Strategic Threat Landscape Reveals AI‑Accelerated Attacks, Integration Gains, and Critical Zero‑Day Gaps
Good morning, March 8 2026 – here are the top cyber and AI threats you need to act on.
Today's headlines
- GreyNoise data now powers CrowdStrike Falcon for real‑time malicious‑IP blocking.
- OpenAI’s Codex Security flags over 10,000 high‑severity code flaws in 1.2 M commits.
- GoAnywhere MFT zero‑day (CVSS 10.0) bypasses perimeter firewalls, exposing critical data transfers.
- AI agents are automating reconnaissance and phishing for state‑sponsored groups.
- Iran‑linked campaign compromises IP cameras to gain battlefield visual intelligence.
1️⃣ GreyNoise Intelligence Embedded in CrowdStrike Falcon Enhances Threat Context
Key Points:
- Real‑time blocklists filter noisy internet scans
- Adds malicious IP context to incidents
- Supports SOC efficiency and asset detection
- Enables vulnerability prioritization via exploitation trends
Description:
GreyNoise announced its intelligence is now available across the CrowdStrike Falcon platform. The integration delivers fully configurable, real‑time blocklists that suppress low‑severity alerts from mass scanners, enriches incidents with malicious‑IP reputation, and provides early warnings on emerging CVE exploitation, helping security teams focus on genuine threats.
Why It Matters:
By coupling GreyNoise data with Falcon’s detection capabilities, organizations can reduce alert fatigue, accelerate response times, and prioritize remediation based on active exploitation trends, strengthening overall cyber resilience.
2️⃣ OpenAI Codex Security Scans 1.2 M Commits, Flags 10,561 Critical Flaws

Key Points:
- AI agent identifies high‑severity vulnerabilities missed by traditional tools
- Provides contextual fixes to reduce noise
- Available in research preview for ChatGPT Pro/Enterprise
- Free usage for one month
Description:
OpenAI introduced Codex Security, an AI‑driven security assistant that examined 1.2 million code commits and uncovered over ten thousand high‑severity issues. The tool leverages deep project context to surface complex bugs, automatically suggests remediation, and aims to minimize false positives for developers.
Why It Matters:
Early detection of critical code flaws directly within development pipelines lowers the risk of exploitable defects reaching production, enabling CISOs to embed security controls earlier and reduce potential breach impact.
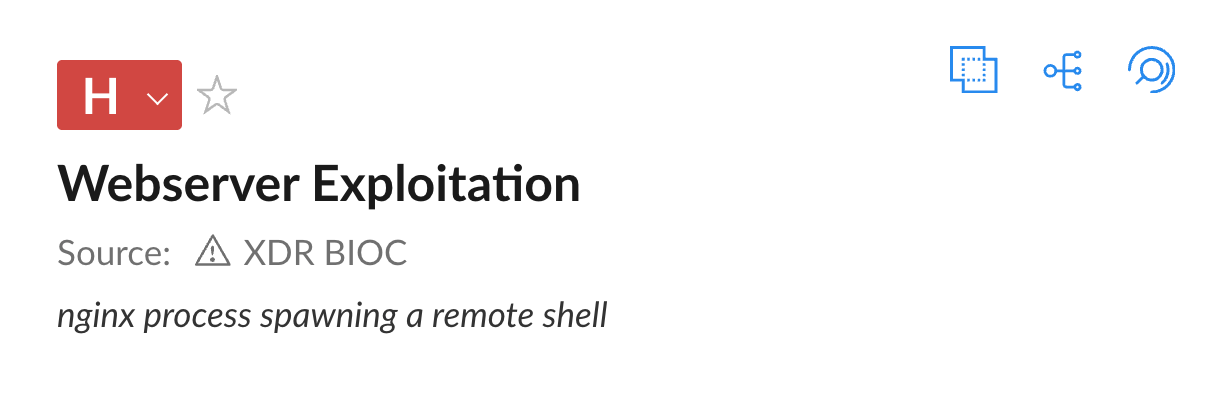
3️⃣ GoAnywhere MFT Zero‑Day Demonstrates Limits of Perimeter‑Only Defenses

Key Points:
- CVE‑2025‑10035 is a critical deserialization bug (CVSS 10.0)
- Exploited by Storm‑1175 in September 2025
- Bypasses traditional firewalls and network segmentation
- Highlights need for application‑layer monitoring
Description:
VMware security researchers detailed how the GoAnywhere Managed File Transfer (MFT) zero‑day vulnerability, exploited by the Storm‑1175 threat actor, evaded perimeter firewalls and caused severe data compromise. The CVE, scored at the maximum severity, remained undisclosed until active exploitation was observed.
Why It Matters:
Relying solely on perimeter controls leaves enterprises exposed to sophisticated application exploits; organizations must adopt deep packet inspection, runtime monitoring, and rapid vulnerability patching to protect critical data transfers.
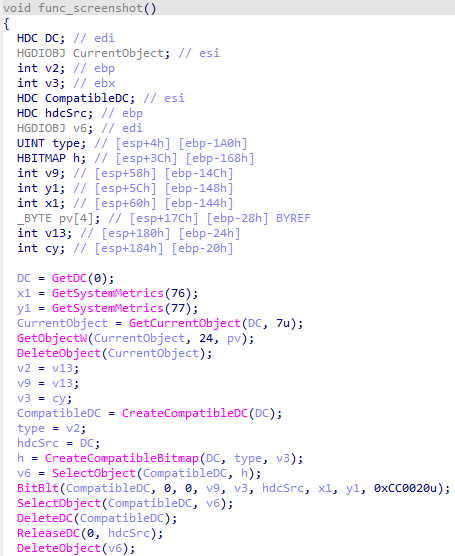
4️⃣ LummaStealer Resurfaces Paired with CastleLoader Malware
Key Points:
- Combines credential theft with modular loader capabilities
- Adapts delivery to mimic legitimate user behavior
- Uses fresh IoCs posted on GitHub
- Targets Windows users via social‑engineering lures
- Increases post‑compromise persistence
Description:
Bitdefender researchers reported that the LummaStealer infostealer has re‑emerged alongside the CastleLoader droploader, forming a more versatile threat chain. The duo employs sophisticated social‑engineering and leverages legitimate‑looking processes to evade detection while exfiltrating credentials and deploying additional payloads.
Why It Matters:
The evolution underscores the need for behavioral analytics and strict endpoint monitoring, as traditional signature‑based defenses may miss these blended threats, raising the risk of credential compromise across enterprises.
5️⃣ AI Agents Accelerate Attack Infrastructure for State‑Sponsored Threat Actors

Key Points:
- North Korean groups using LLMs to automate reconnaissance
- AI bots handle credential stuffing, phishing content generation
- Reduces manual labor and speeds up campaign scaling
- Highlights emergence of AI‑augmented cyber‑espionage
Description:
A report from The Register reveals that advanced AI agents are now employed by malicious actors, including North Korean units, to manage repetitive tasks such as scanning, credential spraying, and phishing material creation. These agents free human operators to focus on strategic planning.
Why It Matters:
AI‑assisted automation raises the volume and sophistication of attacks, compelling defenders to adopt AI‑driven detection and harden supply‑chain processes to mitigate automated threat operations.
6️⃣ Microsoft Details How Threat Actors Operationalize AI in Attacks

Key Points:
- Threat actors embed generative models to craft malware evasion
- AI used for automated vulnerability discovery
- Integrates with existing C2 frameworks for adaptive behavior
- Microsoft provides guidance on detection
Description:
Microsoft’s security blog outlines the tradecraft where adversaries leverage artificial intelligence to generate polymorphic code, automate exploit research, and dynamically adapt command‑and‑control communications. The post includes recommendations for monitoring AI‑related artifacts.
Why It Matters:
Understanding AI‑driven attack techniques enables security teams to develop counter‑measure baselines, adjust threat‑model assumptions, and invest in detection tools that can spot AI‑generated anomalies.
7️⃣ Falcon Next‑Gen SIEM Simplifies Sensor‑Native Log Collection
Key Points:
- Eliminates agents for log ingestion via native sensors
- Accelerates SOC onboarding by 40% in trials
- Provides unified visibility across workloads
- Supports scaling of automated response playbooks
Description:
CrowdStrike announced that its Falcon Next‑Gen SIEM now offers sensor‑native log collection, removing the need for separate log shippers. Early adopters reported faster deployment timelines and improved data fidelity for threat hunting and automation.
Why It Matters:
Streamlined log onboarding reduces operational overhead and accelerates the time to detect threats, allowing security leadership to achieve higher ROI on SIEM investments and strengthen incident response.
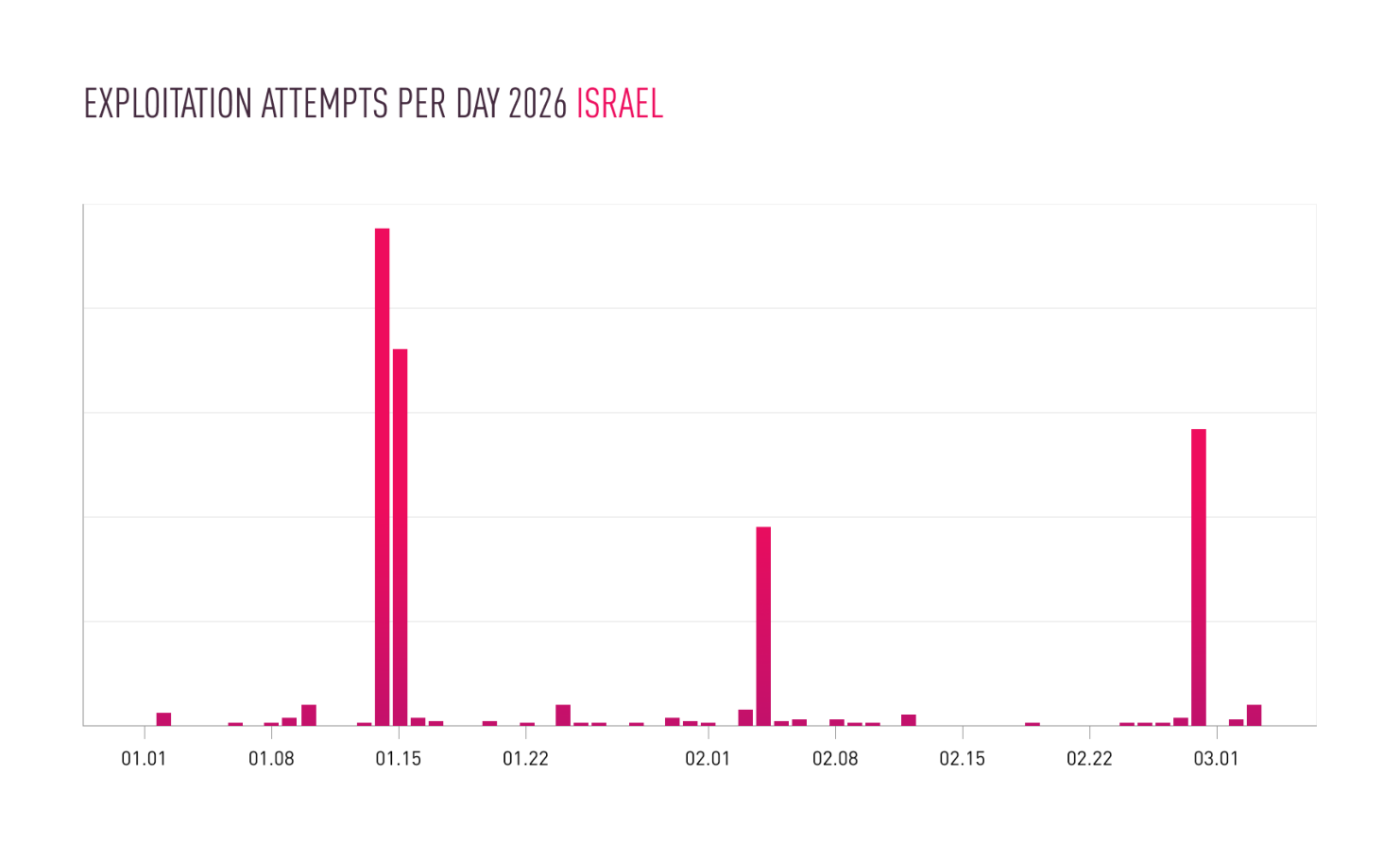
8️⃣ Iranian Actors Intensify Attacks on IP Cameras Amid Regional Conflict
Key Points:
- Surge in exploitation of insecure IoT video feeds
- Aligns with physical warfare tactics in the Middle East
- Uses credential‑brute forcing and default passwords
- Enables real‑time reconnaissance of battlefield zones
- Highlights supply‑chain risk for surveillance vendors
Description:
Check Point research identified a campaign where Iranian‑affiliated groups systematically compromise internet‑connected IP cameras, leveraging them for visual intelligence that complements kinetic operations in the region. The attackers exploit default credentials and unpatched firmware.
Why It Matters:
Compromised cameras can leak sensitive location data and be weaponized for propaganda, urging organizations to enforce strong authentication, regular patching, and network segmentation of IoT assets.
9️⃣ Fake Google Meet Update Delivers Malware with One Click
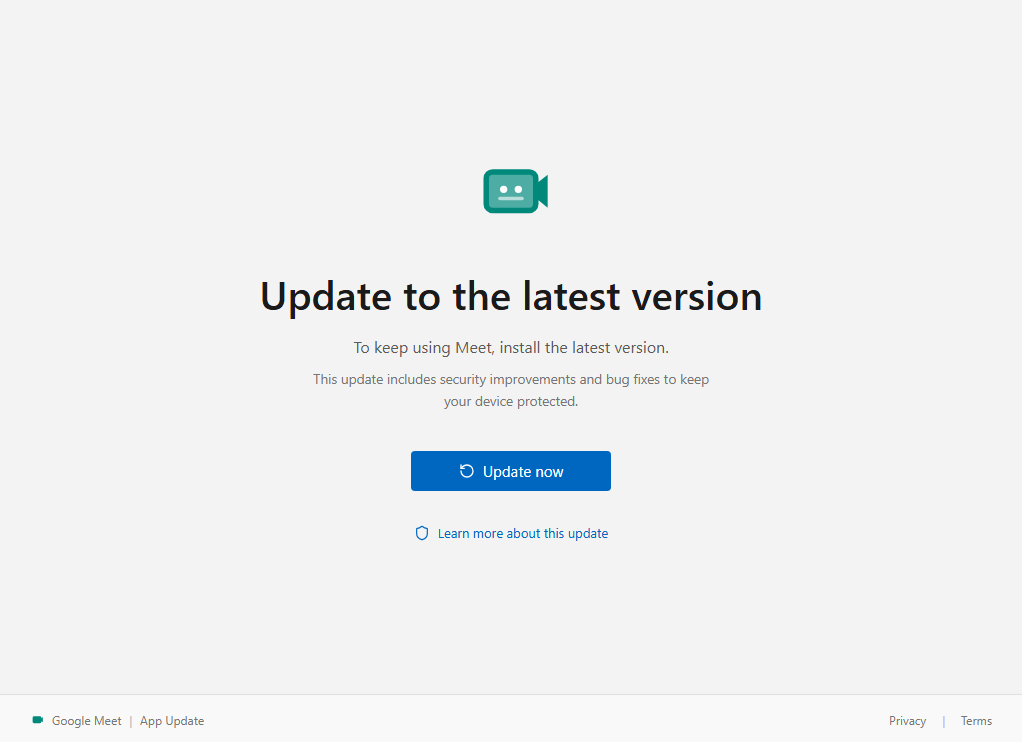
Key Points:
- Attackers distribute a malicious installer masquerading as a Meet update
- Execution grants attacker remote control of the victim PC
- Uses social engineering targeting remote‑work users
- Detected by Malwarebytes in early March 2026
- Leads to credential theft and ransomware deployment
Description:
Malwarebytes reported a new phishing campaign that tricks users into downloading a counterfeit Google Meet update executable. Once run, the payload installs a remote‑access trojan, giving adversaries full system control.
Why It Matters:
The ease of infection stresses the importance of user awareness training, application whitelisting, and verification of software sources to prevent credential and system compromise in hybrid workplaces.
🔟 Unit 42 Uncovers Long‑Term CL‑UNK‑1068 Campaign Targeting Critical Sectors
Key Points:
- Activity observed since 2020 across South, Southeast, East Asia
- Targets aviation, energy, government, pharma, telecom
- Uses DLL sideloading, fast reverse proxy, ScanPortPlus
- Operates under stealth with custom malware
- Highlights gap in regional threat‑intel sharing
Description:
Palo Alto Networks’ Unit 42 detailed a previously undocumented operation, designated CL‑UNK‑1068, that has been compromising high‑value organizations for years. The campaign employs sophisticated techniques such as DLL sideloading and custom reverse proxies to maintain persistence and exfiltrate data.
Why It Matters:
Awareness of this persistent threat enables CISOs to audit vulnerable supply‑chain components, strengthen detection of anomalous DLL loads, and collaborate internationally to mitigate a long‑standing espionage effort.
Stay vigilant and prioritize proactive defenses.
Member discussion