LummaStealer Teams Up with CastleLoader to Boost Theft and Evade Detection
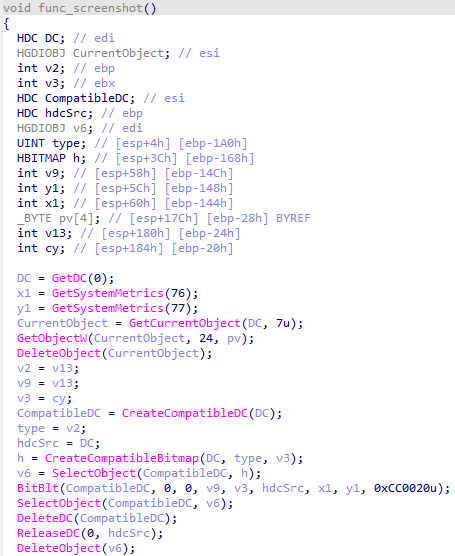
Bitdefender researchers have identified a resurgence of the LummaStealer credential‑stealer, now being delivered through the CastleLoader modular loader. The new pairing injects the stealer after CastleLoader establishes a foothold, allowing the malware to masquerade as legitimate user activity such as file browsing and software updates. This technique not only hides the malicious process from typical behavior‑based sensors but also expands the range of harvested data to include browser cookies, VPN credentials, and cloud service tokens across infected endpoints.
The combined threat poses a heightened risk for enterprises because the loader’s flexible architecture enables rapid updates and the inclusion of additional payloads without triggering traditional signature alerts. Defenders should prioritize monitoring for anomalous loader execution patterns, tighten application whitelisting, and enforce strict credential‑access controls to mitigate the broader data exfiltration capabilities introduced by this evolution.
Categories: Malware & Ransomware, Threat Intelligence
Source: Read original article




Member discussion