LummaStealer Returns, Bundled with CastleLoader – New Social‑Engineering Threat
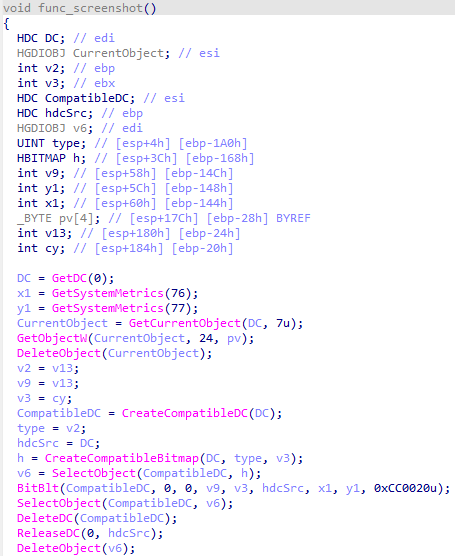
Bitdefender’s latest lab report confirms that the long‑dormant LummaStealer trojan has resurfaced, this time shipped alongside the CastleLoader dropper. Attackers are using highly tailored phishing emails and malicious document macros to deliver the combined payload. Once executed, CastleLoader establishes a stealthy foothold, then fetches and launches LummaStealer, which proceeds to harvest credentials, browser data, and other sensitive files before encrypting them for exfiltration.
The resurgence poses a direct risk to enterprise networks and remote workforces, as the loader bypasses many traditional AV signatures and leverages legitimate system utilities for persistence. Defenders should immediately update endpoint detection rules to flag CastleLoader’s known binaries, monitor for the characteristic network callbacks of LummaStealer, and enforce strict macro execution policies. Early detection and isolation are critical to prevent data loss and limit the attacker’s lateral movement.
Categories: Malware & Ransomware, Threat Intelligence
Source: Read original article



Comments ()