, 2026. Here’s the latest cyber and AI threat intelligence.
Today's headlines
- Amaranth‑Dragon weaponizes a new zero‑day in Southeast Asia.
- Microsoft patches 59 flaws, six actively exploited.
- Cloud‑logging technique exposes hidden threat actor activity.
- AI‑assisted PowerShell attacks detailed in Muddled Libra playbook.
- VMware’s vDefend advances zero‑trust in private clouds.
1️⃣ Amaranth‑Dragon exploits CVE‑2025‑8088 for Southeast Asian espionage
Key Points:
- APT‑41 linked group leverages unpublished zero‑day CVE‑2025‑8088.
- Primary targets include government, telecom and tech firms in Southeast Asia.
- Combines supply‑chain intrusion with credential theft and data exfiltration.
- Shows increased weaponization of unknown vulnerabilities for strategic espionage.
Description:
Check Point researchers identified Amaranth‑Dragon, an extension of APT‑41, using the newly discovered CVE‑2025‑8088 to compromise high‑value assets across Southeast Asian nations. The campaign blends classic supply‑chain compromise with novel exploit delivery, enabling long‑term intelligence gathering and credential harvesting from critical sectors.
Why It Matters:
Enterprises operating in the region face heightened risk of stealthy data breaches and intellectual property loss. The use of a zero‑day underscores the need for proactive vulnerability management, threat‑hunts focused on unknown exploits, and enhanced monitoring of supply‑chain interactions.
2️⃣ Microsoft releases patches for 59 flaws, including six active zero‑day exploits

Key Points:
- 59 vulnerabilities addressed across Windows, Office, Azure and more.
- Six of the flaws are actively exploited zero‑day attacks.
- Five critical issues include privilege‑escalation and remote code execution vectors.
- Patch Tuesday highlights a continued trend of high‑impact vulnerabilities.
Description:
Microsoft’s February security update bundle covers 59 security issues, ranging from privilege escalation to remote code execution, with six of them confirmed as being exploited in the wild. Critical patches span client operating systems, server products, and cloud services, reinforcing the importance of timely updates.
Why It Matters:
Unpatched systems remain a primary attack surface for nation‑state and criminal actors. Organizations must expedite deployment of these patches to mitigate remote compromise risks, especially for services exposed to the internet and internal privileged accounts.
3️⃣ Threat intel report flags Romania pipeline outage and rising ransomware activity

Key Points:
- Conpet, Romania’s national oil pipeline operator, suffered a disruptive cyberattack.
- Ransomware groups increased targeting of critical infrastructure in Eastern Europe.
- Supply‑chain compromises remain a key vector for lateral movement.
- Emerging threats include AI‑generated phishing and credential‑stuffing campaigns.
Description:
The 9th‑February Check Point Threat Intelligence Report highlights a recent attack on Romania’s Conpet pipeline operator that caused service interruption and website downtime. The analysis also notes a surge in ransomware activity against critical infrastructure, employing sophisticated credential‑stuffing and AI‑augmented phishing.
Why It Matters:
Disruption of energy utilities demonstrates the tangible impact of cyber incidents on national economies. CISOs must prioritize segmentation, robust backup strategies, and advanced threat detection to defend against ransomware and supply‑chain based attacks.
4️⃣ Novel cloud‑logging technique uncovers hidden threat‑actor operations
Key Points:
- Introduces a method to correlate multi‑cloud logs for attacker behavior.
- Detects lateral movement and credential abuse across SaaS, IaaS and PaaS.
- Reduces detection latency from days to minutes.
- Applicable to AWS, Azure, Google Cloud and hybrid environments.
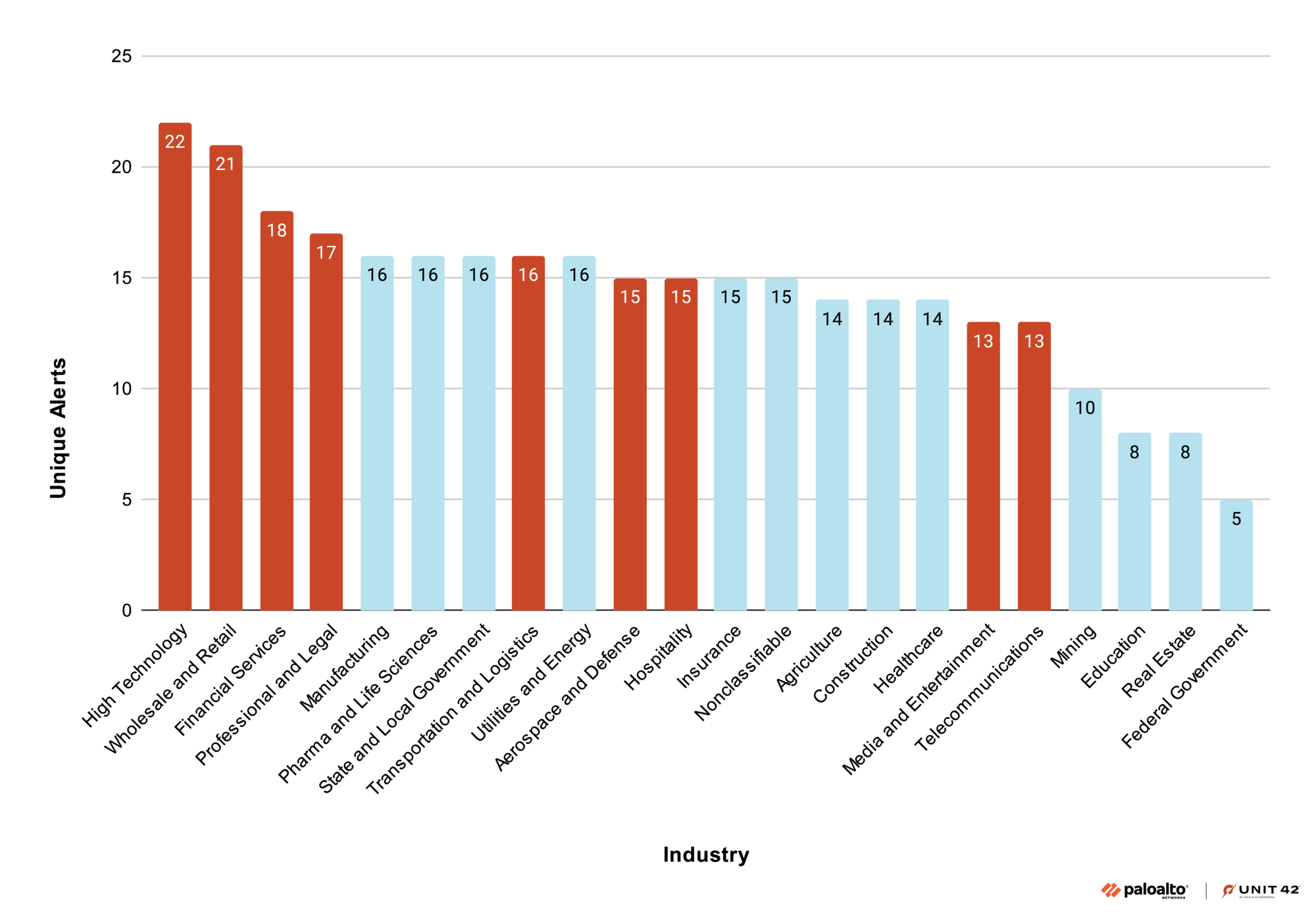
Description:
Palo Alto Networks Unit 42 presents a new detection framework that leverages granular cloud service logs to trace threat‑actor activities across diverse environments. By normalizing and analyzing log streams, the technique reveals stealthy lateral movements and privilege misuse that traditional tools miss.
Why It Matters:
As enterprises shift workloads to the cloud, visibility gaps increase. Implementing this log‑correlation approach enables security teams to identify advanced attacks early, limiting potential data loss and supporting compliance with cloud‑security standards.
5️⃣ Publicly available hacking tools proliferate across global incidents
Key Points:
- Catalogs widely‑used ransomware kits, credential‑harvesting frameworks, and exploit tools.
- Shows increased adoption of open‑source malware by both nation‑state and criminal actors.
- Highlights trends in tool modularity and ease of distribution.
- Provides guidance for defenders on detection signatures and mitigation.
Description:
CISA’s advisory outlines the explosion of publicly available tools that have been observed in cyber incidents worldwide, ranging from ransomware encryptors to credential‑harvesting utilities. The report emphasizes the democratization of sophisticated capabilities previously limited to advanced threat groups.
Why It Matters:
The accessibility of these tools raises the baseline threat level for all organizations. Defensive strategies must include threat‑intel‑driven detection rules, endpoint monitoring, and proactive threat‑hunting to counter tool‑based attacks.
6️⃣ Muddled Libra’s playbook reveals AI‑assisted PowerShell campaigns

Key Points:
- Operates through PowerShell scripts enhanced by AI‑generated phishing content.
- Targets enterprises for credential theft and lateral movement.
- Employs modular stages: initial access, persistence, data exfiltration.
- Demonstrates rapid adaptation of AI for social engineering.
Description:
Unit 42 details the operational methodology of the Muddled Libra group, which combines AI‑crafted phishing messages with PowerShell payloads to infiltrate corporate networks. The playbook includes step‑by‑step tactics for establishing persistence, escalating privileges, and exfiltrating data.
Why It Matters:
AI‑augmented social engineering increases the success rate of phishing attacks, making traditional awareness training insufficient. Organizations should adopt AI‑driven email security solutions and monitor PowerShell usage for anomalous behavior.
7️⃣ Notepad markdown feature enables remote code execution on Windows 11

Key Points:
- A markdown rendering bug allows crafted files to execute arbitrary code.
- Impact is confined to Windows 11 systems running the updated Notepad component.
- Exploit can be delivered via email or download, leading to silent infection.
- Microsoft has issued an out‑of‑band fix to mitigate the vulnerability.
Description:
Researchers discovered that Notepad’s new markdown preview capability on Windows 11 can be abused to trigger remote code execution. By opening a specially crafted markdown file, attackers can run malicious payloads without user interaction, presenting a novel attack vector for Windows users.
Why It Matters:
Given Notepad’s ubiquitous presence, this flaw widens the attack surface for ransomware and espionage campaigns. Immediate patch deployment and restricting markdown file handling are essential to prevent exploitation.
8️⃣ CrowdStrike highlights six zero‑days patched, with active RDP exploit
Key Points:
- Six zero‑day vulnerabilities were addressed in February’s Patch Tuesday.
- CVE‑2026‑21533, an RDP elevation‑of‑privilege bug, is actively exploited.
- Elevation of privilege remains the dominant exploitation technique (42%).
- CrowdStrike contributed discovery of the RDP flaw to Microsoft.
Description:
CrowdStrike’s analysis of the February 2026 Patch Tuesday release notes six zero‑day patches, including a critical Remote Desktop Services vulnerability (CVE‑2026‑21533) that attackers are leveraging to gain elevated privileges on Windows servers. The report outlines exploit trends and mitigation priorities.
Why It Matters:
RDP remains a high‑value target for lateral movement and ransomware. Rapid remediation of the disclosed vulnerability, coupled with network segmentation and multi‑factor authentication for remote access, is vital to reduce breach risk.
9️⃣ VMware launches vDefend for lateral movement control in private clouds

Key Points:
- vDefend provides micro‑segmentation and automated response to lateral threats.
- Integrates with existing VMware Cloud Foundation environments.
- Leverages behavioral analytics to detect suspicious east‑west traffic.
- Aims to simplify zero‑trust implementation for private cloud workloads.
Description:
VMware’s new vDefend solution extends zero‑trust principles to private cloud infrastructures by automatically enforcing micro‑segmentation policies and delivering real‑time threat containment. The platform uses AI‑driven analytics to identify anomalous lateral movement and triggers isolation actions.
Why It Matters:
Enterprises adopting hybrid clouds need granular control over internal traffic to prevent credential abuse. vDefend’s automated policy enforcement helps reduce manual configuration errors and accelerates compliance with zero‑trust frameworks.
🔟 AI simplifies Zero‑Trust rollout, boosting policy automation
Key Points:
- AI generates context‑aware access policies based on user behavior and asset risk.
- Reduces time to deploy zero‑trust controls by up to 70%.
- Provides continuous risk scoring and automated policy adjustments.
- Integrates with existing security stacks to harmonize enforcement.
Description:
VMware’s AI‑driven platform automates the creation and maintenance of zero‑trust policies, translating behavioral insights into granular access controls. The technology continuously evaluates risk, updating policies without manual intervention, thereby streamlining compliance efforts.
Why It Matters:
The complexity of manual zero‑trust implementations often delays adoption. AI‑enabled automation empowers security teams to achieve comprehensive protection faster, enhancing overall security posture and reducing operational overhead.
Stay vigilant and keep your defenses ahead.
Member discussion