Proxy‑Chained Scans Target SonicWall Firewalls, Skipping Rate Limits
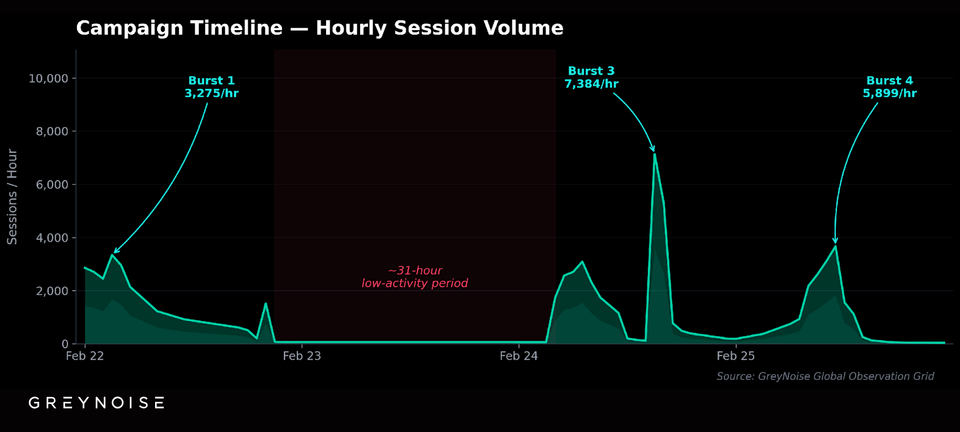
GreyNoise has identified an active reconnaissance campaign that leverages a chain of commercial proxy services to systematically probe SonicWall firewalls. By rotating through multiple IP ranges, the attackers evade rate‑based defenses and focus on organizations that use default SonicWall settings, primarily small and mid‑size enterprises.
The scans can expose vulnerable firmware or misconfigurations, giving threat actors a foothold for later exploitation. Defenders should tighten firewall configurations, enforce strict inbound proxy traffic controls, and implement logging and alerting for unusual SonicWall query patterns to disrupt this proxy‑based reconnaissance effort.
Categories: Threat Intelligence, SOC & Automation
Source: Read original article




Member discussion