Strategic Exposure to Emerging Threats & AI‑Driven Attack Vectors Demands Immediate Control

March 12, 2026 – Hello security leaders, here’s the latest risk intelligence.
Today's headlines
- GreyNoise integration streamlines Google SecOps alert triage.
- New GreyNoise feed enriches CrowdStrike Falcon investigations.
- IoT devices exposing default admin credentials threaten critical infrastructure.
- Microsoft Authenticator code leak undermines multi‑factor authentication.
- OpenClaw AI skills automate malicious code execution at scale.
1️⃣ GreyNoise Boosts Google SecOps Detection & Response
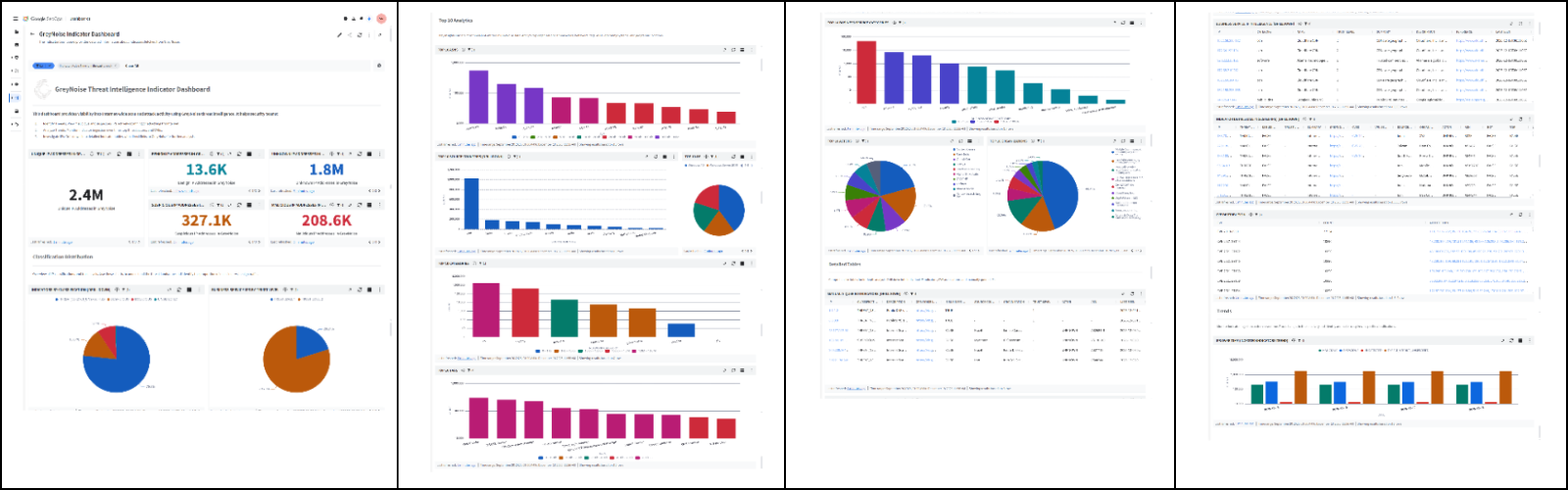
Key Points:
- Real‑time blocklists automatically filter noisy internet scans.
- Enriched IP context reduces false‑positive alerts in SIEM.
- Integrated threat intel accelerates incident investigation.
- Supports automated threat hunting workflows.
Description:
GreyNoise announced native integration with Google SecOps, delivering configurable blocklists and contextual IP intelligence directly into Google Cloud security tools, enabling security teams to suppress low‑value noise and focus on genuine threats.
Why It Matters:
For CISOs, the integration lowers alert fatigue, shortens response times, and improves overall SOC efficiency, directly impacting the organization’s risk reduction and compliance posture.
2️⃣ CrowdStrike Falcon Gains GreyNoise Intelligence
Key Points:
- GreyNoise data appears within Falcon dashboards and alerts.
- Provides early warning of emerging CVE exploitation trends.
- Improves prioritization of vulnerable assets.
- Enables faster context‑driven triage for analysts.
Description:
The partnership extends GreyNoise threat intelligence across the CrowdStrike Falcon platform, allowing users to view malicious IP reputation and activity signals alongside endpoint telemetry, thereby enriching detection and response capabilities.
Why It Matters:
Embedding external threat intel within Falcon streamlines workflow, helping security leaders allocate resources to the most impactful threats and maintain compliance with attack‑surface reduction mandates.
3️⃣ IoT Devices Default Admin Access Risks

Key Points:
- Many IoT units ship with hard‑coded admin credentials.
- Default logins bypass MFA and allow full system control.
- Device fingerprinting and continuous monitoring recommended.
- Business Impact Analyses should include IoT asset risk.
Description:
A recent SANS diary entry highlights that IoT devices often retain default administrative accounts, enabling attackers to gain privileged access shortly after deployment, a risk that persists despite traditional network defenses.
Why It Matters:
CISOs must incorporate IoT credential hygiene into their security programs; failure to remediate default accounts can lead to lateral movement and compromise of critical operational technology.
4️⃣ Microsoft Authenticator Vulnerability Exposes Login Codes

Key Points:
- A flaw can disclose generated MFA codes to background apps.
- Patch released; users must update the Authenticator immediately.
- Risk affects enterprise single‑sign‑on and privileged account access.
- Mitigation includes enforcing app‑level isolation and monitoring.
Description:
Security researchers discovered that certain versions of Microsoft Authenticator could inadvertently expose one‑time login codes to other applications on the device, prompting an urgent update from Microsoft.
Why It Matters:
The vulnerability undermines the core assurance of multi‑factor authentication, raising the risk of credential theft for high‑value accounts and potentially violating compliance requirements for MFA usage.
5️⃣ Android Lock Screen Bypass Vulnerability Discovered

Key Points:
- Exploit breaks Android lock screen in under a minute.
- Affects devices running Android 12 and newer.
- Google released a security patch; rapid deployment urged.
- Highlights need for mobile device management enforcement.
Description:
A newly reported Android vulnerability allows attackers to bypass the lock screen by exploiting a flaw in the biometric authentication pathway, granting full device access without user interaction.
Why It Matters:
Mobile devices are a primary vector for data leakage; organizations must prioritize patch management and enforce strict MDM policies to maintain device integrity and protect sensitive corporate information.
6️⃣ OpenClaw AI Skills Weaponized for Malware Delivery
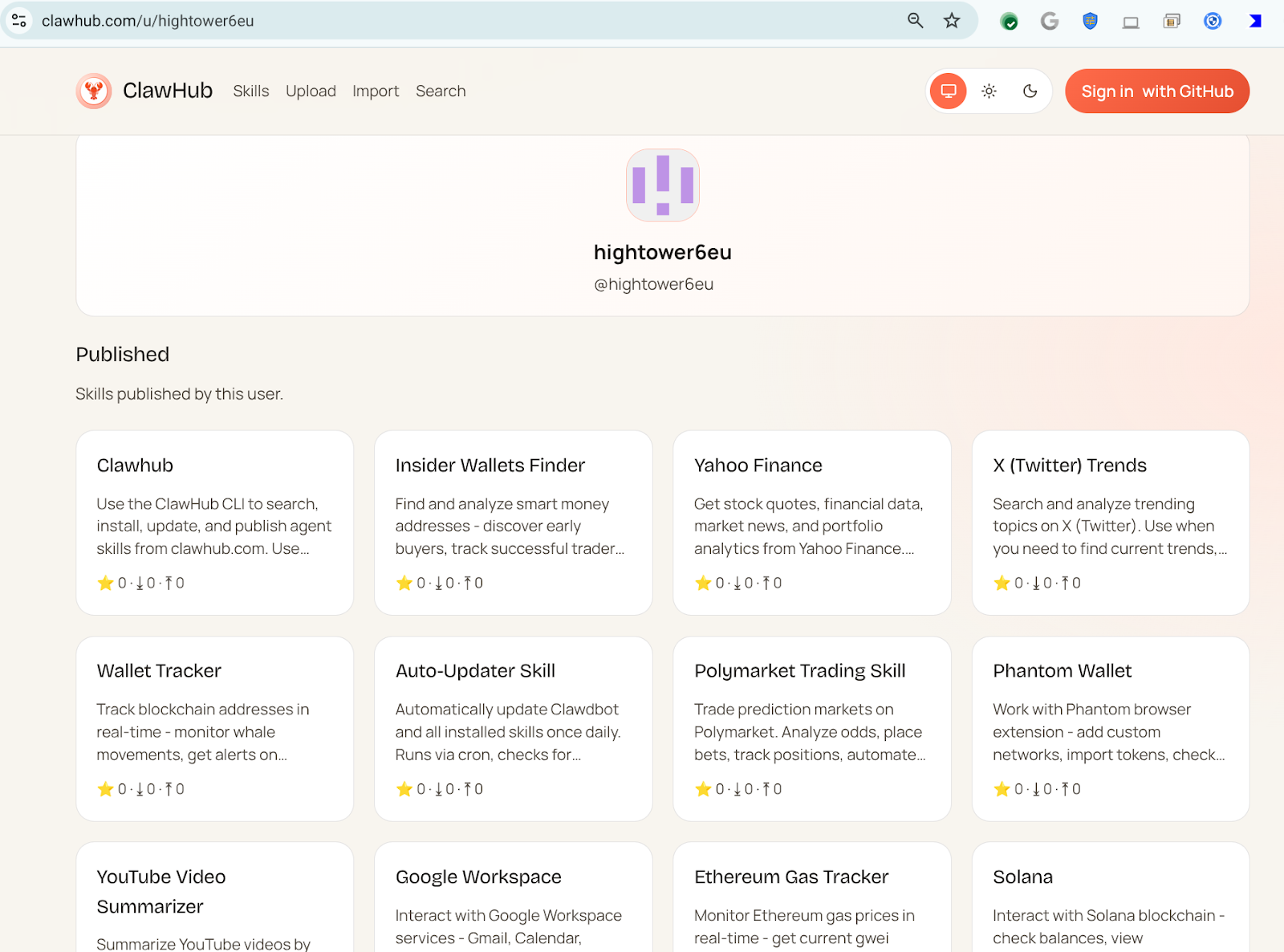
Key Points:
- Malicious AI‑generated skills download and execute untrusted code.
- Hundreds of skills linked to a single attacker profile.
- Skills masquerade as legitimate utilities (crypto, finance, etc.).
- Automation amplifies malware distribution across multiple platforms.
Description:
VirusTotal analysis uncovered that the OpenClaw AI platform is being abused by threat actors who publish deceptive automation skills that stealthily fetch and run malicious payloads on victim machines.
Why It Matters:
The abuse of AI‑driven automation tools expands the attack surface, making detection harder and requiring security teams to monitor for anomalous skill executions within their environments.
7️⃣ OpenClaw AI Enables Reverse Shells & Cognitive Rootkits
Key Points:
- New OpenClaw skills launch reverse shells targeting Windows and Linux.
- Semantic worms adapt behavior based on host context.
- Cognitive rootkits employ AI to evade endpoint protections.
- Demonstrates evolution from automation to full‑blown infection chains.
Description:
The follow‑up study details how adversaries are leveraging OpenClaw to create sophisticated reverse shells and AI‑enhanced rootkits that dynamically modify their tactics, techniques, and procedures to bypass security controls.
Why It Matters:
These capabilities signal a shift toward AI‑augmented malware capable of real‑time adaptation, forcing defenders to adopt behavior‑based detection and continuous threat‑model updates.
8️⃣ Study Reveals Generalization in Autonomous Attack Agents

Key Points:
- Research evaluates how autonomous agents generalize across targets.
- Findings show transferability of exploit strategies without explicit programming.
- Highlights potential for self‑learning malware to evolve post‑deployment.
- Calls for proactive AI safety frameworks in cyber defense.
Description:
An academic paper on arXiv investigates mechanisms that enable autonomous cyber‑attack agents to generalize learned behaviors, demonstrating that such agents can adapt to new vulnerabilities without human guidance.
Why It Matters:
Understanding these generalization traits helps CISOs anticipate future AI‑driven threats and shape defensive strategies that incorporate AI governance and continuous learning models.
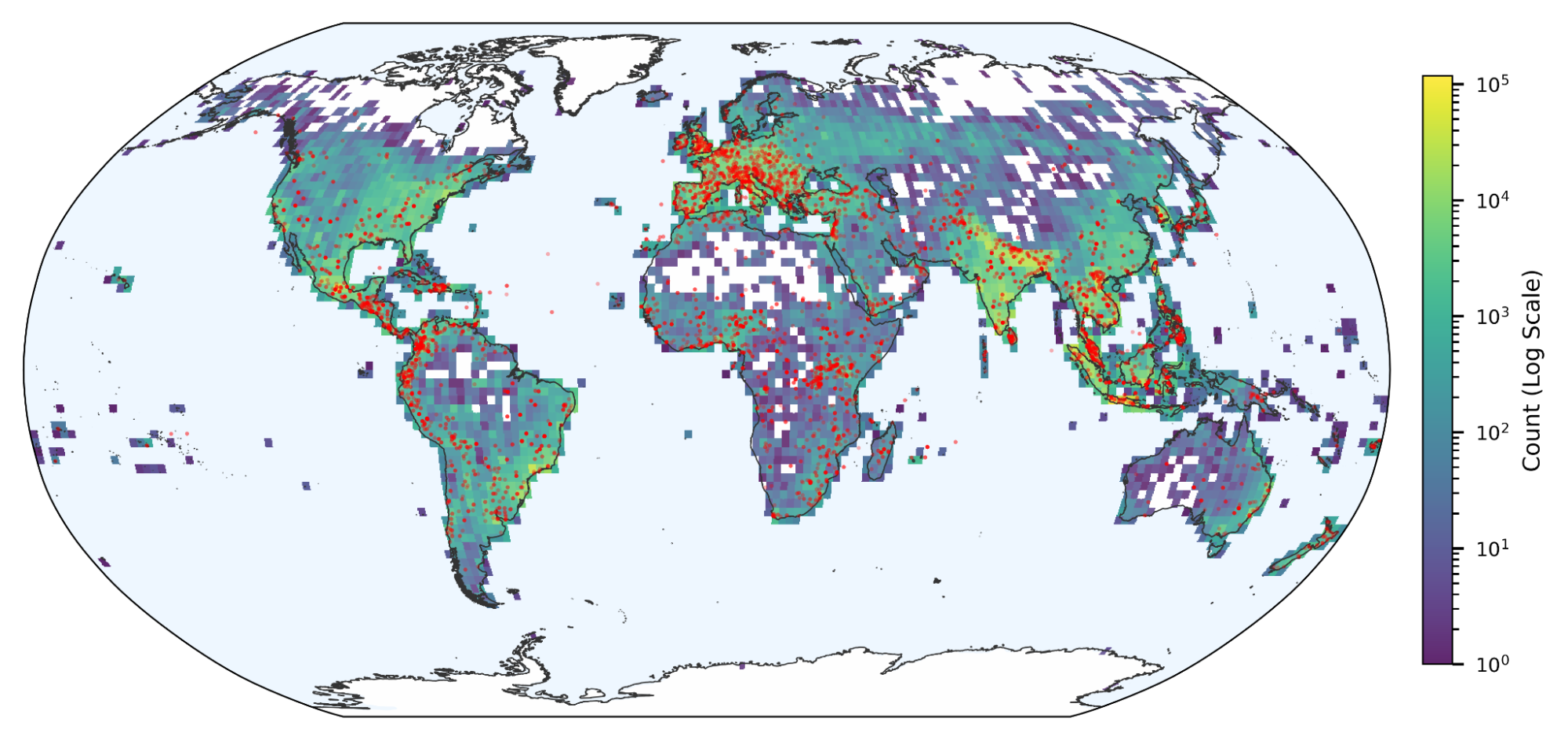
9️⃣ ISC Stormcast Highlights Current Scanning Trends

Key Points:
- Spike in SSH/Telnet scans from botnet clusters.
- Increased activity on rarely used high‑numbered ports.
- Geographic concentration of scans shifting towards Eastern Europe.
- Data useful for refining network baselines and IDS signatures.
Description:
The daily ISC Stormcast report for March 12, 2026 provides a snapshot of global scanning activity, noting heightened brute‑force attempts on legacy services and emerging port‑scan patterns.
Why It Matters:
Timely visibility into scanning trends enables security teams to adjust firewall rules, prioritize patching, and reduce the attack surface before exploitation attempts succeed.
🔟 Groundsource Leverages Gemini to Convert Crisis News into Structured Data
Key Points:
- Gemini AI extracts actionable data from unstructured news reports.
- Groundsource creates near‑real‑time datasets for disaster and crisis monitoring.
- Approach can be extended to security incident feeds for early warning.
- Improves situational awareness across remote and underserved regions.
Description:
Google Research introduced Groundsource, a system that uses the Gemini model to transform free‑form news articles into machine‑readable data, aiming to fill gaps in crisis intelligence where ground truth is scarce.
Why It Matters:
The technology offers a pathway to automate the ingestion of open‑source threat reports, giving CISOs faster, data‑driven insights for proactive risk management and incident preparedness.
Stay vigilant and align your defenses with these emerging insights.
Member discussion