Starkiller Phishing Service Mirrors Real Logins, Skips MFA and Harvests Tokens
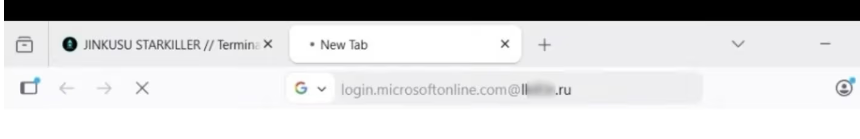
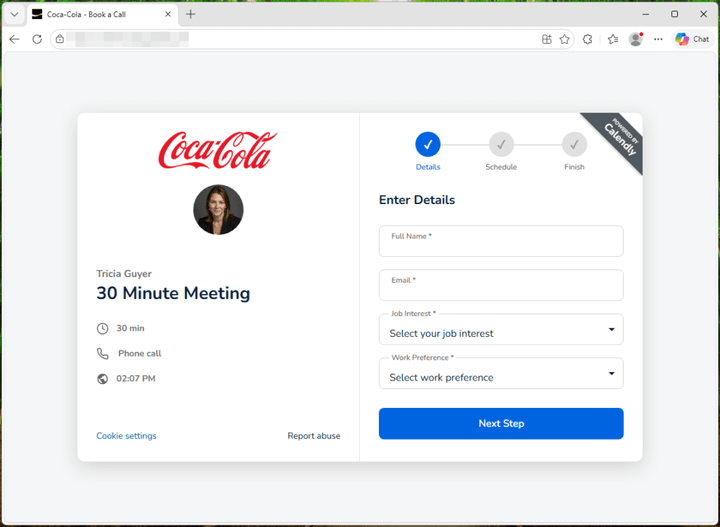
KrebsOnSecurity exposed a new phishing‑as‑a‑service platform dubbed “Starkiller” that routes victims through live, unmodified login pages of targeted services. By acting as a transparent proxy, the service captures usernames, passwords, and one‑time MFA codes in real time, then forwards the authentication request to the legitimate site, allowing the victim to log in without suspicion. The operation is sold to criminal affiliates, who can quickly spin up campaigns against any brand that supports web‑based authentication.
Because Starkiller harvests the actual MFA token rather than tricking users into providing a static password, it defeats many common anti‑phishing controls and yields high‑fidelity credentials that can be used to compromise privileged accounts. Defenders must treat this as a credential‑theft threat rather than a simple phishing nuisance: monitor for anomalous redirects, enforce MFA methods resistant to interception (e.g., push‑approved or hardware tokens), and implement continuous authentication risk analysis to spot logins that originated from proxy‑controlled browsers. Early detection and layered verification are essential to mitigate the damage from this sophisticated service.
Categories: Vulnerabilities & Exploits, Identity & Access Management (IAM), Security Culture & Human Factors
Source: Read original article

Comments ()