LummaStealer Returns, Now Riding CastleLoader for Stealthier Delivery
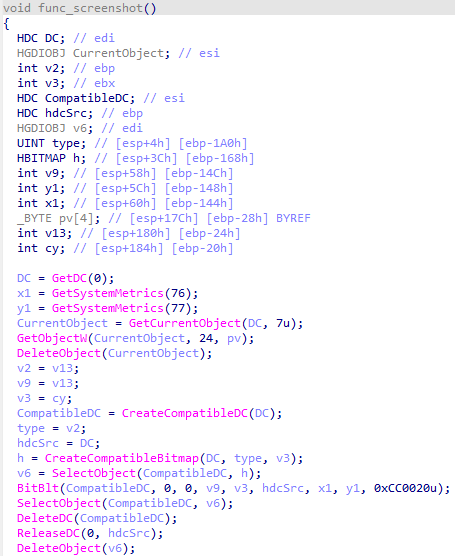
Bitdefender’s threat‑research team has identified a new variant of the LummaStealer Trojan that now piggybacks on the CastleLoader modular loader. The combination uses a two‑stage drop: CastleLoader first infiltrates the host, then fetches and executes the LummaStealer payload. Both components employ refined social‑engineering lures—phishing emails, malicious documents, and fake software updates—and masquerade as legitimate Windows processes such as svchost.exe and rundll32.exe, making behavioural detection far more difficult.
For defenders, this evolution means traditional signature‑based tools and simple process‑name whitelists are insufficient. The loader’s ability to encrypt its payload, inject it into trusted processes, and dynamically resolve C2 infrastructure evades many sandbox and endpoint detection solutions. Organizations should prioritize behavioral analytics, enforce strict code‑signing verification, monitor for anomalous DLL loading patterns, and update threat‑intel feeds to include the latest CastleLoader indicators of compromise.
Categories: Threat Intelligence, AI Security & Threats, Malware & Ransomware
Source: Read original article




Member discussion