Turn Cloud Logs into Threat Intel: Unit42’s New Detection Playbook
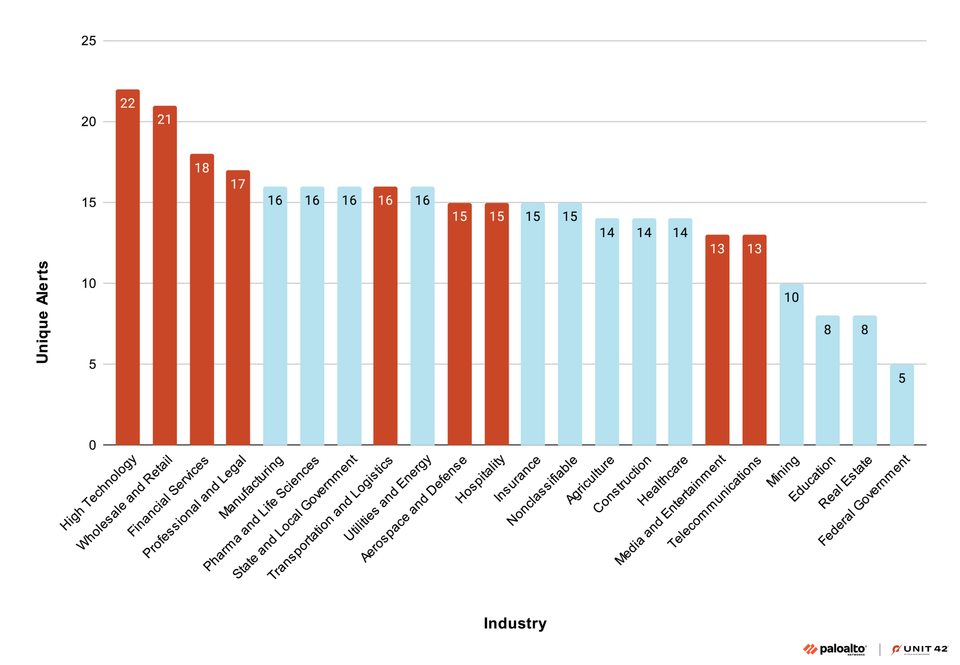
Unit42’s latest research shows how defenders can repurpose native cloud logs—such as AWS CloudTrail and Azure Activity Logs—to surface the behavioral fingerprints of known adversary groups. By automatically correlating login anomalies, suspicious API calls, and lateral‑movement patterns across accounts and services, the methodology creates a “threat‑actor signature” that flags malicious cloud activity in near real‑time.
For security teams, this means turning abundant, often‑overlooked log data into actionable threat intelligence, cutting dwell time, and improving coverage of cloud‑native attacks. As enterprises continue to expand their cloud footprints, integrating these detection techniques into SIEMs and SOAR platforms is essential for staying ahead of actors who exploit misconfigurations and cloud‑specific attack vectors.
Categories: Identity & Access Management (IAM), Security Culture & Human Factors, AI Security & Threats
Source: Read original article


Member discussion