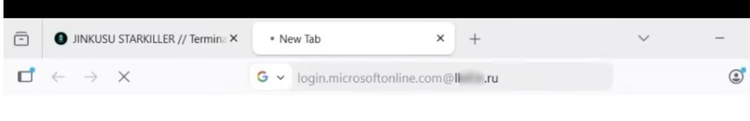
Starkiller Phishing Service Mirrors Real Logins, Skips MFA and Harvests Tokens
KrebsOnSecurity exposed a new phishing‑as‑a‑service platform dubbed “Starkiller” that routes victims through live, unmodified login pages of
CrowdStrike Wins Gartner Choice for Unified Auth & EDR – A Defender’s Edge
CrowdStrike was named a Gartner Customers’ Choice in the 2026 Peer Insights Voice of the Customer for User Authentication. The
Student Loan Servicer Leak: 2.5M Records Exposed via Misconfigured Cloud Bucket
A major student loan servicer suffered a data breach that publicly exposed the personal and financial details of roughly 2.
Password Managers Exposed: New Vulnerabilities Threaten Credential Vaults
The Register’s recent probe uncovered critical bugs in several popular password‑manager apps, including insecure local storage, weak encryption
CrowdStrike Wins Gartner Customer’s Choice, Patches Six Zero‑Day Auth Flaws
CrowdStrike has been named a Gartner Peer Insights “Customer’s Choice” for its user authentication suite, a distinction that reflects
Amaranth‑Dragon Exploits New CVE‑2025‑8088 to Penetrate SE Asian Networks
Check Point’s threat intel team has identified the state‑sponsored group Amaranth‑Dragon actively weaponizing the freshly disclosed CVE‑
Amaranth‑Dragon Exploits CVE‑2025‑8088 to Target SE Asian Critical Infrastructure
Check Point Research has identified the APT group Amaranth‑Dragon actively weaponizing the newly disclosed CVE‑2025‑8088 flaw. The
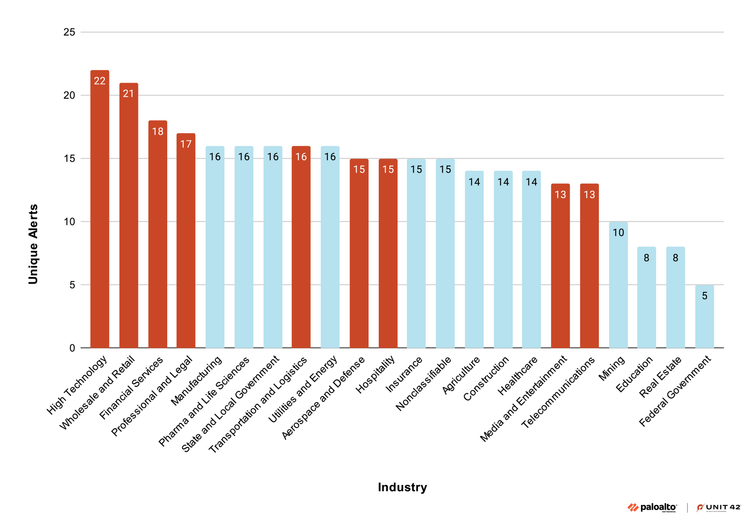
Turn Cloud Logs into Threat Intel: Unit42’s New Detection Playbook
Unit42’s latest research shows how defenders can repurpose native cloud logs—such as AWS CloudTrail and Azure Activity Logs—