Zero‑day firewalls and AI model theft raise risk 🚨. IoT and OAuth abuse widen surface 🤖.
Good morning, March 2, 2026 – here’s your critical cybersecurity briefing.
Today's headlines
- SonicWall firewalls scanned via commercial proxies.
- GoAnywhere MFT zero‑day exploited despite perimeter defenses.
- Chrome extension hijack targets Gemini panel with CVE‑2026‑0628.
- Anthropic AI model theft and Roundcube webmail RCE observed.
- OAuth redirection abuse fuels sophisticated phishing attacks.
1️⃣ Reconnaissance of SonicWall firewalls via proxy networks
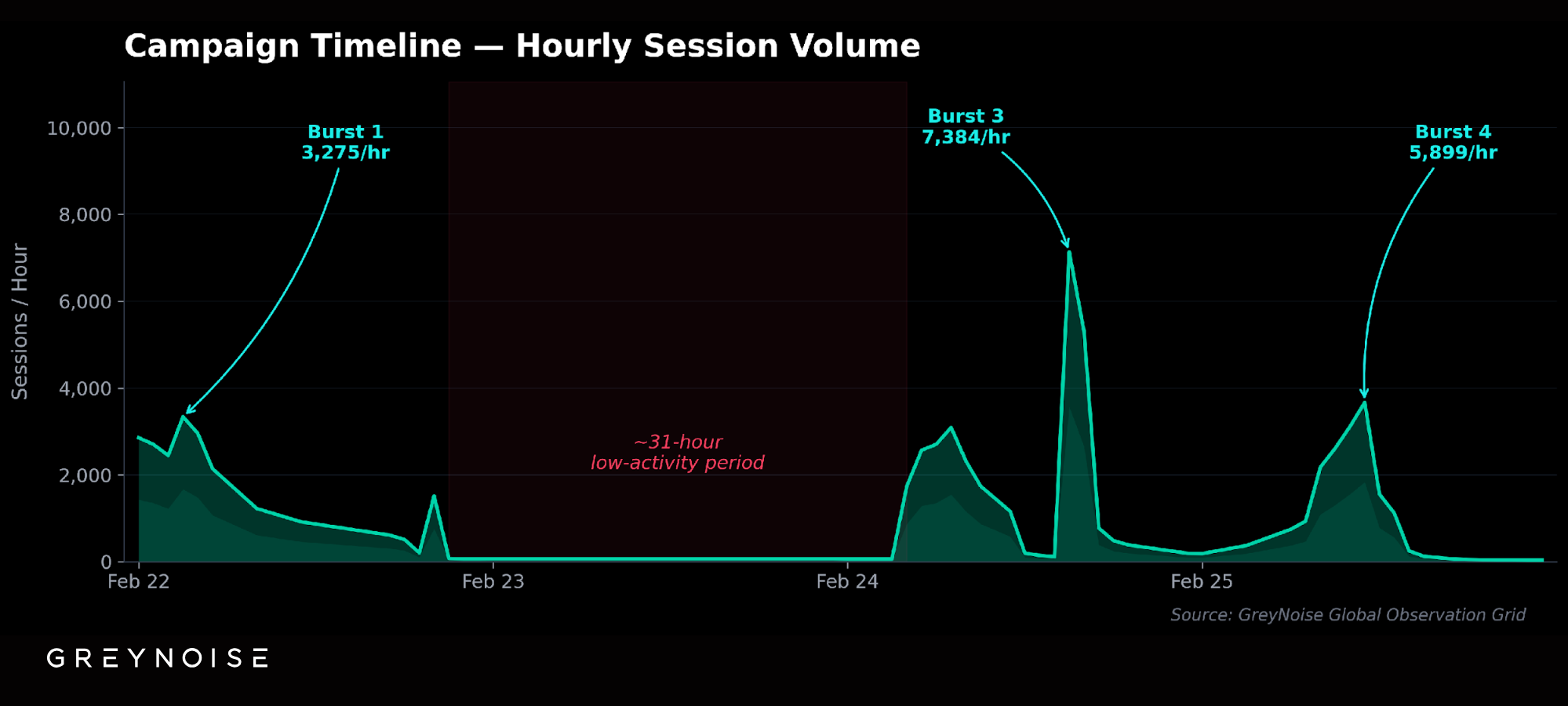
Key Points:
- Attackers leverage commercial proxy services to hide origin.
- Targets focus on SonicWall devices across SMB environments.
- Increased scanning noise overwhelms traditional IDS signatures.
- Real‑time blocklists can curb malicious traffic.
Description:
GreyNoise reports a coordinated active‑recon campaign that uses legit proxy infrastructure to enumerate SonicWall firewalls, generating high‑volume scan traffic that blends with normal traffic patterns.
Why It Matters:
The use of reputable proxies masks attacker IPs, making detection harder for firewalls and SOCs. Enterprises relying on SonicWall must adopt adaptive blocklists and enrich logs with proxy intelligence to prevent foothold attempts.
2️⃣ GoAnywhere MFT zero‑day bypasses perimeter firewalls

Key Points:
- CVE‑2025‑10035 is a critical deserialization flaw (CVSS 10.0).
- Exploited by Storm‑1175 to evade perimeter defenses.
- CISA warns such zero‑days can remain undetected for months.
- Impact spans data transfer services used by large enterprises.
Description:
A zero‑day vulnerability in GoAnywhere MFT’s license servlet was exploited in September 2025, allowing attackers to execute arbitrary code and bypass traditional firewall controls.
Why It Matters:
Perimeter firewalls alone cannot stop application‑layer exploits. Organizations must implement rapid patching, application‑layer monitoring, and zero‑trust segmentation to mitigate the risk of similar high‑severity flaws.
3️⃣ Chrome extension hijack in Gemini panel
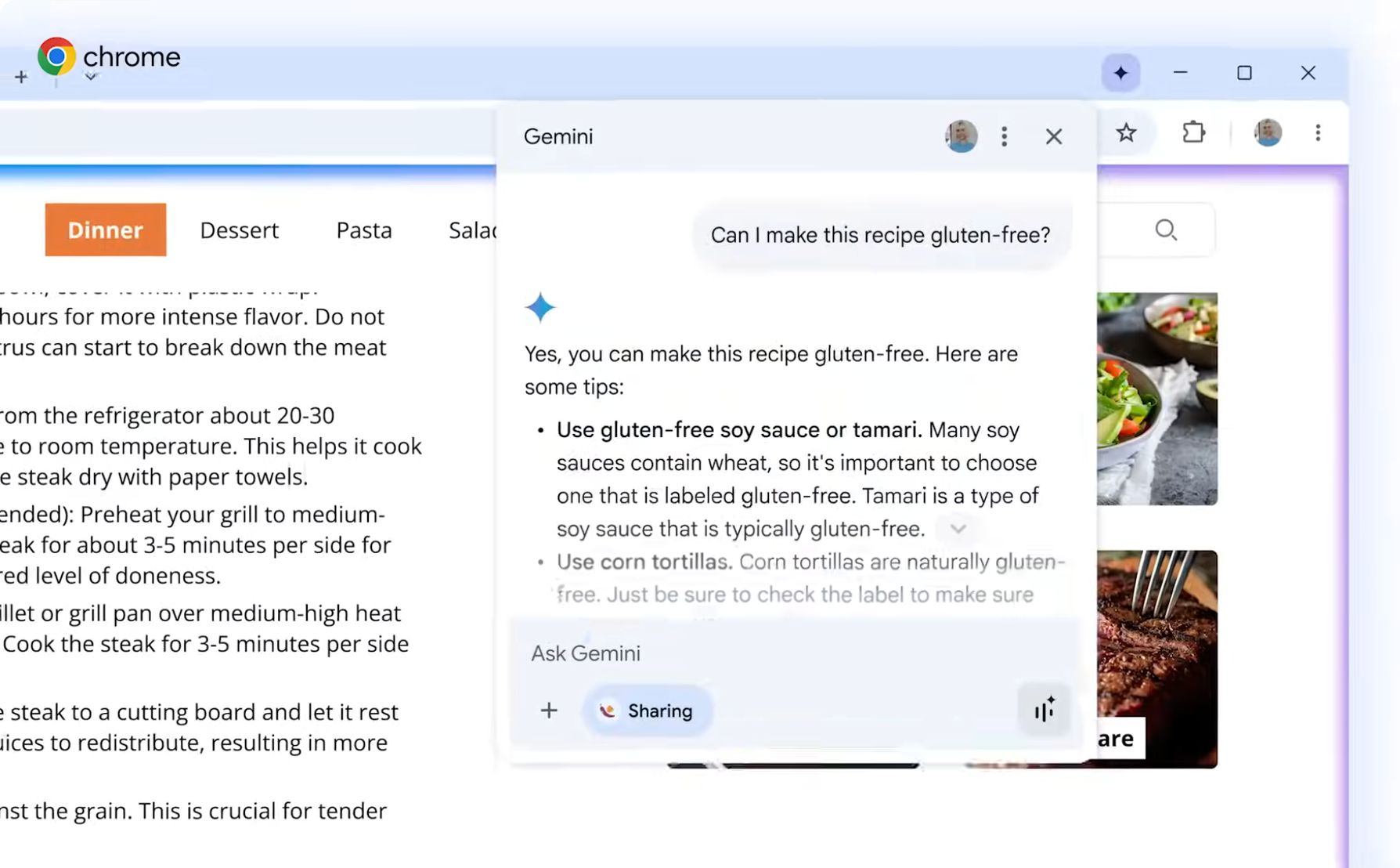
Key Points:
- CVE‑2026‑0628 allows malicious Chrome extensions to hijack Gemini UI.
- Enables credential theft and unauthorized command execution.
- Targets users of AI‑driven browser agents and developer tools.
- Patch released; immediate update recommended.
Description:
Research from Palo Alto Networks reveals a vulnerability in Google Chrome where malicious extensions can hijack the newly introduced Gemini panel, compromising user sessions and potentially leaking AI model prompts.
Why It Matters:
Browsers are a primary attack vector for supply‑chain and AI‑agent threats. Prompt patching and strict extension controls are essential to protect enterprise users and prevent data exfiltration.
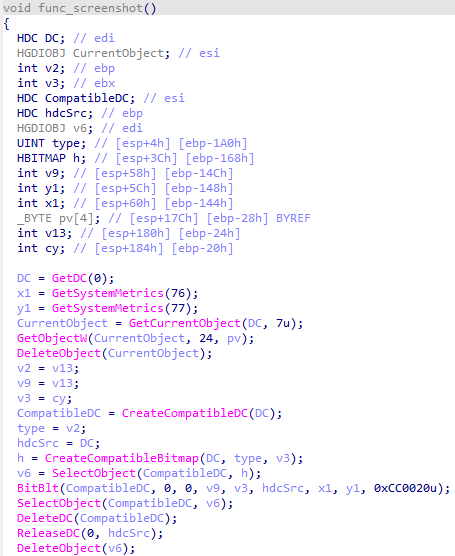
4️⃣ AI model theft and Roundcube webmail exploits

Key Points:
- Anthropic reports coordinated “distillation” attacks by China‑based AI firms.
- Millions of Claude exchanges harvested to train competing models.
- Roundcube CVE‑2025‑49113 enables post‑auth remote code execution.
- Stolen keys grant access to shared workspaces and file tampering.
Description:
Checkpoint’s March threat report highlights a dual threat: large‑scale AI model theft via fraudulent accounts and active exploitation of two Roundcube Webmail vulnerabilities in the wild.
Why It Matters:
Both incidents demonstrate how intellectual property and email infrastructure are becoming high‑value targets, urging enterprises to enforce stricter access controls, monitor anomalous usage, and apply timely webmail patches.
5️⃣ CrowdStrike gains NCSC CIR assurance for IR

Key Points:
- NCSC CIR certification validates incident‑response capabilities.
- Boosts trust for public‑sector and regulated customers.
- Supports integration with Falcon Fusion SOAR for automation.
- Positions CrowdStrike as a compliant vendor for high‑security environments.
Description:
CrowdStrike announced it has achieved the UK National Cyber Security Centre’s CIR assurance, confirming its incident‑response services meet rigorous government standards.
Why It Matters:
Certification provides CISOs with confidence in outsourcing IR functions, especially in regulated sectors, and facilitates faster breach containment through proven automation and governance frameworks.
6️⃣ LummaStealer resurfaces paired with CastleLoader
Key Points:
- LummaStealer evolves to mimic legitimate user behavior.
- Often delivered alongside CastleLoader loader module.
- Targets credential stores and cryptocurrency wallets.
- Behavior‑based detection required to catch evolving payloads.
Description:
Bitdefender’s lab analysis shows LummaStealer has re‑emerged, now distributed with CastleLoader, employing sophisticated social‑engineering to gain initial access and exfiltrate data.
Why It Matters:
The malware’s ability to blend in with normal activity challenges signature‑based defenses, urging security teams to deploy UEBA and endpoint detection platforms capable of spotting anomalous patterns.
7️⃣ OAuth redirection abuse fuels phishing campaigns
Key Points:
- Attackers exploit open redirect URIs in OAuth flows.
- Allows seamless delivery of phishing pages and malware.
- Bypasses traditional URL filtering and domain reputation checks.
- Recommendations include strict redirect‑URI whitelisting.
Description:
Microsoft Security researchers detail how threat actors manipulate OAuth redirection endpoints to craft convincing phishing links that lead victims to malicious payloads without triggering conventional defenses.
Why It Matters:
OAuth abuse undermines trust in federated authentication, making it critical for organizations to enforce redirect URI validation and monitor anomalous auth traffic to prevent credential compromise.
8️⃣ Samsung TV ACR privacy fix after Texas breach

Key Points:
- Automatic Content Recognition (ACR) collected viewing data without consent.
- Texas incident exposed privacy risks of smart TV telemetry.
- Firmware update now disables ACR by default.
- Highlights need for secure default settings in IoT devices.
Description:
Following a privacy investigation in Texas, Samsung released a firmware patch that disables the Automatic Content Recognition feature on its smart TVs, stopping unauthorized data collection.
Why It Matters:
IoT devices can become inadvertent surveillance tools. Enterprises deploying smart TVs must verify firmware settings and enforce privacy‑first configurations to mitigate data leakage.
9️⃣ Kimwolf botnet expansion under botmaster Dort
Key Points:
- Botmaster “Dort” operates the Kimwolf botnet across compromised proxies.
- Supports credential‑stuffing and DDoS services for hire.
- Utilizes I2P anonymity network to hide command traffic.
- Targets small businesses and unmanaged web services.
Description:
KrebsOnSecurity profiles the Kimwolf botnet’s growth under its enigmatic leader, Dort, detailing its reliance on proxy abuse and I2P for covert operations.
Why It Matters:
The botnet’s ability to leverage legitimate proxy infrastructure complicates detection and underscores the need for rigorous outbound traffic monitoring and proxy reputation filtering.
🔟 Student loan data breach reveals 2.5 M records

Key Points:
- Personal information of 2.5 million borrowers exposed.
- Breach traced to a third‑party loan servicing vendor.
- Includes Social Security numbers, addresses, and loan details.
- Raises concerns over vendor risk management and data stewardship.
Description:
ThreatPost reports a massive breach of a student loan servicing platform that leaked sensitive data of over 2.5 million individuals, attributed to insufficient security controls at a third‑party provider.
Why It Matters:
The incident highlights the critical importance of supply‑chain security and continuous vendor assessments to protect personal data assets from exposure.
Stay vigilant and prioritize proactive defenses.
Member discussion