OpenClaw AI Skills Weaponized to Deliver Malware via Automated Scripts
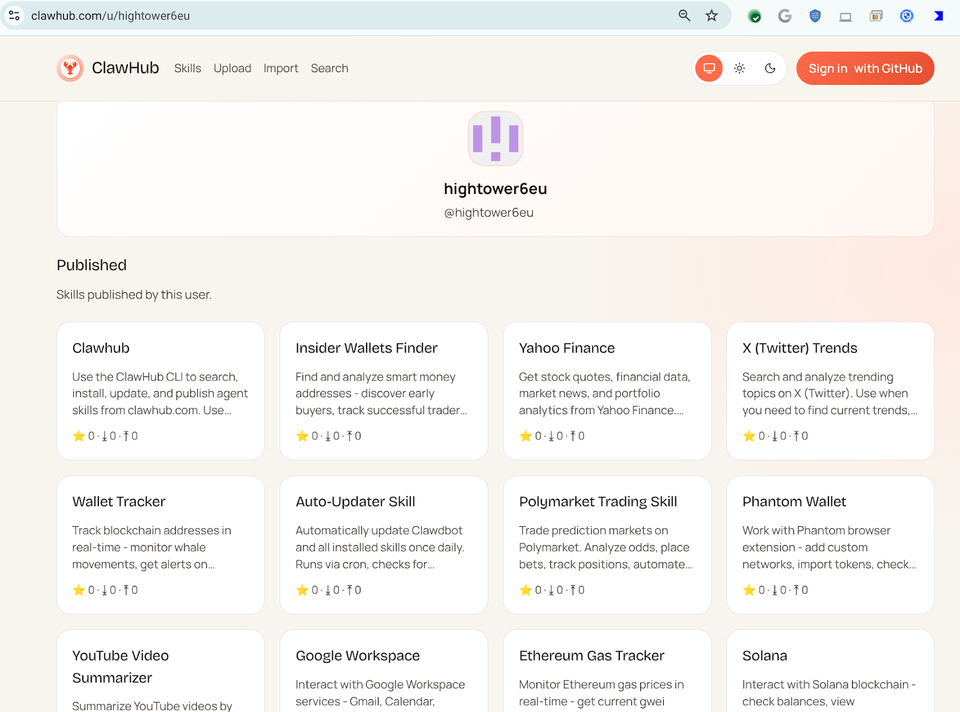
VirusTotal researchers discovered that threat actors are exploiting the OpenClaw low‑code automation platform by publishing AI‑generated “skills” that silently download and execute malicious payloads on victim endpoints. These skills are packaged to look like legitimate workflow automations, but they embed obfuscated PowerShell or curl commands that pull down ransomware, credential stealers, or other payloads once the skill is triggered. Because OpenClaw is a trusted marketplace often whitelisted in enterprise environments, the malicious skills can bypass traditional security controls and reach users with minimal friction.
The abuse turns a productivity tool into a delivery vector, expanding the attack surface for initial compromise and subsequent lateral movement. Defenders should treat any OpenClaw execution as suspicious, especially when new or unsigned skills appear. Immediate actions include adding OpenClaw binaries to application allow‑/deny lists, monitoring for outbound connections to unknown domains initiated by the platform, and integrating threat‑intel feeds that flag malicious skill hashes. Continuous inspection of skill metadata and user education on downloading unverified automation scripts are essential to mitigate this emerging threat.
Categories: AI Security & Threats, Malware & Ransomware
Source: Read original article



Member discussion