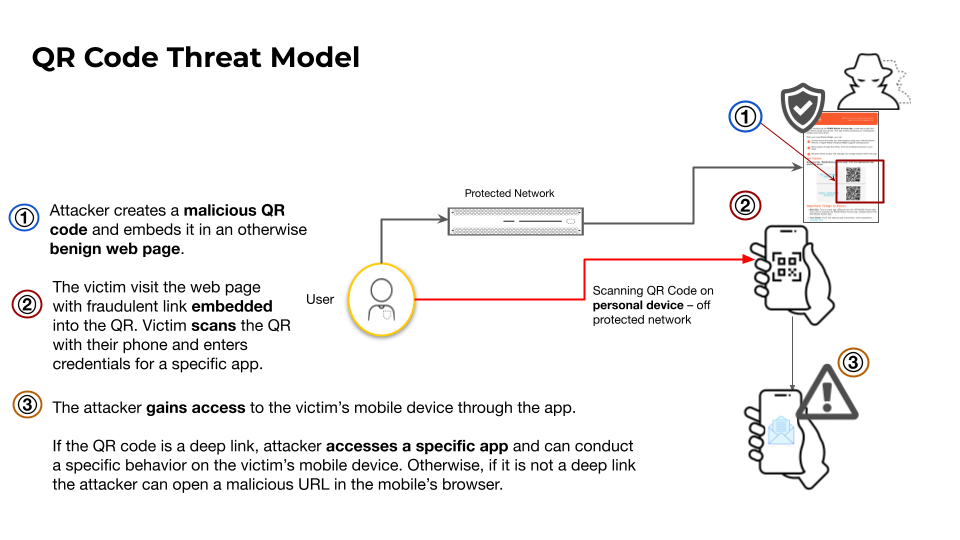
QR Code Phishing Turns Smartphones Into New Attack Vectors
Researchers observed threat actors embedding malicious URLs in QR codes that, when scanned, direct victims to credential‑harvesting webpages or
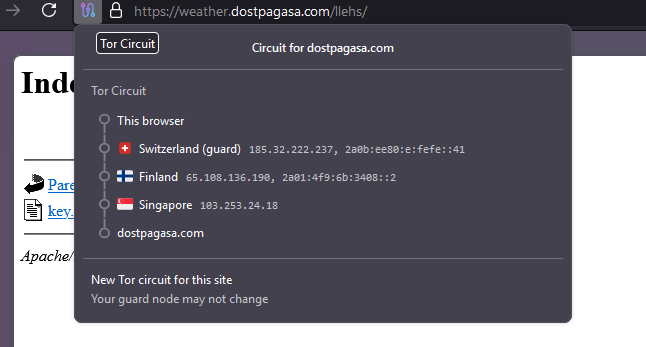
Kimwolf Botnet Hijacks I2P, Boosting Stealthy DDoS Threats
The Kimwolf botnet has started routing its command‑and‑control (C2) traffic through the I2P anonymity network. By embedding its
VMware vDefend Lateral Security Boosts Zero‑Trust in Private Clouds
VMware has introduced vDefend Lateral Security, an AI‑driven module that monitors and validates every inter‑workload communication within private
Nation‑State Hijacks Notepad++ Updates, Threatening Developer Supply Chains
Palo Alto Networks’ Unit 42 uncovered a supply‑chain attack on the popular Notepad++ editor, where a nation‑state actor
Conpet Oil Pipeline Hit by Cyberattack, Exposing Energy Critical Infrastructure Gaps
Romania’s national oil pipeline operator, Conpet, suffered a cyber intrusion that crippled its internal IT environment and rendered its
AI‑Driven Prompt RCE and 0‑Click Claude Exploit Spark New Threat Wave
The latest ThreatsDay Bulletin reports a coordinated surge of AI‑powered attacks. Researchers uncovered a prompt‑injection remote code execution
Amaranth-Dragon Leverages CVE‑2025‑8088 to Target Southeast Asian Networks
Checkpoint researchers have linked the state‑aligned threat group Amaranth‑Dragon to active exploitation of the newly disclosed CVE‑2025‑
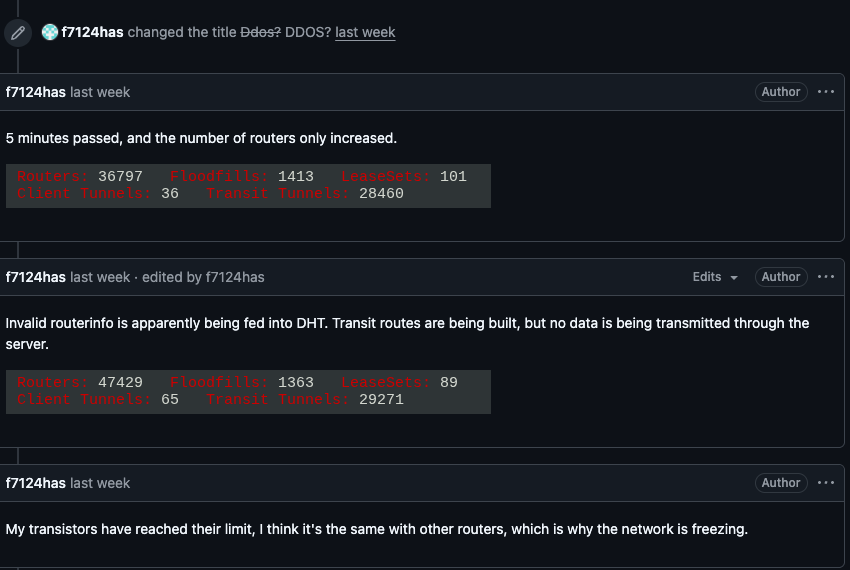
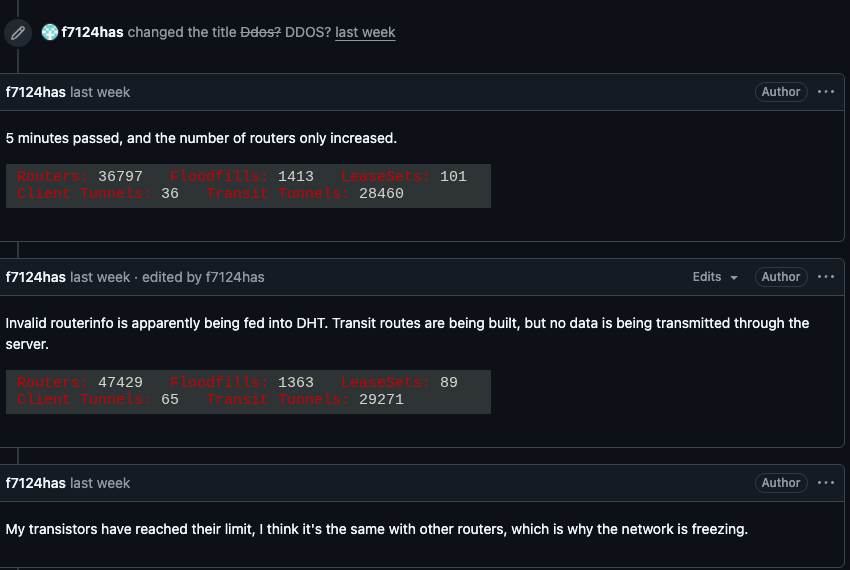
Kimwolf Botnet Weaponizes I2P, Flooding Anonymity Network with Massive Traffic
The Kimwolf botnet has begun abusing the I2P anonymity network’s open routing architecture to inject a torrent of unwanted
Apple Issues Emergency Patch for Actively‑Exploited dyld Zero‑Day (CVE‑2026‑20700)
Apple released emergency updates for iOS, macOS, iPadOS, watchOS, and tvOS that fix a critical dyld memory‑corruption flaw (CVE‑
Muddled Libra Leverages AI to Automate Phishing and Cloud Intrusions
Unit42’s latest investigation uncovered that the Muddled Libra ransomware group has embedded artificial‑intelligence models into its operational playbook.