Outlook Add‑In Hijack, Wormable IoT Botnet, and AI‑Crafted Malware Threaten Defenders
A wave of malicious Outlook add‑ins surfaced this week, targeting enterprise mailboxes to intercept, modify, and forward messages. The
Lithuania Deploys AI‑Powered Shield Against Deep‑Fake Fraud
Lithuania has unveiled a nationwide anti‑fraud program that pairs new regulations with AI‑driven detection tools to counter the
Romanian Pipeline Operator Conpet Hit by Full-Service Outage After IT Breach
Check Point’s 9 February Threat Intelligence Report details a cyberattack that breached Conpet’s corporate IT infrastructure, Romania’s
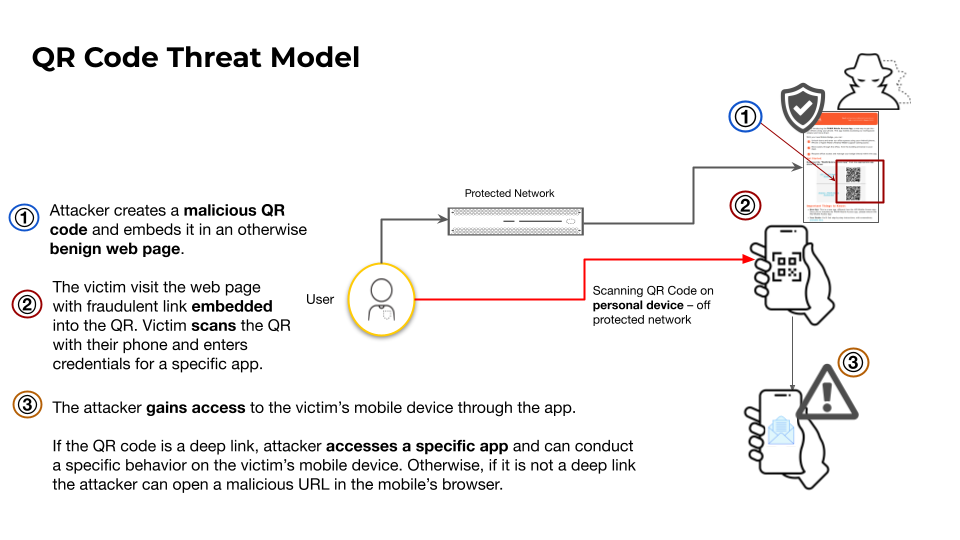
QR Code Phishing Expands Mobile and Web Attack Surface
Threat actors are increasingly embedding malicious URLs in QR codes, allowing them to sidestep traditional network and email filters. When
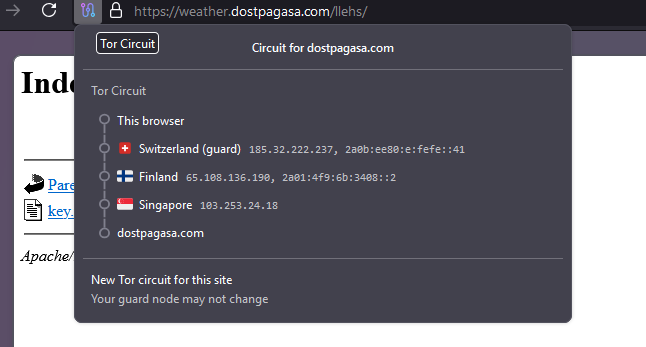
Amaranth‑Dragon Exploits New CVE‑2025‑8088 to Penetrate SE Asian Networks
Check Point’s threat intel team has identified the state‑sponsored group Amaranth‑Dragon actively weaponizing the freshly disclosed CVE‑
VMware's vDefend Lateral Security Automates Micro‑Segmentation for Zero‑Trust Private Clouds
VMware introduced vDefend Lateral Security, a solution that embeds continuous micro‑segmentation and automated threat containment directly into private‑cloud
CrowdStrike Tops Gartner Peer Insights for Cloud‑Native Authentication
CrowdStrike has been named a Customers’ Choice in the 2026 Gartner Peer Insights for User Authentication. The accolade reflects strong
Outlook Add‑In Hijacks Fuel AI‑Generated Malware in Blended Threat Campaigns
A wave of Outlook add‑in hijacks has been observed, with threat actors compromising legitimate Office Store extensions to inject
Lithuania Launches National AI‑Fraud Defense Initiative to Shield E‑Signatures & Health Data
Lithuania’s government has unveiled a €20 million, three‑year program aimed at countering AI‑driven cyber fraud. The effort
Romanian Oil Pipeline Outage Exposes Critical Energy Cyber Weaknesses
On February 9, Check Point’s threat report documented a cyber intrusion against Conpet, Romania’s national oil pipeline operator.