Malwarebytes Renewal Invite Scam Uses Calendar Events to Harvest Credentials
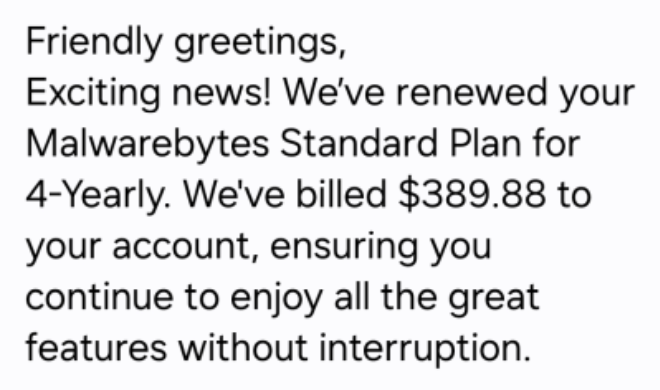
A new social‑engineering campaign is leveraging calendar invitations to distribute counterfeit Malwarebytes renewal notices. The invites appear to come from legitimate senders and contain a link that leads to a spoofed Malwarebytes portal. When users click, their credentials are captured and, in some cases, a malicious payload is silently delivered to the endpoint.
The breach can give attackers valid enterprise credentials, enabling them to bypass multi‑factor authentication, move laterally, and exfiltrate data. In addition, the payload may install remote access tools or ransomware, amplifying the impact across the organization.
Defenders must treat unexpected calendar events as potential phishing vectors, enforce verification of renewal communications, and monitor for anomalous login activity. Deploying URL filtering, endpoint detection, and user awareness training will help mitigate this emerging threat.
Categories: Threat Intelligence, Security Culture & Human Factors
Source: Read original article



Member discussion