Resurrected LummaStealer Teams with CastleLoader to Target Enterprise Credentials
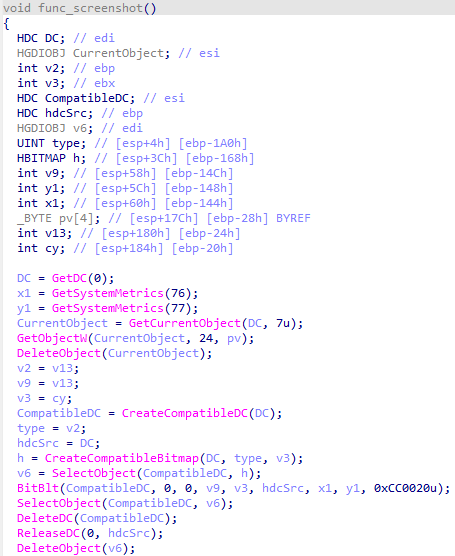
Bitdefender’s threat‑research team has identified a resurgence of the LummaStealer infostealer, now being bundled with the CastleLoader modular loader. The combined payload is distributed through highly crafted phishing emails that mimic legitimate software updates or business communications. Once the attachment is executed, CastleLoader drops a stealthy loader that injects LummaStealer into the memory of legitimate processes, evading many endpoint protections while establishing a command‑and‑control channel for credential harvesting.
The revived threat focuses on extracting browser passwords, VPN tokens, and remote‑desktop credentials, enabling attackers to move laterally and gain persistent access to high‑value assets. Defenders should prioritize detection of the loader’s characteristic process injection patterns, anomalous network connections to known CastleLoader C2 domains, and the presence of the encrypted payload files dropped in user profile directories. Updating YARA rules, tightening email filtering, and enforcing multi‑factor authentication are essential steps to mitigate this renewed attack vector.
Categories: Malware & Ransomware, Threat Intelligence
Source: Read original article



Comments ()