AI‑Powered Scans Target Misconfigured FortiGate Firewalls Across Enterprises
A threat group is leveraging AI‑enhanced tools to automatically discover internet‑exposed FortiGate appliances. The bots probe for default
Unpatched Web Flaw Lets Hackers Steal Data of 2.5M Student Loan Borrowers
A threat‑actor group compromised a leading student loan servicer by exploiting a known but unpatched web application vulnerability. The
Manual Data Transfers Turn National‑Security Networks Into Easy Targets
A recent CYBER360 analysis highlighted that numerous national‑security agencies still depend on manual data‑transfer methods—such as USB
Typosquatting Domains Slip Past Filters, Deliver Malware at Scale
Attackers are registering domains that differ by a single character or visual similarity from well‑known brands. These look‑alike
AI-Driven Threats Surge: Generative Models Fuel Malware, Phishing, and Deepfake Attacks
CrowdStrike’s Global Threat Report for 2026 reveals a sharp rise in adversaries exploiting generative AI to automate the creation
Edge‑First OT Security Cuts Dwell Time with AI‑Powered Light Agents
Unit42 has published a new OT edge security model that moves threat detection from central SCADA servers to the devices
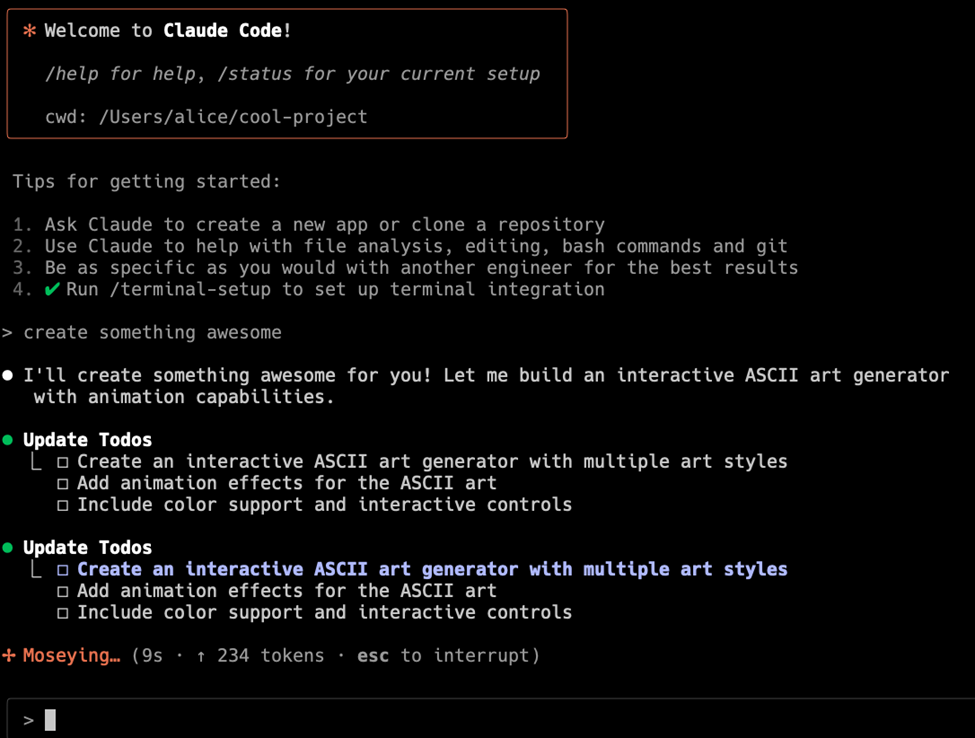
Claude AI Project Files Weaponized for Remote Code Execution and Token Theft
Threat actors are targeting Claude AI code project files, inserting malicious payloads that execute arbitrary commands on vulnerable hosts and
Threat Actors Reconnaissance Targets BeyondTrust RCE (CVE‑2026‑1731) Before Exploit Release
GreyNoise researchers have identified a wave of coordinated scans aimed at systems running BeyondTrust’s privileged access management service. The
Student Loan Servicer Breach Leaks 2.5M Records via Compromised API
A major student loan servicer suffered a data breach that exposed the personal and financial information of roughly 2.5
AI Prompt Poisoning Hijacks ‘Summarize with AI’ Buttons to Manipulate Chatbot Answers
Microsoft Defender Security Research uncovered a new “AI Recommendation Poisoning” technique where attackers hide malicious prompts behind the “Summarize with