QR Code Phishing Spikes, Targeting Users on Web & Mobile
Palo Alto Networks’ Unit 42 has documented a sharp increase in QR‑code phishing campaigns that direct victims to credential‑
CrowdStrike Wins Gartner Customer’s Choice, Patches Six Zero‑Day Auth Flaws
CrowdStrike has been named a Gartner Peer Insights “Customer’s Choice” for its user authentication suite, a distinction that reflects
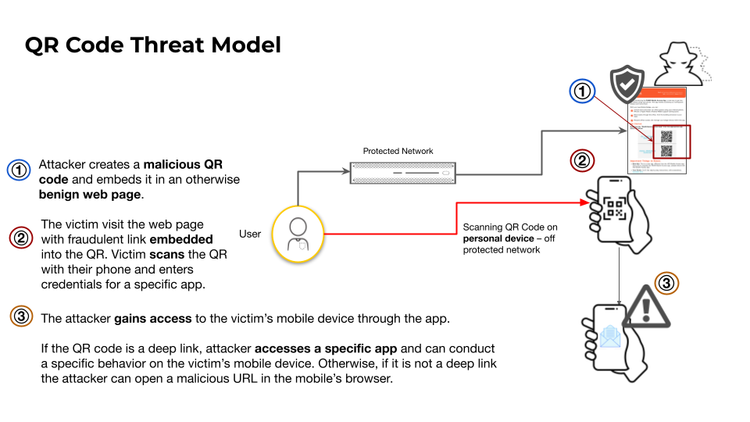
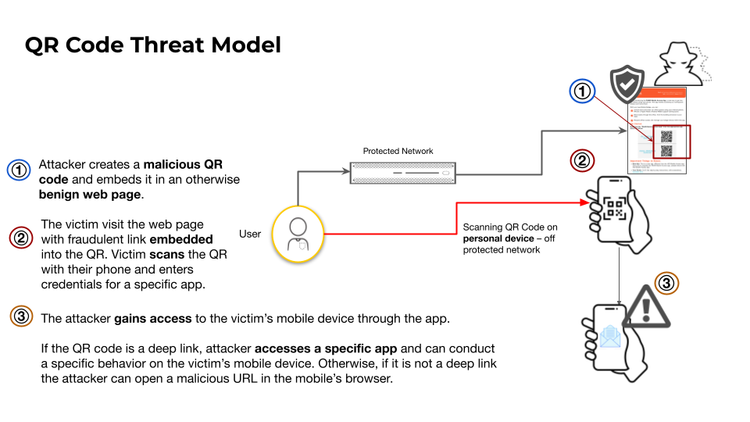
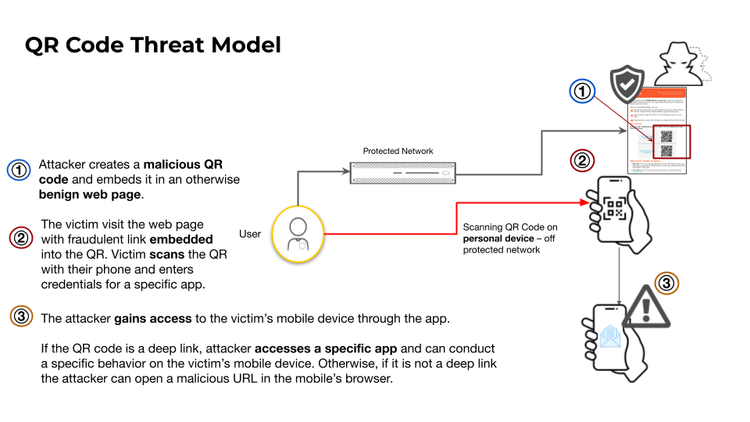
QR Code Phishing Expands Mobile and Web Attack Surface
Threat actors are increasingly embedding malicious URLs in QR codes, allowing them to sidestep traditional network and email filters. When
Active Scans Target New BeyondTrust RCE Vulnerability – Prepare for Privileged Access Threats
GreyNoise researchers have identified a surge in scanning activity aimed at the recently disclosed BeyondTrust remote code execution flaw (CVE‑
QR Code Phishing Turns Smartphones Into New Attack Vectors
Researchers observed threat actors embedding malicious URLs in QR codes that, when scanned, direct victims to credential‑harvesting webpages or
CrowdStrike’s Human‑AI Loop Accelerates Zero‑Day Detection and Response
CrowdStrike disclosed a “human‑AI feedback loop” in which threat analysts continuously inject contextual insights—such as tactics, techniques, and
Muddled Libra Leverages AI to Automate Phishing and Cloud Intrusions
Unit42’s latest investigation uncovered that the Muddled Libra ransomware group has embedded artificial‑intelligence models into its operational playbook.
AI‑Boosted Phishing Fuels PowerShell Attacks by Muddled Libra Group
Muddled Libra has refined its intrusion chain by leveraging generative AI to produce highly contextualized phishing emails that bypass traditional
Romanian Pipeline Hit by Attack; Ransomware Targeting Critical Infrastructure Soars
On 9 February, Check Point’s Threat Intelligence Report documented a successful intrusion against Conpet, Romania’s main pipeline operator.
VMware Unveils vDefend: Zero‑Trust Micro‑Segmentation for Hybrid Cloud
VMware’s security team announced the vDefend framework, a set of built‑in controls that bring zero‑trust principles to