LummaStealer Returns with CastleLoader, Using New Evasion and Social‑Engineering Tricks
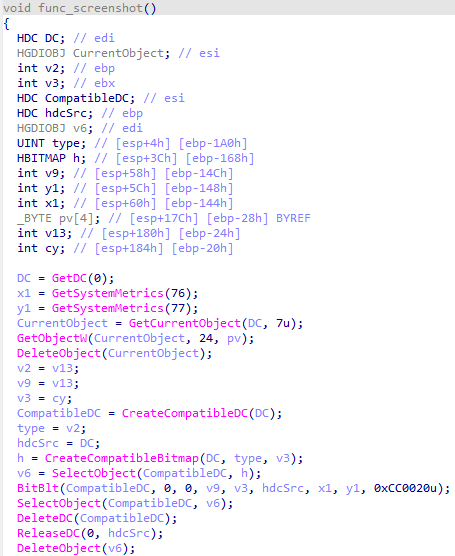
Bitdefender has observed a resurgence of the LummaStealer information‑stealer, now bundled with the CastleLoader droploader. The combined payload employs advanced evasion methods such as process hollowing, encrypted payloads, and runtime checks for sandbox environments. Attackers are also using social‑engineering lures that mimic routine user actions—like software updates or shared documents—to trick victims into executing the malicious dropper.
The renewed campaign enables credential harvesting, browser data theft, and the deployment of additional payloads through CastleLoader’s flexible loading engine. Because the malware disguises itself as legitimate activity and bypasses many traditional detection controls, organizations may see an increase in undetected data exfiltration and lateral movement. Defenders should prioritize updating detection signatures, enable behavioral analytics for droploader activity, and reinforce user awareness training to mitigate the heightened risk.
Categories: Malware & Ransomware, Threat Intelligence
Source: Read original article



Comments ()