RCE and AI‑supply chain threats surge; phishing and OT edge defenses essential 🚨 💡
Greetings, February 25 2026 – here’s today’s executive threat overview.
Today's headlines
- BeyondTrust RCE (CVE‑2026‑1731) scanning spikes across networks
- AI‑assisted code tools abused to exfiltrate API tokens
- Supply‑chain attacks hide in malicious NuGet and npm packages
- Typosquatting campaigns increase malware delivery success
- Starkiller service proxies real login pages to defeat MFA
1️⃣ BeyondTrust RCE (CVE‑2026‑1731) reconnaissance escalates
Key Points:
- New remote code execution vulnerability discovered in BeyondTrust PAM products.
- GreyNoise reports a surge in scanning activity targeting the CVE‑2026‑1731 vector.
- Potential exploitation could grant attackers privileged access to critical systems.
- Patch release expected in Q2 2026; mitigation advised now.
- Immediate controls: block inbound traffic on affected ports and monitor for exploit signatures.
Description:
GreyNoise researchers observed coordinated reconnaissance against the newly disclosed BeyondTrust RCE vulnerability (CVE‑2026‑1731), indicating threat actors are actively mapping vulnerable assets before a public exploit may emerge. The flaw resides in the privileged access management service and could enable attackers to execute arbitrary code with elevated rights.
Why It Matters:
Compromise of privileged credentials undermines core security controls, exposing organizations to data breaches, ransomware, and compliance violations. Early detection and network segmentation are essential to reduce exposure while vendors finalize patches.
2️⃣ Claude code project files weaponized for RCE and token theft
Key Points:
- AI‑generated code repositories used to embed malicious payloads.
- Exploits achieve remote code execution on developer machines.
- Embedded scripts silently harvest cloud API tokens and exfiltrate them.
- Affected projects were shared via popular AI code assistants.
- Mitigation: enforce code review, restrict AI tool output, rotate compromised tokens.
Description:
Check Point researchers detailed how threat actors manipulate Claude AI code project files to deliver malicious code that both executes remotely and siphons API tokens, bypassing traditional security checks in development pipelines.
Why It Matters:
The abuse of AI coding assistants expands the attack surface of software supply chains, putting cloud credentials at risk and enabling lateral movement across environments. Organizations must harden CI/CD processes and monitor for anomalous token usage.
3️⃣ OT edge security model reduces dwell time

Key Points:
- Edge‑distributed sensors provide real‑time visibility into OT networks.
- Machine‑learning analytics prioritize alerts based on operational impact.
- Rapid isolation of compromised devices shortens attacker dwell time.
- Integration with existing SIEMs enables unified incident response.
- Pilot deployments show a 40% reduction in mean time to detect.
Description:
Unit42 outlines a strategy that shifts threat detection to the network edge in operational technology environments, leveraging lightweight agents and AI to identify anomalies directly at source devices.
Why It Matters:
Traditional centralized monitoring often misses OT-specific threats, leading to prolonged compromise. Deploying edge analytics enhances resilience of critical infrastructure and supports regulatory compliance for industrial sectors.
4️⃣ Check Point 2025 untold stories reveal AI weaponization trends
Key Points:
- Increase in AI‑generated phishing and deepfake content observed.
- Adversaries leverage large‑language models for automated vulnerability discovery.
- Supply‑chain attacks now embed AI scripts to adapt to defenses.
- Rise in weaponized ransomware that uses AI for target selection.
- Recommendations include AI‑aware detection and employee training.
Description:
The 2025 retrospective from Check Point highlights how threat actors have adopted artificial intelligence to automate exploitation, craft persuasive social engineering, and dynamically modify malware payloads.
Why It Matters:
AI‑enabled attacks scale more rapidly and evade conventional signatures, raising the bar for detection. Enterprises must integrate AI‑driven threat intelligence and reinforce human awareness programs.
5️⃣ Malicious NuGet packages steal ASP.NET Identity data

Key Points:
- Four NuGet packages published between Aug 12‑21 2024 contain backdoors.
- Packages exfiltrate ASP.NET Identity tables, including user credentials and roles.
- Persistent access achieved by modifying authorization rules in victim apps.
- Packages were signed with a compromised developer account.
- Mitigation: audit dependencies, enforce package provenance checks, rotate leaked credentials.
Description:
Security researchers at Socket uncovered a supply‑chain campaign distributing malicious NuGet packages that target ASP.NET developers, stealing identity data and establishing lasting backdoors in compromised web applications.
Why It Matters:
Compromised identity stores provide attackers with privileged access to corporate systems, increasing the likelihood of data breaches and ransomware. Continuous monitoring of third‑party libraries is essential for maintaining application security.
6️⃣ CrowdStrike 2026 report: AI‑enhanced adversary tactics

Key Points:
- Adversaries deploy generative AI to craft polymorphic malware.
- AI‑driven phishing emails achieve higher click‑through rates.
- Deepfake audio used for social engineering of privileged accounts.
- Defensive AI tools lag behind attacker capabilities.
- Strategic advice: adopt AI‑augmented detection, red‑team AI simulations.
Description:
CrowdStrike’s Global Threat Report for 2026 outlines how threat actors are increasingly using generative AI to automate malware creation, enhance phishing effectiveness, and produce convincing deepfake voice attacks.
Why It Matters:
The acceleration of AI in offensive operations narrows the detection window and raises the cost of false negatives. Enterprises must integrate AI‑powered analytics and conduct regular AI‑based breach simulations to stay ahead.
7️⃣ Typosquatting campaigns bypass traditional filters
Key Points:
- Threat actors register look‑alike domains with single‑character variations.
- Malicious sites host drive‑by exploits and credential‑stealing loaders.
- Campaigns use URL shorteners to obscure final destinations.
- Detection evaded by reputable DNS resolvers and whitelist policies.
- Countermeasure: implement domain‑monitoring and block fuzzy matches.
Description:
CrowdStrike researchers detail how attackers exploit typosquatting to deliver malware, leveraging near‑identical domain names that slip past conventional URL filtering and corporate whitelists.
Why It Matters:
Typosquatting increases the success rate of initial compromise, especially for remote workers. Proactive domain monitoring and strict URL filtering policies reduce exposure to these deceptive attacks.
8️⃣ Manual data‑transfer processes expose national‑security systems

Key Points:
- Over 50% of defense agencies still rely on manual file handling.
- Human error leads to accidental data leakage and insider threats.
- Recent supply‑chain breaches leveraged unsecured USB transfers.
- Automation reduces attack surface and improves auditability.
- Recommendation: adopt secure file‑transfer gateways and workflow automation.
Description:
The Hacker News reports findings from the CYBER360 report indicating that manual data‑transfer procedures in national‑security organizations create systemic vulnerabilities that adversaries exploit via compromised physical media.
Why It Matters:
Compromise of sensitive defense data can have cascading geopolitical impacts. Automating data flows enhances confidentiality, integrity, and compliance with governmental security standards.
9️⃣ Starkiller phishing service proxies real login pages, defeats MFA
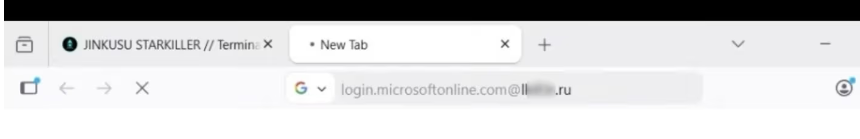
Key Points:
- Service hosts exact replicas of target login portals behind a proxy.
- Multi‑factor authentication codes are captured in real time.
- Operation offered as a subscription to cyber‑crime groups.
- Victims receive legitimate‑looking URLs that bypass URL filters.
- Mitigation: enforce hardware‑based MFA, monitor for proxy anomalies.
Description:
KrebsOnSecurity uncovered the Starkiller phishing-as-a‑service platform that routes victims through authentic login pages, capturing MFA tokens and credentials with high fidelity.
Why It Matters:
The ability to bypass MFA undermines one of the strongest defenses against account takeover, exposing enterprises to credential theft at scale. Deploying phishing‑resistant authentication methods and network traffic analytics is critical.
🔟 Student loan breach leaks 2.5 M personal records

Key Points:
- Data of 2.5 million borrowers exposed, including SSNs and financial details.
- Breach originated from an unpatched web application vulnerability.
- Attackers accessed both loan servicing and ancillary credit data.
- Regulatory notifications triggered under state breach‑notification laws.
- Remediation steps: enforce patch management, encrypt data at rest, conduct credit monitoring.
Description:
ThreatPost reports a breach of a major student loan servicer where attackers exploited an unpatched web flaw to exfiltrate personally identifiable information of 2.5 million borrowers.
Why It Matters:
Compromised financial data increases identity theft risk and can lead to regulatory penalties under GDPR, CCPA, and U.S. state laws. Organizations must prioritize vulnerability remediation and data encryption to protect consumer privacy.
Stay vigilant and prioritize controls to protect against evolving threats.
Member discussion