Strategic Risk Exposure and Resilience Insights Across Threat Intelligence, Exploits, and AI Weaponization

Good morning, March 16 2026 – here’s the latest intelligence briefing for your security leadership.
Today's headlines
- GreyNoise adds context layers to Google SecOps and CrowdStrike defenses.
- Malicious actors exploit ClickFix to spread Remcos RAT in targeted campaigns.
- Google addresses two actively exploited Chrome vulnerabilities.
- Cloudflare’s new protection curtails account abuse by bots and humans.
- OpenClaw AI skills are being weaponized to automate sophisticated malware delivery.
1️⃣ GreyNoise Enhances Google SecOps with Real‑Time Threat Context
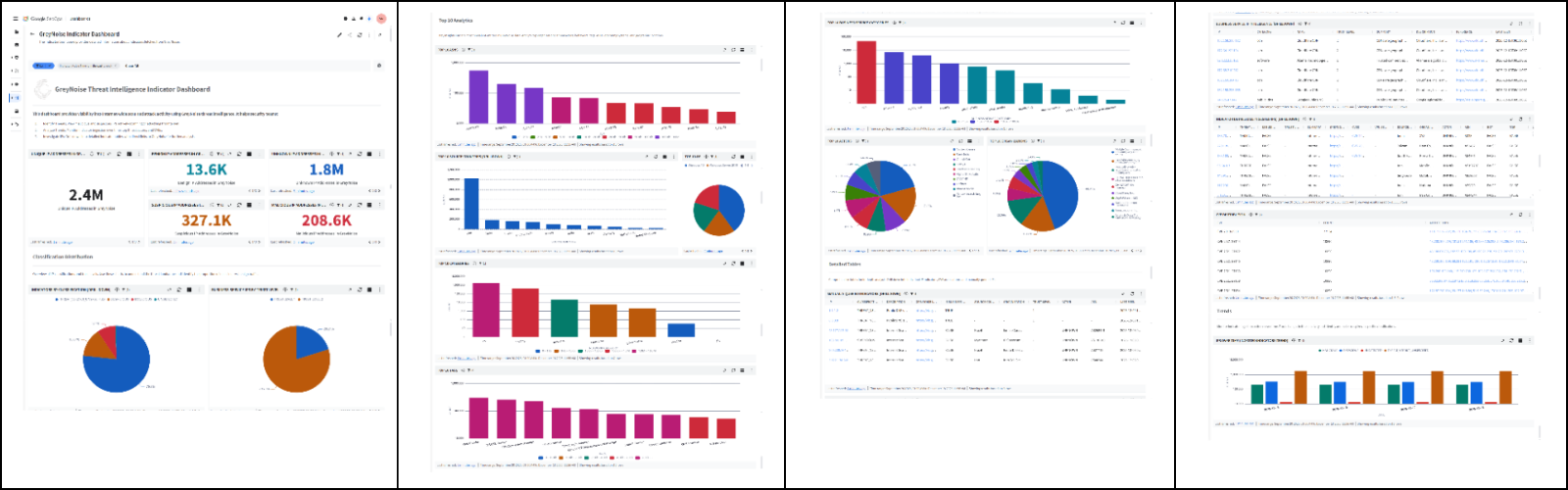
Key Points:
- Integrates GreyNoise IP reputation data directly into Google Cloud security tools.
- Enables automatic filtering of noisy internet scan traffic.
- Provides enriched alerts for compromised asset detection and vulnerability prioritization.
Description:
GreyNoise announced a new integration that feeds its internet background noise intelligence into Google SecOps workflows. The partnership allows security teams to automatically block or deprioritize traffic from IPs identified as benign scanners, while highlighting truly malicious activity for faster incident response.
Why It Matters:
For organizations using Google Cloud, the integration reduces alert fatigue and improves the signal‑to‑noise ratio, allowing analysts to focus on high‑impact threats and accelerate remediation of compromised assets.
2️⃣ GreyNoise Intelligence Now Integrated into CrowdStrike Falcon Platform

Key Points:
- Brings GreyNoise reputation scoring into CrowdStrike’s endpoint detection suite.
- Supports automated enrichment of detections with global IP activity data.
- Helps prioritize alerts based on active exploitation trends.
Description:
The collaboration expands GreyNoise coverage to the CrowdStrike Falcon platform, enabling real‑time enrichment of endpoint alerts with contextual information about IP reputation, scan activity, and known exploit activity. This integration streamlines threat hunting and reduces investigation time.
Why It Matters:
Enterprises that rely on CrowdStrike gain a clearer view of which detections are likely part of broader campaigns, improving incident response prioritization and reducing dwell time for high‑risk threats.
3️⃣ SmartApeSG Campaign Leverages ClickFix to Deploy Remcos RAT
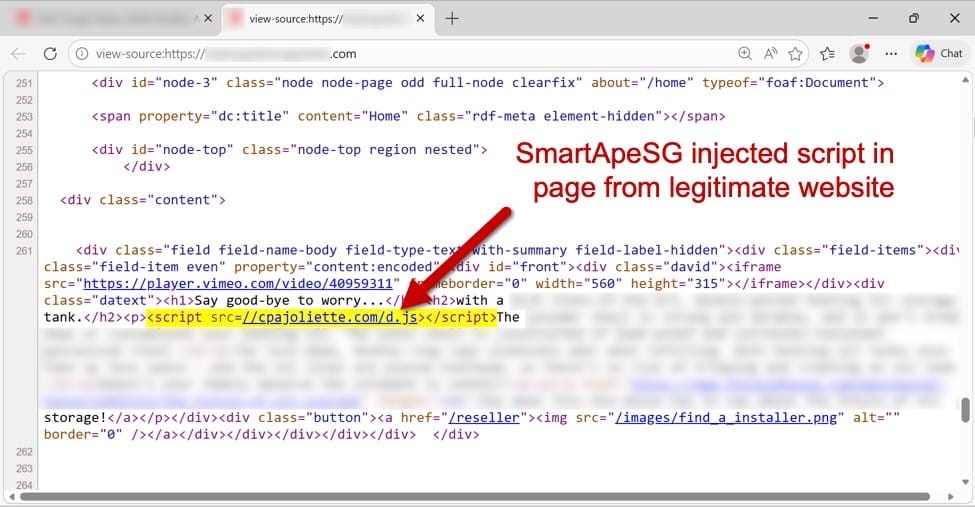
Key Points:
- Threat actors use compromised ClickFix pages to deliver Remcos remote‑access trojan.
- Campaign targets small‑to‑mid‑size businesses with spear‑phishing lures.
- Malware payloads obfuscated using custom packers to evade sandbox analysis.
Description:
Security researchers observed the SmartApeSG group abusing legitimate ClickFix web‑page creation services to host malicious scripts that download and execute the Remcos RAT on victim machines. The operation combines social engineering with fast‑flashing payload delivery, making detection challenging.
Why It Matters:
The technique demonstrates how attackers can hijack trusted cloud services for initial infection, prompting defenders to monitor third‑party service usage and implement stricter content‑security policies.
4️⃣ Cloudflare Launches Account Abuse Protection to Thwart Bot and Human Fraud
Key Points:
- Introduces machine‑learning models to differentiate legitimate vs. abusive account activity.
- Blocks credential‑stuffing, account takeover, and automated abuse attempts.
- Provides granular alerts and remediation guidance for customers.
Description:
Cloudflare announced a new Account Abuse Protection service that leverages behavioral analytics and AI to identify fraudulent activities targeting both bots and human users. The solution automatically challenges suspicious logins and offers real‑time reporting for security teams.
Why It Matters:
With credential‑stuffing attacks on the rise, organizations using Cloudflare can now reduce account takeover risk, protect customer data, and maintain trust without extensive manual rule creation.
5️⃣ Google Patches Two Actively Exploited Chrome Zero‑Days
Key Points:
- CVE‑2026‑XXXX and CVE‑2026‑YYYY allow remote code execution via malicious web content.
- Exploits observed in the wild targeting enterprise browsers.
- Patch released via Chrome 119.0.6045.113 with automatic rollout.
Description:
Google released emergency updates for two critical Chrome vulnerabilities that were actively exploited in targeted attacks against enterprise users. The flaws permitted attackers to execute arbitrary code by convincing victims to visit crafted web pages, bypassing Chrome’s sandbox protections.
Why It Matters:
Given Chrome’s prevalence across corporate environments, prompt patching is essential to close an active attack vector and prevent potential data exfiltration or ransomware deployment.
6️⃣ Malwarebytes Warns of Fake Renewal Notices in Calendar Invites
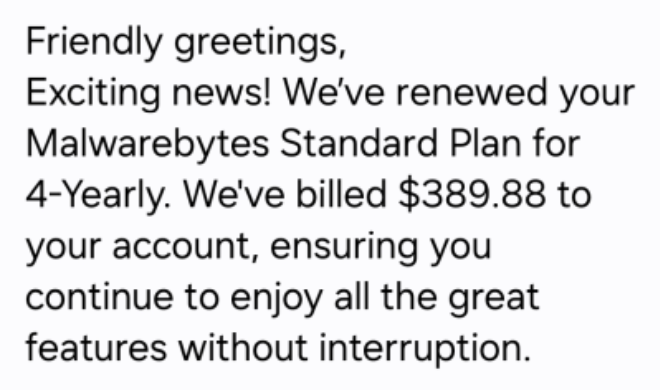
Key Points:
- Phishing campaign uses calendar event invitations mimicking Malwarebytes renewal emails.
- Links direct recipients to credential‑harvesting pages hosted on compromised domains.
- Campaign leverages trusted calendar platforms to increase click‑through rates.
Description:
Malwarebytes disclosed a social‑engineering campaign that distributes fraudulent renewal notices via calendar invites. Recipients see a familiar branding scheme and are prompted to click a link that leads to a credential‑stealing site, often resulting in compromised corporate accounts.
Why It Matters:
The abuse of calendar ecosystems highlights the need for users to verify renewal communications through official channels and for organizations to monitor for anomalous calendar activity.
7️⃣ New Study Links Security Metrics to Key Risk Indicators for Prioritizing Vulnerabilities

Key Points:
- Proposes an empirical framework that maps traditional security metrics to KRIs.
- Demonstrates improved vulnerability prioritization accuracy in simulated enterprise environments.
- Provides actionable formulas for integrating metric‑driven risk scoring into remediation pipelines.
Description:
Researchers published a paper detailing a framework that connects security performance metrics—such as patch latency and exploit prevalence—to key risk indicators (KRIs). The model quantifies risk exposure, enabling more data‑driven vulnerability management decisions.
Why It Matters:
Enterprises can adopt the methodology to align security operations with business risk objectives, ensuring resources focus on the most consequential vulnerabilities.
8️⃣ OpenClaw AI Agent Skills Weaponized to Automate Malware Delivery
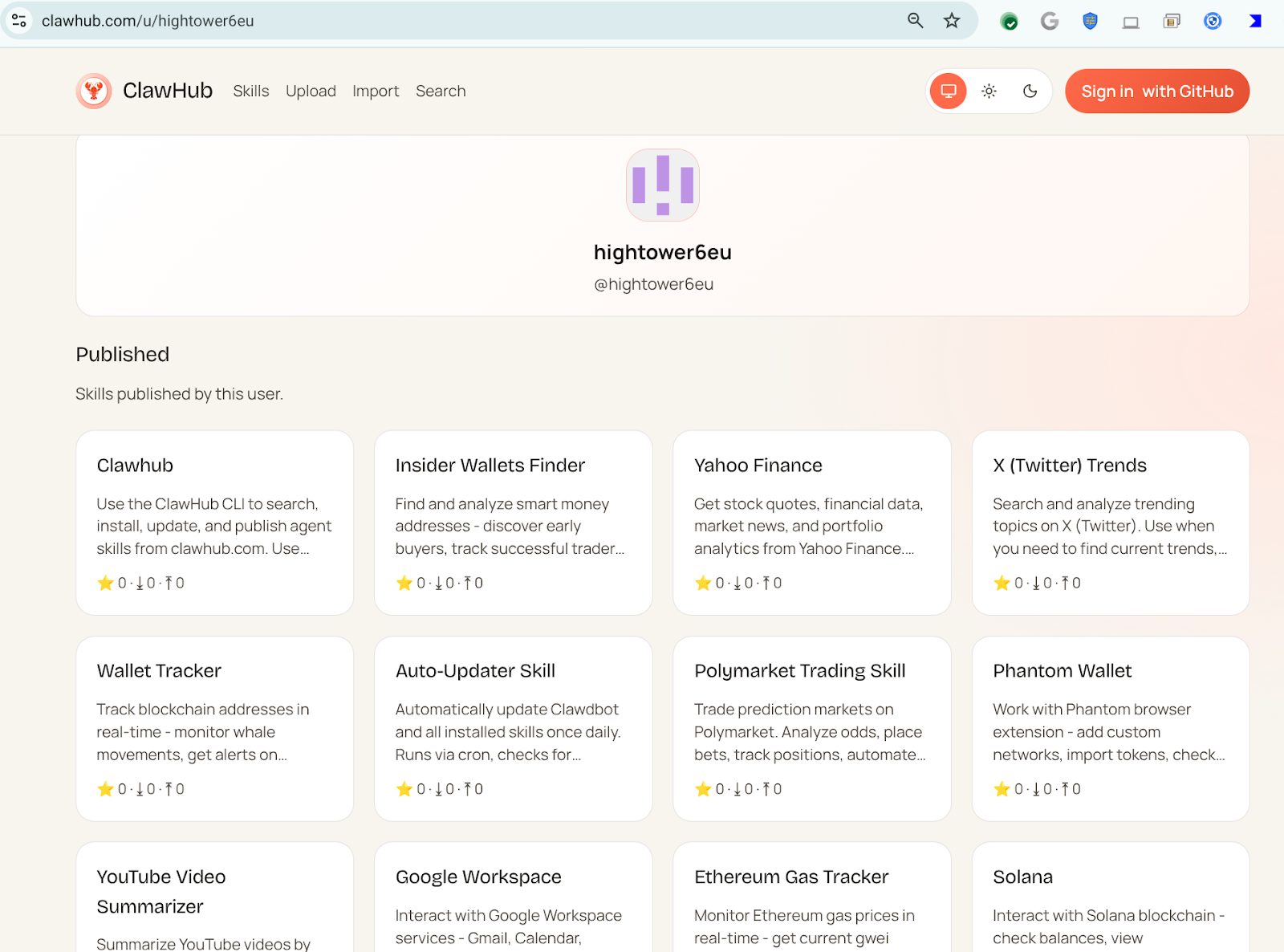
Key Points:
- Threat actor "hightower6eu" publishes malicious OpenClaw skills disguised as legitimate utilities.
- Skills instruct victims to download and execute code from untrusted sources.
- Over 300 malicious skills identified, covering diverse functional masks.
Description:
VirusTotal researchers uncovered a campaign where an OpenClaw AI agent user uploaded dozens of malicious skills that appear to perform benign tasks but actually retrieve and run malware binaries. The approach leverages the platform’s automation capabilities to scale infection campaigns.
Why It Matters:
The abuse of AI‑driven automation tools illustrates a new attack surface; organizations should monitor for unauthorized skill deployments and enforce strict validation of code execution pathways.
9️⃣ OpenClaw Part II Reveals Reverse Shells, Semantic Worms, and Cognitive Rootkits
Key Points:
- Continues analysis of OpenClaw malicious skills focusing on advanced persistence mechanisms.
- Identifies techniques such as semantic worm propagation and AI‑driven rootkits.
- Shows how reverse shells are auto‑generated within OpenClaw workflows.
Description:
The follow‑up blog post expands on the OpenClaw threat, detailing sophisticated techniques like reverse shells embedded in AI‑generated scripts, semantic worms that mutate to evade detection, and cognitive rootkits that adapt based on system responses.
Why It Matters:
Understanding these advanced tactics helps defenders develop detection signatures and harden environments against AI‑augmented malware, a growing concern for enterprise security.
🔟 ISC Stormcast Highlights Emerging Threats on March 16 2026
Key Points:
- Discusses recent surge in credential‑stuffing attacks targeting cloud services.
- Analyzes new IoT botnet activity observed in Southeast Asia.
- Provides mitigation recommendations for organizations deploying zero‑trust architectures.
Description:
The Internet Storm Center’s Stormcast podcast for March 16 2026 reviews the latest threat landscape, emphasizing the rise of credential‑stuffing campaigns against SaaS platforms, a growing IoT botnet exploiting vulnerable routers, and best practices for zero‑trust implementation.
Why It Matters:
Security leaders can leverage the insights to adjust defensive postures, prioritize patching of exposed IoT devices, and refine authentication controls to reduce exposure to emerging threats.
Stay vigilant and keep your defenses aligned with the evolving threat landscape.






Member discussion