Windows Delete Fails: Remnants Leak Data, Defenders Must Enforce Secure Erasure
Malwarebytes’ recent analysis shows that the default Windows file‑deletion process merely removes directory entries, leaving the underlying data blocks untouched on disk. Even when users employ third‑party “shredder” utilities, many of the deleted files can still be reconstructed with forensic tools, exposing credentials, proprietary documents, and other sensitive artifacts.
The lingering data creates a low‑effort vector for threat actors who can harvest recovered files from compromised endpoints, exfiltrate them, or use them for credential‑stuffing and lateral movement. Organizations risk violating data‑protection regulations, incurring breach penalties, and facing prolonged incident‑response cycles because the assumed “delete” never truly erased the information.
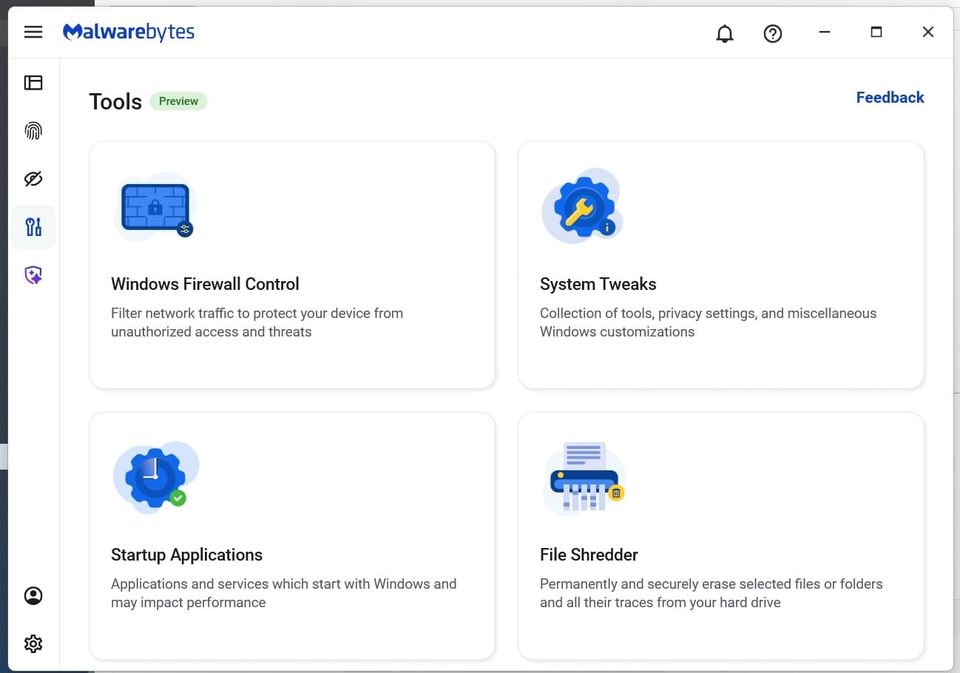
Defenders should treat deletion as a potential data‑leak point: deploy verified secure‑erase solutions that overwrite file clusters, enforce policies that require cryptographic shredding for high‑value data, and regularly audit storage media for residual artifacts. Integrating secure deletion into endpoint hardening and DLP workflows reduces the attack surface and ensures compliance with data‑privacy mandates.
Categories: Data Protection & Privacy, Compliance & Regulation
Source: Read original article




Member discussion