Kimwolf Botnet Grows: Dort Exploits Proxies and I2P for Stealthy C2
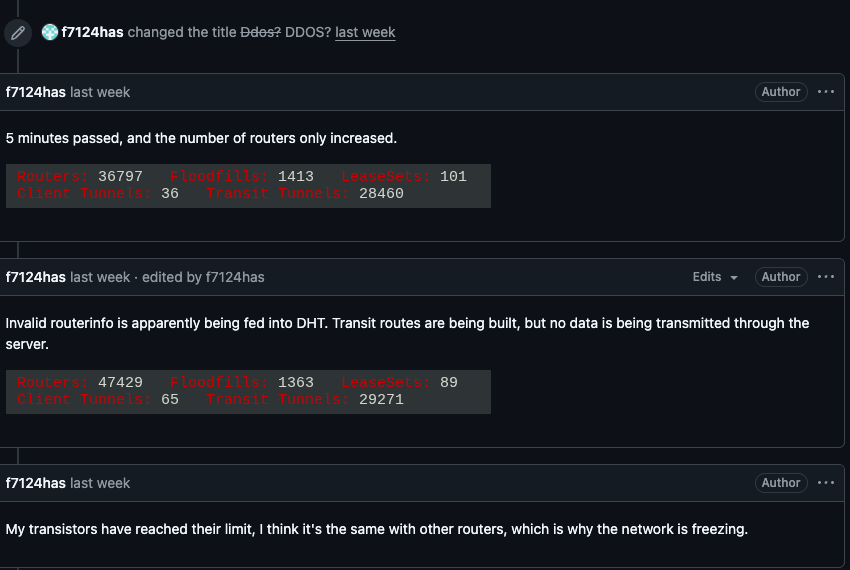
The Kimwolf botnet, now led by the elusive operator known as “Dort,” has surged in size and sophistication. Researchers observed
LummaStealer Returns, Bundled with CastleLoader – New Social‑Engineering Threat
Bitdefender’s latest lab report confirms that the long‑dormant LummaStealer trojan has resurfaced, this time shipped alongside the CastleLoader
AI‑Generated Malware Variants Flood 2026, Eroding Traditional Defenses
CrowdStrike’s 2026 Global Threat Report shows threat actors now leveraging large language models to auto‑create thousands of code
Kimwolf Botnet Moves C2 to I2P, Hiding in IoT Networks
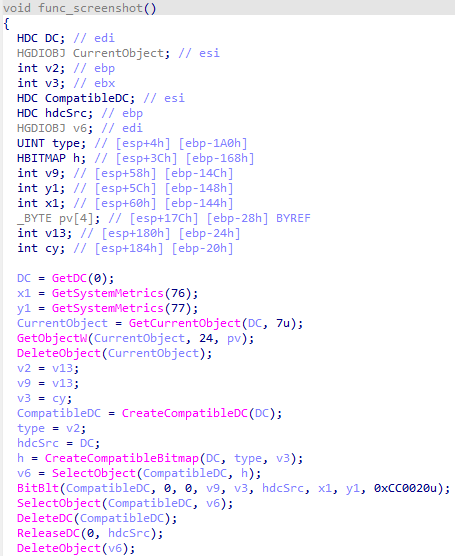
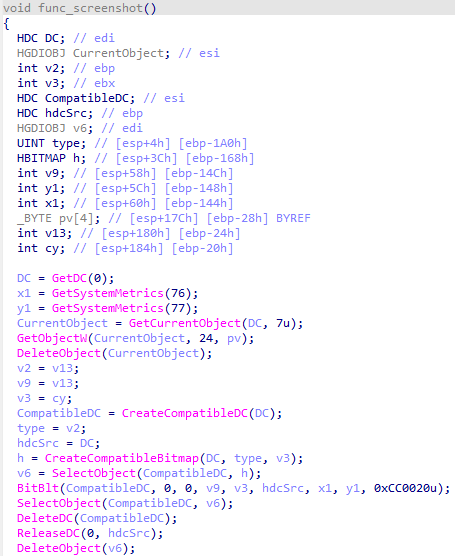
Security researchers have confirmed that the Kimwolf botnet, known for compromising consumer‑grade IoT devices, has migrated its command‑and‑
LummaStealer Teams Up with CastleLoader to Boost Theft and Evade Detection
Bitdefender researchers have identified a resurgence of the LummaStealer credential‑stealer, now being delivered through the CastleLoader modular loader. The
OpenClaw II Unleashes AI‑Powered Reverse Shells and Self‑Evolving Rootkits
The latest VirusTotal deep‑dive on OpenClaw Part II reveals that the malware now incorporates generative‑AI modules to craft
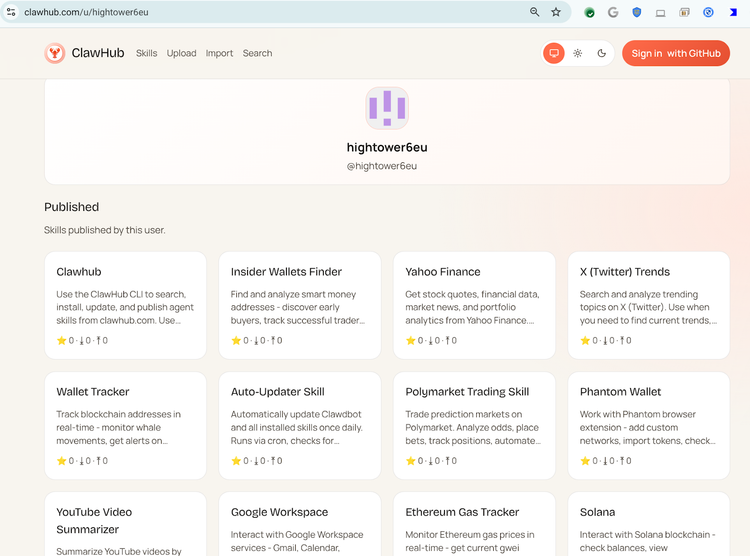
OpenClaw AI Skills Weaponized to Distribute Malware via Automation Tools
VirusTotal researchers have uncovered a campaign in which a prolific threat actor is publishing malicious “skills” on the OpenClaw AI
Manual Data Transfers Turn National‑Security Networks Into Easy Targets
A recent CYBER360 analysis highlighted that numerous national‑security agencies still depend on manual data‑transfer methods—such as USB
Typosquatting Domains Slip Past Filters, Deliver Malware at Scale
Attackers are registering domains that differ by a single character or visual similarity from well‑known brands. These look‑alike
AI-Driven Threats Surge: Generative Models Fuel Malware, Phishing, and Deepfake Attacks
CrowdStrike’s Global Threat Report for 2026 reveals a sharp rise in adversaries exploiting generative AI to automate the creation