OpenClaw AI Skills Hijacked for Covert Malware Delivery
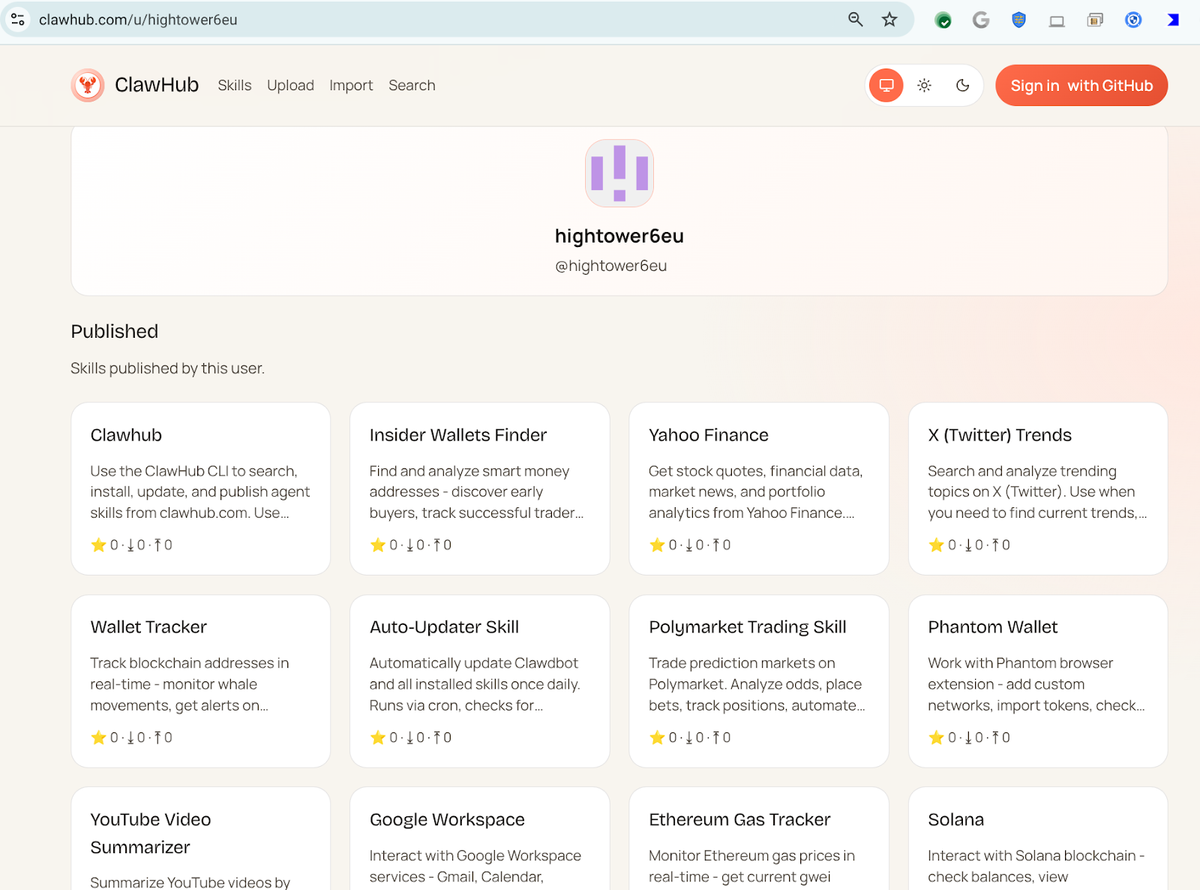
Threat actors have begun abusing the OpenClaw AI automation platform by publishing deceptive “skills” that appear legitimate but are programmed to silently retrieve and execute malicious payloads on compromised hosts. VirusTotal’s recent scans flagged several of these skills, revealing that they embed hidden network calls to malicious repositories and trigger payload execution without user interaction.
The abuse turns a trusted AI workflow tool into a delivery vector, allowing attackers to bypass traditional defenses and achieve persistence or lateral movement within target environments. Defenders should treat OpenClaw skill repositories as untrusted sources, monitor outbound connections for suspicious fetches, and implement strict validation or sandboxing of any AI‑generated automation before execution.
Categories: AI Security & Threats, Malware & Ransomware, Threat Intelligence
Source: Read original article



Comments ()