Malicious NuGet Packages Exfiltrate ASP.NET Identity and Install Persistent Backdoors
Security researchers at Socket identified a supply‑chain attack that distributes malicious NuGet packages targeting ASP.NET developers. The packages
AI-Driven Threats Surge: Check Point 2025 Reveals New Weaponization Playbook
Check Point’s 2025 retrospective shows threat actors have moved from experimental use of artificial intelligence to fully integrating it
Claude AI Project Files Weaponized for Remote Code Execution and Token Theft
Threat actors are targeting Claude AI code project files, inserting malicious payloads that execute arbitrary commands on vulnerable hosts and
Threat Actors Reconnaissance Targets BeyondTrust RCE (CVE‑2026‑1731) Before Exploit Release
GreyNoise researchers have identified a wave of coordinated scans aimed at systems running BeyondTrust’s privileged access management service. The
AI Prompt Poisoning Hijacks ‘Summarize with AI’ Buttons to Manipulate Chatbot Answers
Microsoft Defender Security Research uncovered a new “AI Recommendation Poisoning” technique where attackers hide malicious prompts behind the “Summarize with
Six Actively‑Exploited Zero‑Days Included in February 2026 Patch Tuesday
Microsoft’s February 2026 Patch Tuesday released updates for more than 50 flaws, but six of those were zero‑day
Scale SOC Automation Fast with CrowdStrike Falcon Fusion Playbooks
CrowdStrike’s recent blog walks security teams through extending their SOC using Falcon Fusion, the vendor’s native SOAR platform.
AI Summarize Buttons Used for Prompt Poisoning on Compromised Sites
Microsoft Defender Security Research identified a novel attack chain where threat actors embed malicious “Summarize with AI” buttons into compromised
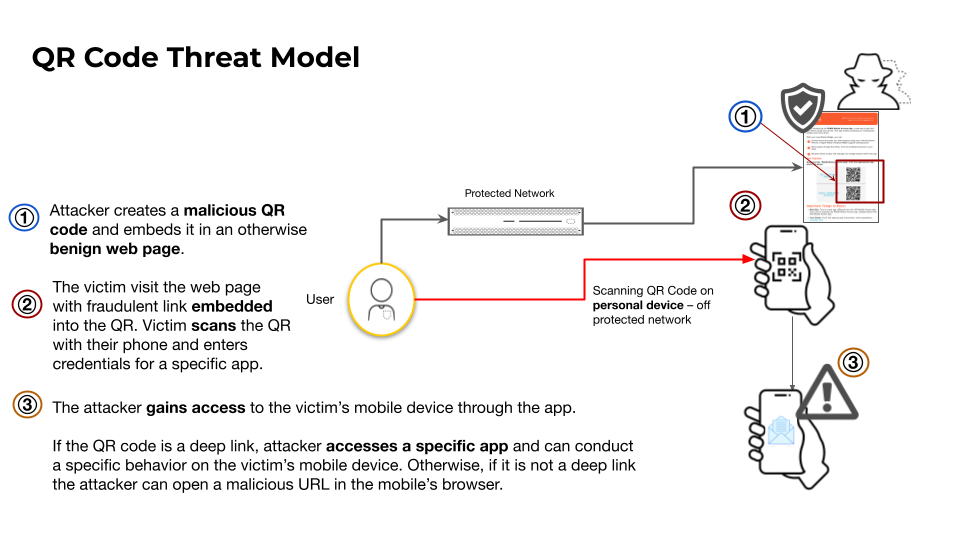
QR Code Phishing Spikes, Targeting Users on Web & Mobile
Palo Alto Networks’ Unit 42 has documented a sharp increase in QR‑code phishing campaigns that direct victims to credential‑
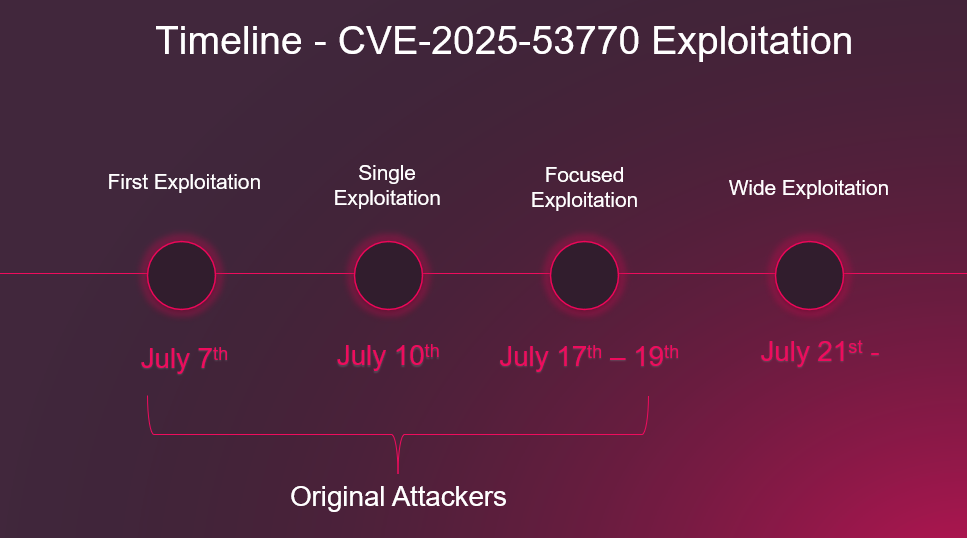
Coordinated Scans Target New BeyondTrust RCE Vulnerability – Exploit Likely Soon
GreyNoise analysts have observed a widespread, credential‑free reconnaissance campaign that is actively probing internet‑exposed BeyondTrust management consoles for