Romanian Oil Pipeline Outage Exposes Critical Energy Cyber Weaknesses
On February 9, Check Point’s threat report documented a cyber intrusion against Conpet, Romania’s national oil pipeline operator.
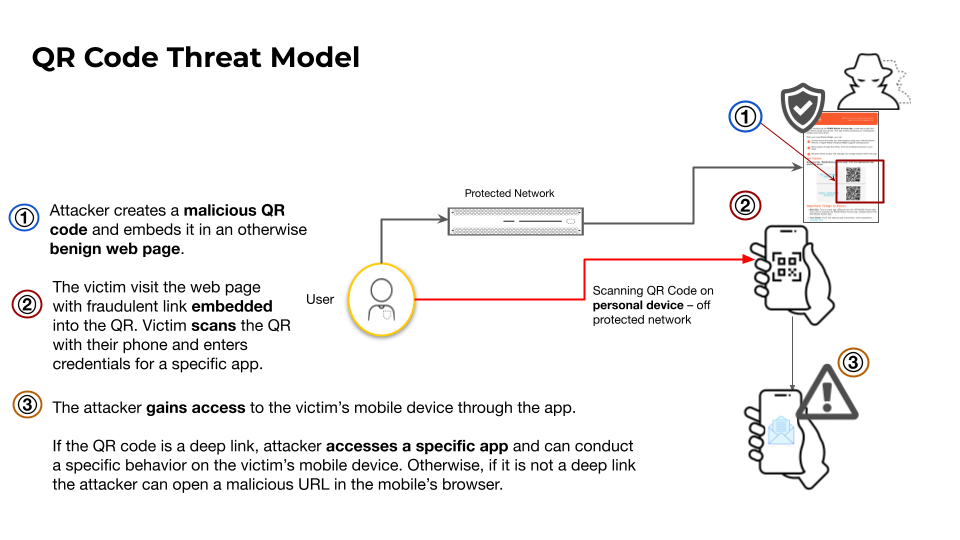
QR Code Phishing Turns Smartphones Into New Attack Vectors
Researchers observed threat actors embedding malicious URLs in QR codes that, when scanned, direct victims to credential‑harvesting webpages or
Amaranth‑Dragon Exploits CVE‑2025‑8088 in SE Asian Supply‑Chain Attack
Check Point researchers identified that the APT‑41 affiliated group, operating under the name Amaranth‑Dragon, weaponized the recently disclosed
Spike in Scans Targets New BeyondTrust RCE Vulnerability, Threat Actors Reconnaissance Rising
GreyNoise has observed a sharp increase in scanning traffic aimed at the newly disclosed CVE‑2026‑1731 remote code execution
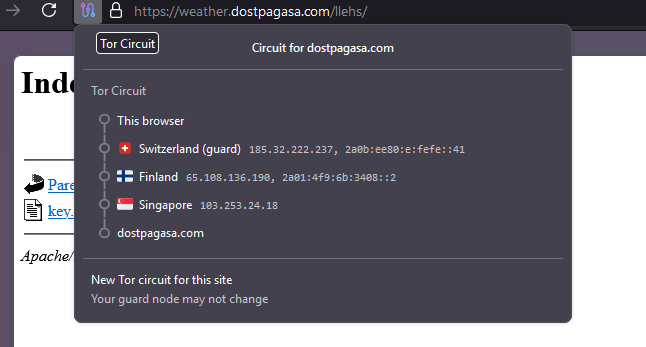
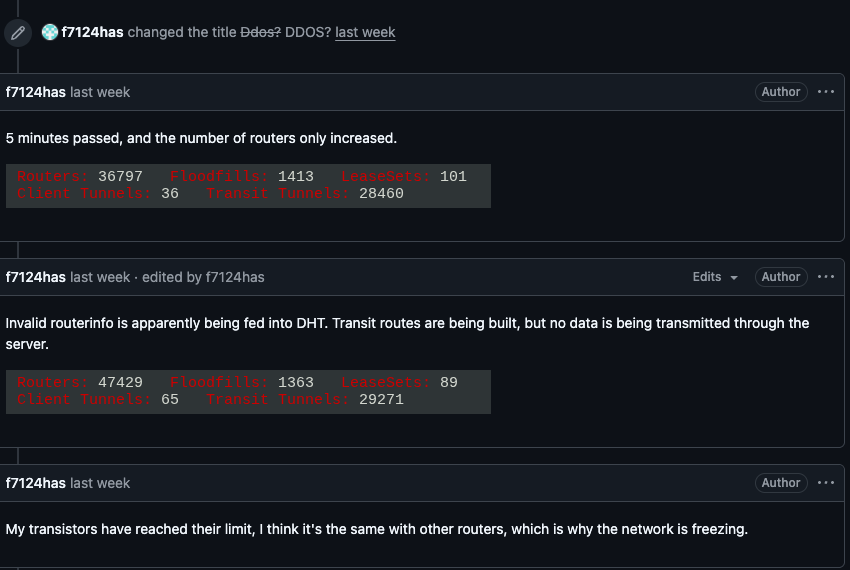
Kimwolf Botnet Hijacks I2P, Boosting Stealthy DDoS Threats
The Kimwolf botnet has started routing its command‑and‑control (C2) traffic through the I2P anonymity network. By embedding its
AI-Driven Zero Trust Cuts Manual Policy Work, Boosts Defender Efficiency
VMware’s latest blog details a new AI engine that ingests user and device behavior, contextual threat intelligence, and existing
Meta on Trial: Platform Safety Scrutinized Over Child Exploitation Allegations
A federal jury is hearing a lawsuit that accuses Meta’s family of apps—particularly Facebook and Instagram—of facilitating
VMware vDefend Lateral Security Boosts Zero‑Trust in Private Clouds
VMware has introduced vDefend Lateral Security, an AI‑driven module that monitors and validates every inter‑workload communication within private
Falcon Fusion SOAR Accelerates SOC Automation and Cuts Response Time
CrowdStrike unveiled Falcon Fusion SOAR, a low‑code platform that lets security operations centers stitch together alerts from disparate security
CrowdStrike’s Human‑AI Loop Accelerates Zero‑Day Detection and Response
CrowdStrike disclosed a “human‑AI feedback loop” in which threat analysts continuously inject contextual insights—such as tactics, techniques, and