LummaStealer Returns, Teams with CastleLoader to Boost Persistence
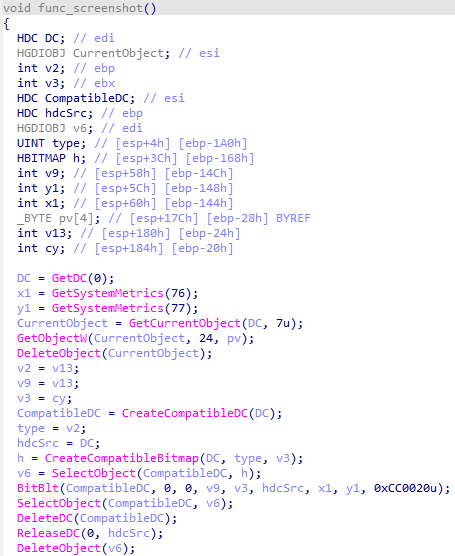
Bitdefender has identified a new wave of LummaStealer activity in which the notorious infostealer is being delivered by the CastleLoader dropper. The loader installs itself in legitimate‑looking directories, modifies autostart registry keys, and injects the payload into trusted system processes, giving the malware a durable foothold and helping it slip past traditional signature‑based scanners.
The combined threat harvests credentials, browser data, and cryptocurrency wallets while maintaining long‑term persistence on infected hosts. Defenders should prioritize updating detection rules with the latest CastleLoader indicators, enable behavioral monitoring for process injection and registry changes, and enforce strict application whitelisting to reduce the attack surface.
Categories: Malware & Ransomware, Threat Intelligence
Source: Read original article



Comments ()