Windows Delete Leaves Traces: Secure Shredding Essential for GDPR Compliance
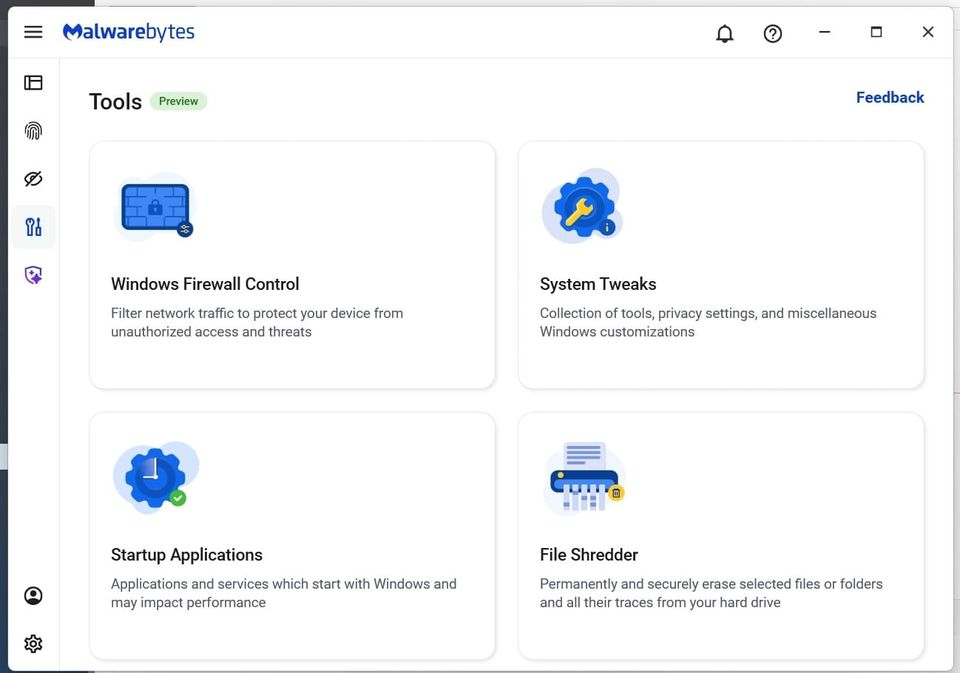
Malwarebytes recently demonstrated that the default “delete” action in Windows does not actually erase data; it merely removes the directory entry while leaving the underlying sectors intact. Forensic utilities can scan the free space and reconstruct the files, even after they appear to be gone. The study highlighted a dedicated Windows file‑shredder that overwrites data multiple times, rendering the remnants unrecoverable.
The residual data poses a serious risk. Attackers who gain low‑level access can recover sensitive documents, credentials, or personal information that organizations thought were discarded. In regulated environments, such recoverable remnants can trigger GDPR, CCPA, or industry‑specific privacy violations, exposing companies to hefty fines and reputational damage.
Defenders must treat file deletion as a policy decision, not a default OS behavior. Deploying secure‑shred tools, enforcing data‑retention policies that include cryptographic erasure, and training staff on proper disposal practices are essential steps to close this hidden data leakage vector and maintain compliance.
Categories: Data Protection & Privacy
Source: Read original article



Member discussion