Strategic Risk Exposure from Integrated Threat Intelligence, AI‑Powered Scanners, and State‑Sponsored Attacks

Hello, March 16 2026 – Here’s your daily executive briefing on critical cyber and AI threats.
Today's headlines
- GreyNoise ties into Google SecOps to cut noise and accelerate response.
- Security validation tools must unify to match multi‑vector attacker tactics.
- Cloudflare launches AI‑driven account abuse protection and API scanner.
- Iran‑backed hackers deploy wiper malware against a major medtech firm.
- OWASP retires its Meetup platform, shifting community engagement.
- Student loan data breach exposes 2.5 million records.
- VirusTotal unveils OpenClaw AI techniques for advanced malware.
- Active network telescopes reveal large‑scale React2Shell exploitation.
- ISC Stormcast highlights rising SSH/Telnet scanning trends.
- Malwarebytes weekly roundup tracks notable industry developments.
1️⃣ GreyNoise Boosts Google SecOps Detection
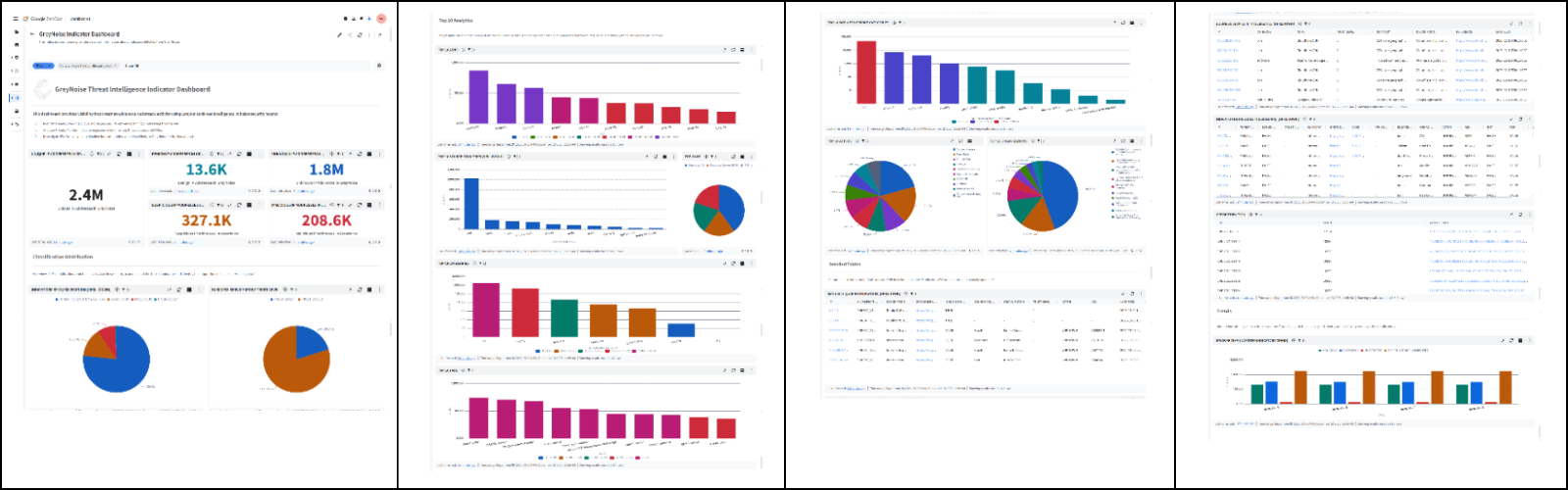
Key Points:
- Real‑time blocklists block malicious IPs before they reach assets.
- Contextual enrichment reduces false positives from internet scanners.
- Integrates with SIEM, SOAR, TIP, and firewall solutions.
- Improves SOC efficiency and threat‑hunting speed.
Description:
GreyNoise announced new integrations that feed its intelligence into Google SecOps, providing fully configurable blocklists and enriched incident context. The partnership aims to filter noisy traffic, prioritize genuine threats, and accelerate investigation cycles for security teams.
Why It Matters:
By embedding GreyNoise data directly into Google SecOps, organizations can cut alert fatigue, focus on high‑impact incidents, and reduce dwell time. Executives gain clearer visibility into active exploitation trends, supporting risk‑based decision making and resource allocation.
2️⃣ Validation Stack Needs Unified Agentic Approach

Key Points:
- Current tools operate in silos: BAS, pen‑testing, scanners.
- Attackers chain identity leaks, misconfigs, and unpatched flaws.
- Agentic validation proposes coordinated, automated risk correlation.
- Improves coverage across the full attack surface.
Description:
The Hacker News discusses the emerging concept of agentic security validation, highlighting how fragmented tools fail to capture complex, chained attacker behaviors. A unified framework would allow continuous, automated correlation of findings across BAS, pentesting, and vulnerability scanning platforms.
Why It Matters:
CISOs can achieve comprehensive exposure visibility, preventing gaps that sophisticated threat actors exploit. An agentic approach drives more efficient remediation cycles and aligns security validation with business risk tolerance.
3️⃣ Cloudflare Introduces AI Account Abuse Shield

Key Points:
- Protects against bot and human‑driven fraudulent login attempts.
- Leverages AI to identify abusive patterns in real time.
- Adds 14 new datasets for a holistic network view.
- Includes a stateful API vulnerability scanner.
Description:
Cloudflare launched Account Abuse Protection, a service combining AI‑driven detection of malicious login activity with an expanded Log Explorer offering 14 additional datasets. The rollout also features a new web and API vulnerability scanner that builds call graphs to spot logic flaws missed by traditional tools.
Why It Matters:
Enterprises can now block credential stuffing, account takeover, and API abuse before they impact users, reducing financial loss and brand damage. The integrated scanner helps secure modern application interfaces, a growing attack surface for many organizations.
4️⃣ Iran‑Backed Wiper Targets MedTech Giant
Key Points:
- Wiper malware allegedly deployed against Stryker's systems.
- Attributed to Iran‑aligned threat group.
- Potential disruption of critical medical device operations.
- Highlights rising state‑sponsored sabotage in healthcare.
Description:
KrebsOnSecurity reports that an Iran‑backed hacking group claimed responsibility for a wiper attack on Stryker, a leading medical technology company. The malware aimed to erase data and render equipment unusable, raising concerns about patient safety and operational continuity.
Why It Matters:
Healthcare providers must prioritize robust backup, segmentation, and detection capabilities to mitigate nation‑state sabotage. Failure to do so could jeopardize patient care, trigger regulatory penalties, and damage corporate reputation.
5️⃣ OWASP Retires Meetup Platform
Key Points:
- OWL’s community meetup site is being decommissioned.
- Focus shifts to newer collaboration channels and virtual events.
- Encourages members to transition to OWASP Discord and webinars.
- Maintains commitment to open‑source security advocacy.
Description:
The OWASP Foundation announced the retirement of its Meetup platform, citing a strategic move toward more modern, scalable community engagement tools such as Discord, virtual conferences, and recorded webinars. The change aims to streamline communication and broaden participation.
Why It Matters:
Security professionals rely on OWASP resources for best practices; ensuring accessible, up‑to‑date venues for knowledge sharing helps maintain industry standards and supports continuous improvement in software security.
6️⃣ Student Loan Data Breach Exposes 2.5 M Records

Key Points:
- Attackers accessed personal data of 2.5 million borrowers.
- Compromised information includes SSNs, loan balances, and contact details.
- Data was likely obtained through a misconfigured cloud storage bucket.
- Regulatory investigation and notification processes underway.
Description:
Threatpost details a breach affecting a major student loan servicer, where attackers exposed the personally identifiable information of 2.5 million individuals. The breach appears to stem from an exposed cloud asset, underscoring the risks of inadequate configuration management.
Why It Matters:
Financial institutions must enforce strict cloud security controls and continuous monitoring. Failure to protect sensitive borrower data can result in identity theft, legal liabilities, and loss of consumer trust.
7️⃣ VirusTotal Unveils OpenClaw AI Malware Techniques
Key Points:
- OpenClaw demonstrates reverse shells, semantic worms, cognitive rootkits.
- Uses AI to automate infection chain creation.
- Highlights emerging threat of AI‑generated malware.
- Provides detection signatures and analysis guidelines.
Description:
VirusTotal’s blog series on OpenClaw explores advanced AI‑driven malware techniques, including reverse shells, semantic worms, and cognitive rootkits. The research showcases how machine learning can automate the creation of sophisticated infection vectors that evade traditional defenses.
Why It Matters:
Security teams must adapt detection strategies to counter AI‑generated threats, incorporating behavior‑based analytics and threat‑intelligence feeds that recognize novel code patterns before they proliferate.
8️⃣ Active Telescope Maps React2Shell Exploitation

Key Points:
- Large‑scale measurement of React2Shell attacks using network telescope.
- Identifies geographic hotspots and target industries.
- Offers insight into attacker tactics and payload delivery.
- Data supports improved IDS signatures and mitigation.
Description:
An arXiv pre‑print presents a study leveraging an active network telescope to capture and analyze internet‑scale exploitation of the React2Shell vulnerability. The researchers charted attack origins, victim profiles, and temporal trends.
Why It Matters:
Understanding the breadth of React2Shell activity enables defenders to prioritize patching, refine intrusion detection rules, and allocate resources to the most impacted sectors, reducing overall exposure.
9️⃣ ISC Stormcast Highlights Rising SSH Scans
Key Points:
- Weekly Stormcast report shows increased SSH/Telnet scanning.
- Attackers target exposed services on IoT and cloud hosts.
- Correlates scan spikes with known threat actor campaigns.
- Recommends network segmentation and strict access controls.
Description:
The Internet Storm Center’s latest Stormcast podcast episode details a surge in SSH and Telnet scanning activity observed across global sensors. The analysis links the uptick to ongoing campaigns by opportunistic threat groups.
Why It Matters:
Enterprises should enforce strong authentication, limit exposure of management ports, and monitor for anomalous scan traffic to preempt credential‑stuffing and brute‑force attacks.
🔟 Malwarebytes Weekly Recap Surveys Emerging Threats
Key Points:
- Summarizes latest malware trends and vendor product comparisons.
- Highlights new ransomware variants and phishing campaigns.
- Provides actionable advice for endpoint protection.
- Encourages adoption of layered security architectures.
Description:
Malwarebytes released its weekly security roundup covering notable malware developments, product performance insights, and best‑practice recommendations for endpoint defenses. The article also touches on emerging AI‑enhanced threats.
Why It Matters:
Staying informed of current adversary tactics helps security leaders refine defense postures, allocate budgeting effectively, and maintain resilience against fast‑evolving threats.
Stay vigilant and keep your defenses ahead of the curve.






Member discussion