Operation TrueChaos Exploits Zero‑Day in Video‑Conferencing Client to Target SE Asian Governments
Operation TrueChaos Exploits Zero‑Day in Video‑Conferencing Client to Target SE Asian Governments
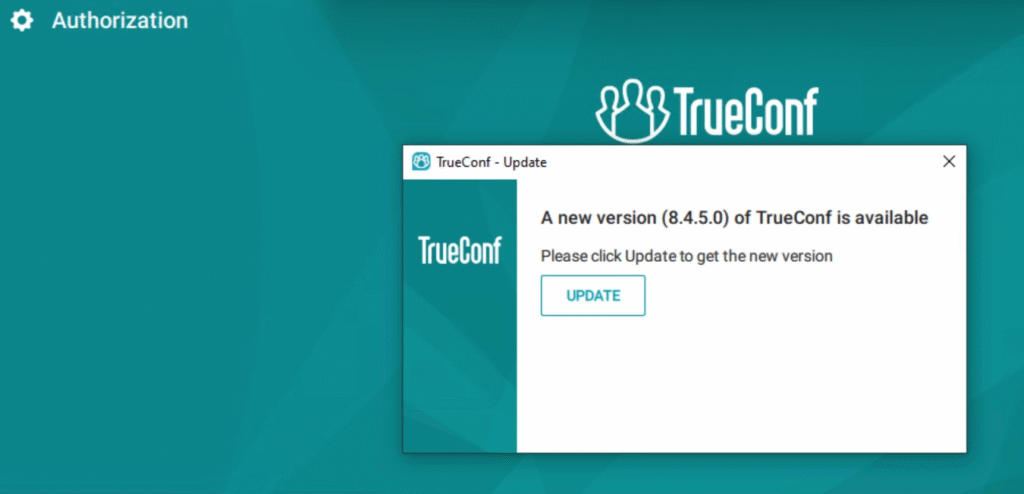
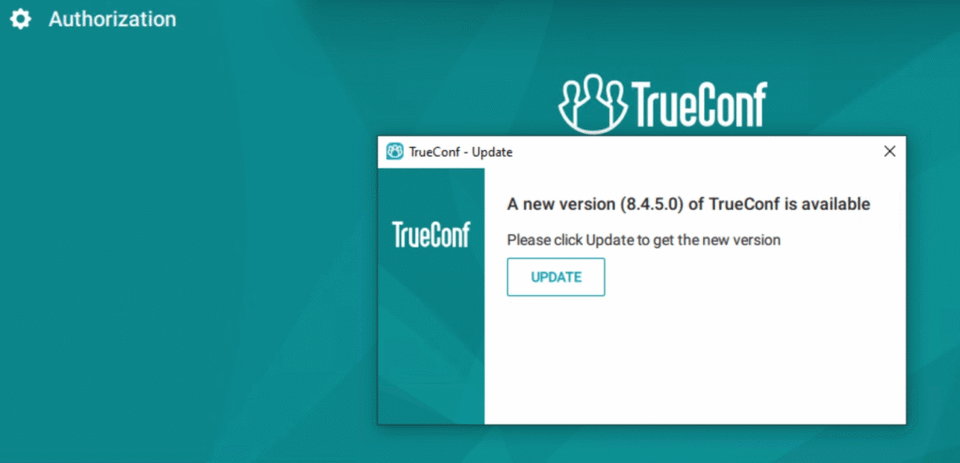
Check Point research uncovered Operation TrueChaos, a campaign that leveraged previously unknown vulnerabilities in the TrueConf video‑conferencing client. Malicious updates delivered multiple zero‑day exploits, installing disguised DLL loaders and the Havoc post‑exploitation framework on government networks across Southeast Asia.
The exploited flaws gave attackers persistent footholds and resilient command‑and‑control channels, which were traced to IP addresses located in the region. This enabled ongoing access and potential lateral movement within critical public‑sector systems.
Defenders should accelerate patch deployment for high‑risk software, monitor threat‑intel sources for emerging indicators of compromise, and apply hardened endpoint controls to limit the effectiveness of similar intrusion attempts.




Member discussion