QR Code Phishing Spikes, Targeting Users on Web & Mobile
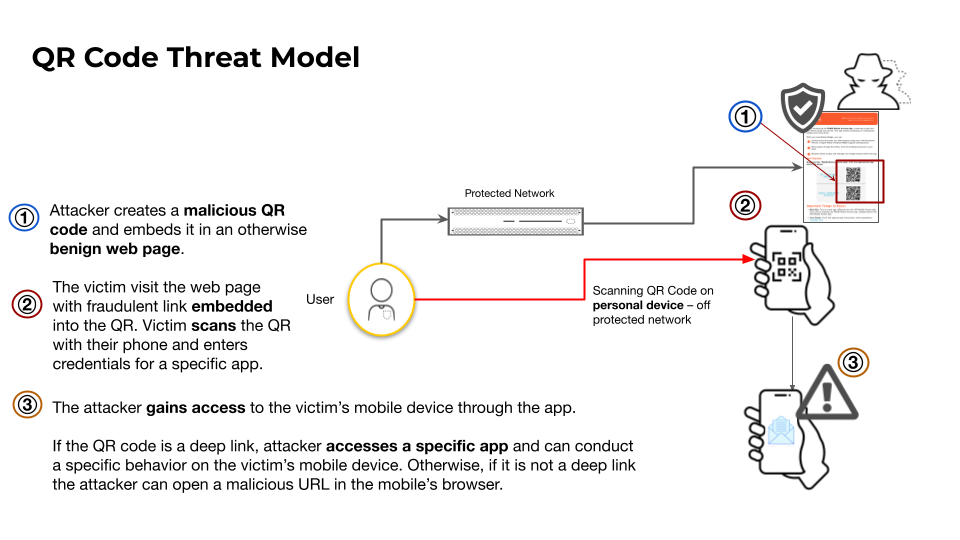
Palo Alto Networks’ Unit 42 has documented a sharp increase in QR‑code phishing campaigns that direct victims to credential‑stealing web pages or malicious app downloads. Attackers embed malicious URLs in QR codes displayed on public signage, receipts, and digital ads, leveraging the growing reliance on contact‑less interactions. Because the payload is delivered via a scanned code rather than email, traditional email security controls often miss these threats.
The campaigns have yielded a high success rate, harvesting credentials from corporate VPN logins, banking apps, and SaaS platforms. Unit 42 provides fresh indicators of compromise, including malicious domains, payload hashes, and QR‑code image fingerprints. Defenders must update web filtering, mobile device management, and user‑education programs to recognize suspicious QR codes, enforce URL reputation checks, and monitor for anomalous authentication attempts. Prompt detection and remediation can stop credential theft before attackers move laterally within the network.
Categories: Malware & Ransomware, Vulnerabilities & Exploits, Security Culture & Human Factors
Source: Read original article



Member discussion