Exec Blames Subordinate, Reveals Critical Insider Risk and Governance Gaps
A senior security leader publicly pinned a recent data‑leak incident on a junior team member, claiming the employee had
OWASP Shifts from Meetup to Hub—What It Means for Security Teams
OWASP announced that its long‑standing Meetup platform is being retired. All community coordination, event scheduling, and discussion will now
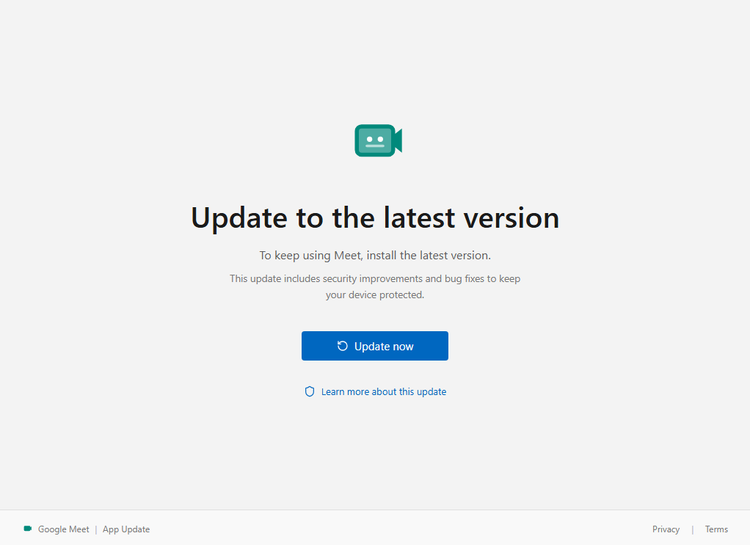
Fake Google Meet Update Delivers Full‑Control RAT to Enterprises
A phishing campaign is distributing a counterfeit Google Meet “update” dialog that mimics the legitimate UI. When a user clicks
App Exposes Nearby Smart Glasses via IR Signature Scan
A developer has published a mobile application that uses the device’s camera and infrared (IR) sensor to identify the
OWASP Sunset's Meetup Platform, Shifts Event Coordination to Secure Alternatives
The OWASP Foundation announced that its long‑used Meetup.com group will be decommissioned by the end of Q2 2024.
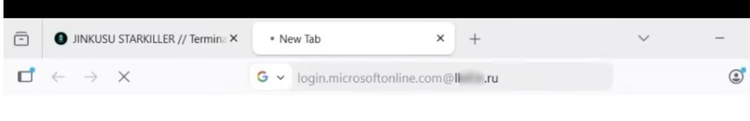
Starkiller Phishing Service Mirrors Real Logins, Skips MFA and Harvests Tokens
KrebsOnSecurity exposed a new phishing‑as‑a‑service platform dubbed “Starkiller” that routes victims through live, unmodified login pages of
AI-Driven Threats Surge: Generative Models Fuel Malware, Phishing, and Deepfake Attacks
CrowdStrike’s Global Threat Report for 2026 reveals a sharp rise in adversaries exploiting generative AI to automate the creation
AI-Driven Threats Surge: Check Point 2025 Reveals New Weaponization Playbook
Check Point’s 2025 retrospective shows threat actors have moved from experimental use of artificial intelligence to fully integrating it
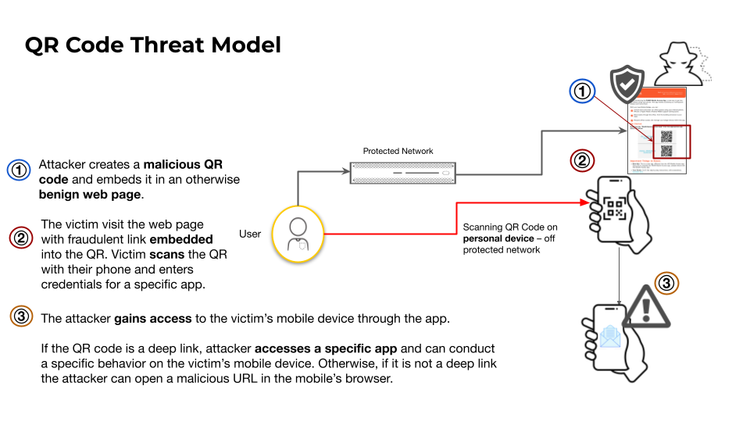
QR Code Phishing Surge Hits Web and Mobile: Threats Hide in Plain Sight
Threat actors are increasingly embedding malicious URLs and deep‑link payloads into QR‑code images that appear on posters, transit
Scale SOC Automation Fast with CrowdStrike Falcon Fusion Playbooks
CrowdStrike’s recent blog walks security teams through extending their SOC using Falcon Fusion, the vendor’s native SOAR platform.