LummaStealer Teams Up with CastleLoader, Expanding Credential Theft Ops
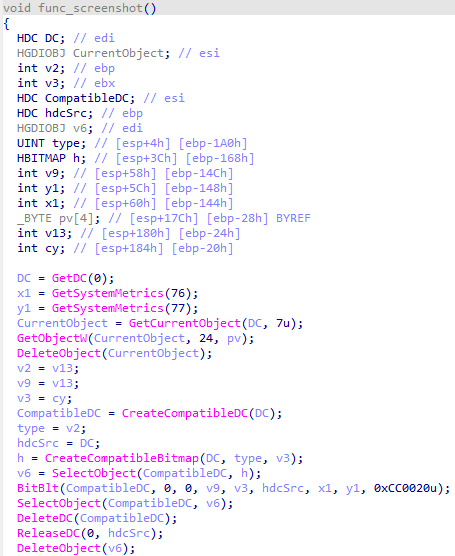
Bitdefender’s latest research shows the dormant LummaStealer infostealer has resurfaced, now bundled with the CastleLoader droploader. The combined malware chain uses sophisticated social‑engineering lures—phishing emails, malicious documents, and compromised websites—to trick users into executing a seemingly benign installer. Once run, CastleLoader drops LummaStealer via a legitimate‑looking Windows process, then both components coordinate to harvest stored credentials, browser cookies, and system information while maintaining a low profile.
The partnership broadens the attackers’ capabilities: CastleLoader serves as a flexible delivery platform for additional payloads, and LummaStealer enriches the exfiltration phase with a wider set of credential types. This evolution increases the risk of large‑scale credential leaks and lateral movement within corporate networks. Defenders should update detection rules to flag the characteristic process masquerading patterns, monitor for unusual DLL loading behaviors, and enforce strict email and web gateway controls to block the initial lure. Early identification of the CastleLoader dropper can disrupt the entire chain before sensitive data is exfiltrated.
Categories: Malware & Ransomware, Threat Intelligence
Source: Read original article



Comments ()