Fake Malwarebytes Renewal Calendar Invites Deploy Credential‑Harvesting Links
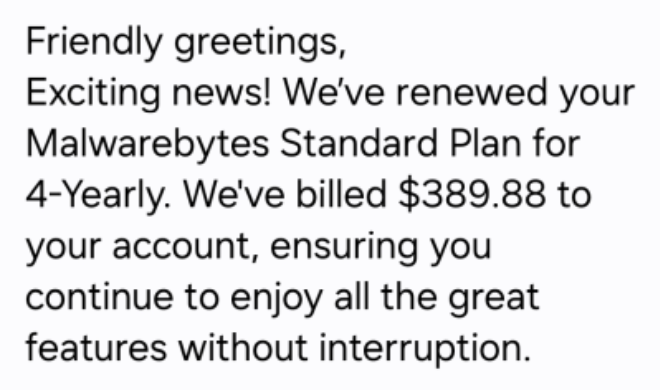
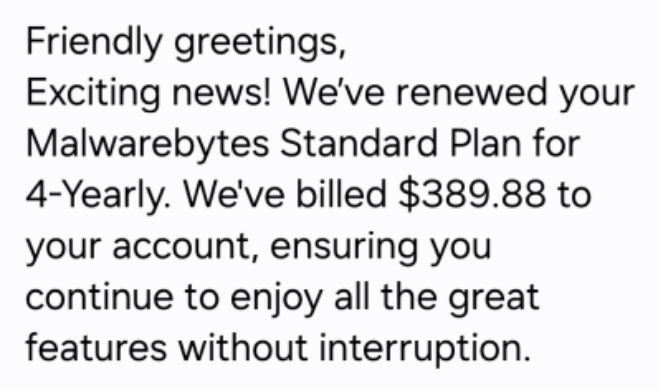
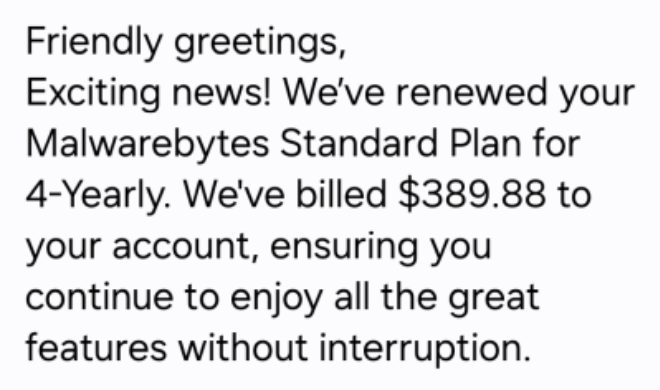
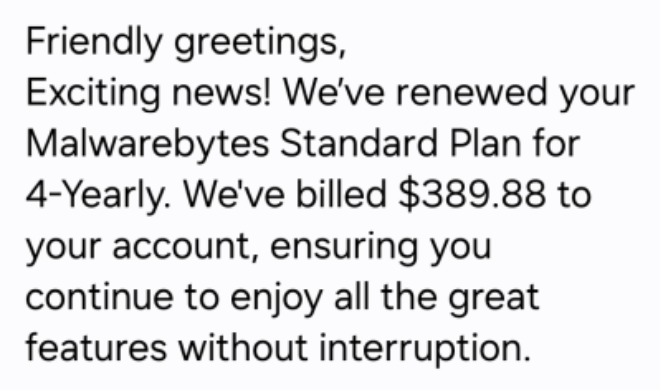
Attackers are sending calendar invitations that mimic Malwarebytes renewal notices. The invites contain malicious URLs that, when clicked, direct users
Malwarebytes Renewal Invite Scam Uses Calendar Events to Harvest Credentials
A new social‑engineering campaign is leveraging calendar invitations to distribute counterfeit Malwarebytes renewal notices. The invites appear to come
Fake Renewal Calendar Invites Used to Harvest Credentials – Malwarebytes Alerts
Malwarebytes uncovered a coordinated campaign distributing fraudulent calendar invitations that mimic subscription renewal reminders. The invites contain malicious URLs that,
Fake Calendar Renewal Notices Deliver Malware via Malicious Links
Attackers are sending bogus calendar invitations that masquerade as subscription renewal reminders. The .ics files embed links that appear to
OWASP Shuts Down Meetup Hub – Defenders Must Reroute Community Intel
The OWASP Foundation has officially retired its dedicated Meetup platform, directing all project and chapter members to shift conversations to
OWASP Moves Away from Meetup to Hardened Collaboration Platforms
OWASP announced it is decommissioning its long‑standing Meetup group, urging members to migrate discussions, project coordination, and event planning
OWASP Shuts Down Meetup Platform, Shifts to Secure Cloud‑Based Event Hub
The OWASP Foundation announced the retirement of its long‑standing Meetup platform, moving away from the legacy system that hosted
IoT Devices Auto‑Login as Admin Open Lateral Paths in Critical Infrastructure
A recent SANS diary entry documented multiple incidents where Internet‑of‑Things (IoT) endpoints—such as smart sensors, cameras, and
Default IoT Admin Passwords Keep Attackers Inside Your Network
A recent SANS diary entry documented several incidents in which IoT devices—cameras, HVAC controllers, and smart sensors—were accessed
Hidden Risks: Proprietary Apps Create Security Blind Spots
A recent Security.StackExchange discussion highlighted how organizations that depend on proprietary software often operate without full visibility into the