Legislative Surveillance Expands Threat Surface 🌐. AI-Enhanced Defense Tools Accelerate Incident Response ⚡

Good morning, March 15 2026 – here’s the critical intel you need.
Today's headlines
- Canada’s Bill C-22 could mandate broad metadata collection, raising compliance challenges.
- GreyNoise now powers real‑time blocklists in CrowdStrike Falcon, cutting noise.
- New Google SecOps integration brings automated malicious IP detection.
- SmartApeSG leverages ClickFix to deliver Remcos RAT across compromised hosts.
- Cloudflare launches Account Abuse Protection to block fraudulent bot activity.
- Malwarebytes warns of fake renewal calendar invites targeting enterprises.
1️⃣ Canada’s Bill C-22 Expands Metadata Surveillance
Key Points:
- Mandates mandatory collection of metadata from electronic services.
- Broad definition could classify routine data as vulnerable.
- Raises legal exposure for organizations handling Canadian user data.
- Potential conflict with existing international privacy regulations.
Description:
Bill C-22, recently introduced in the Canadian Parliament, requires extensive metadata surveillance of domestic electronic communications. The legislation defines “vulnerable” data in a way that could encompass routine service logs, compelling service providers to implement new collection and retention mechanisms.
Why It Matters:
Enterprises with Canadian customers must reassess data handling practices to avoid non‑compliance penalties and reputational damage. Aligning with the bill may also necessitate architectural changes that increase operational overhead and exposure to insider threats.
2️⃣ GreyNoise Intelligence Integrated into CrowdStrike Falcon
Key Points:
- Provides real‑time blocklists to stop noisy internet scanners.
- Delivers early warnings of active CVE exploitation trends.
- Reduces SOC alert fatigue by filtering low‑priority events.
- Seamlessly available within the Falcon console.
Description:
GreyNoise announced native integration with the CrowdStrike Falcon platform, allowing analysts to apply crowd‑sourced threat context directly to endpoint detections. The partnership delivers configurable blocklists and automated enrichment of alerts with malicious IP reputation data.
Why It Matters:
By cutting out background noise, security teams can focus on high‑impact incidents, accelerating response times and conserving resources. The integration also strengthens threat‑intel sharing across heterogeneous environments.
3️⃣ GreyNoise Google SecOps Integration Boosts Detection
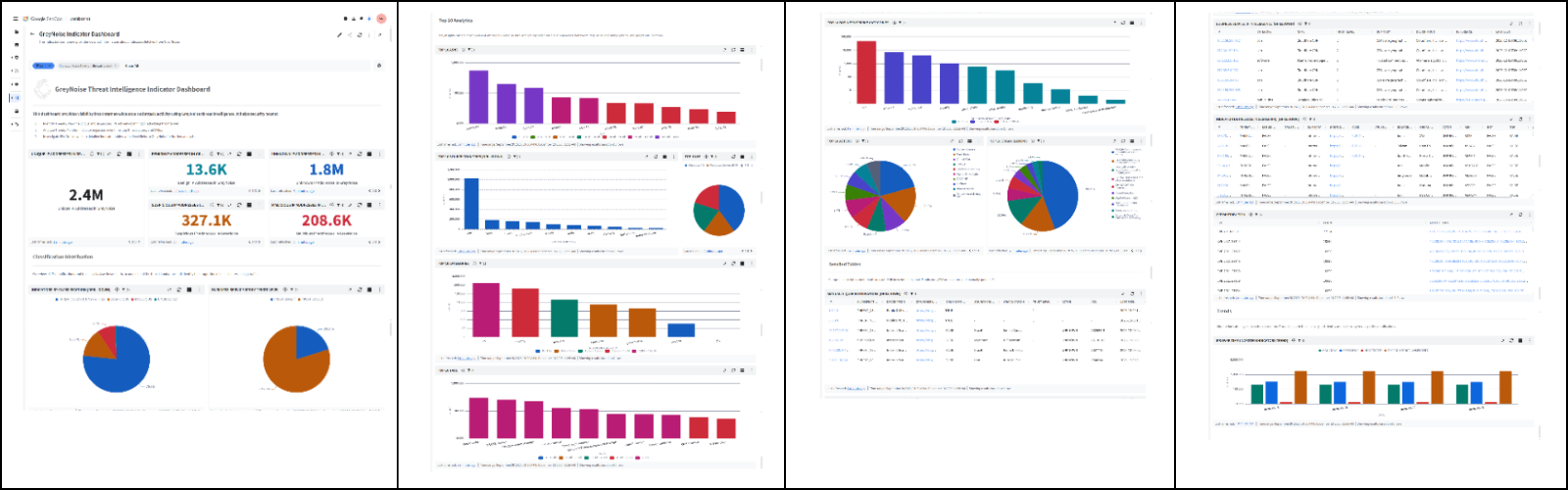
Key Points:
- Automates enrichment of malicious IP data in Google Cloud workloads.
- Supports incident investigation with contextual threat intel.
- Enables automated response via Cloud Functions and Workflows.
- Improves mean‑time‑to‑detect for cloud‑native assets.
Description:
GreyNoise extended its intelligence services to Google SecOps, embedding real‑time IP reputation data into Google Cloud’s security operations suite. The integration feeds threat context into Cloud Logging, Security Command Center, and automated remediation pipelines.
Why It Matters:
Enterprises leveraging Google Cloud gain immediate visibility into hostile activity, reducing reliance on manual threat hunting. Automated actions based on GreyNoise signals can contain breaches before lateral movement occurs.
4️⃣ SmartApeSG Campaign Uses ClickFix to Deploy Remcos RAT
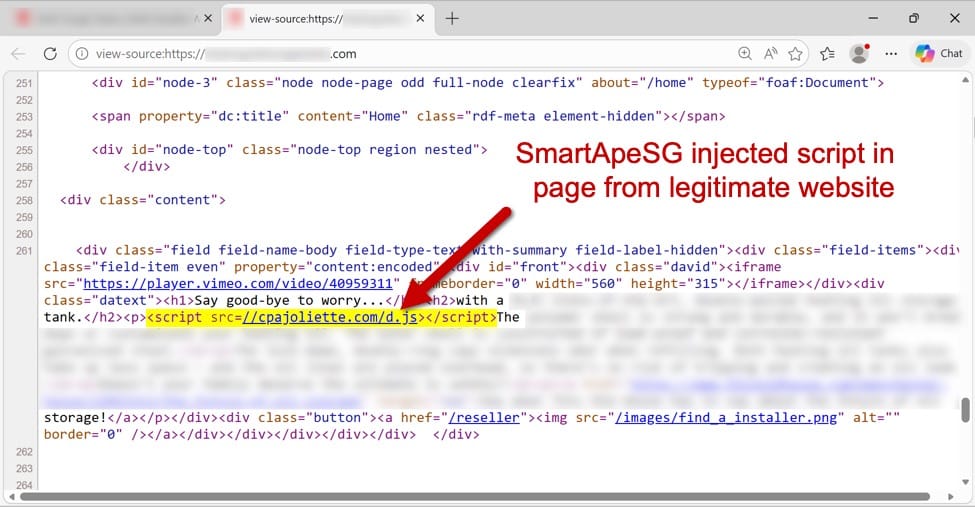
Key Points:
- Compromised ClickFix pages serve as drop zones for Remcos RAT.
- Campaign observed targeting SMB networks in March 2024.
- Payload delivery leverages obfuscated JavaScript redirects.
- Indicators include specific URL patterns and unusual HTTP headers.
Description:
Security researchers reported that the SmartApeSG threat actor is exploiting the ClickFix vulnerability to host the Remcos remote access trojan. Victims receive malicious payloads after visiting compromised pages that masquerade as legitimate software updates.
Why It Matters:
The use of a legitimate third‑party service for distribution complicates detection. Organizations must monitor outbound traffic for connections to known ClickFix domains and apply strict web filtering to mitigate infection risk.
5️⃣ Cloudflare Account Abuse Protection Blocks Fraudulent Bots
Key Points:
- Introduces behavioral analysis to detect abusive account activity.
- Protects login, registration, and API endpoints from credential stuffing.
- Integrates with Cloudflare Zero Trust policies for unified enforcement.
- Provides dashboards for visibility into abuse trends.
Description:
Cloudflare launched Account Abuse Protection, a service that leverages machine learning to identify and block malicious bots and human actors attempting to abuse customer accounts. The feature works across the entire Cloudflare edge network, offering real‑time mitigation.
Why It Matters:
By preventing automated credential theft and abuse, organizations can safeguard user data and reduce downstream incident response costs. Visibility into abuse patterns also informs broader security strategy and policy adjustments.
6️⃣ Fake Malwarebytes Renewal Notices Spread via Calendar Invites
Key Points:
- Phishing campaign uses .ics calendar invites mimicking renewal alerts.
- Embedded links redirect to credential‑stealing landing pages.
- Targets both individual users and enterprise Malwarebytes customers.
- Detection relies on email security gateways and user awareness training.
Description:
Malwarebytes warned that cybercriminals are distributing fraudulent calendar invitations that appear to be renewal reminders. Recipients who accept the invite receive a malicious .ics file, and clicking the embedded link leads to a spoofed Malwarebytes login portal.
Why It Matters:
The campaign exploits trust in calendar systems, bypassing traditional email filters. Organizations should educate users about unsolicited invites and enforce attachment scanning to mitigate this vector.
7️⃣ Google Patches Two Chrome Zero‑Days Under Active Exploitation
Key Points:
- Zero‑day 1: Use‑after‑free vulnerability in V8 JavaScript engine.
- Zero‑day 2: Sandbox escape via malicious browser extension.
- Active exploitation observed in targeted phishing campaigns.
- Immediate update to Chrome 130 recommended for all users.
Description:
Google released emergency updates for Chrome addressing two critical zero‑day vulnerabilities actively exploited by threat actors. The first flaw enables arbitrary code execution through a crafted webpage, while the second permits a malicious extension to break out of the browser sandbox.
Why It Matters:
Given Chrome’s market share, successful exploitation can lead to widespread credential theft and persistent footholds. Prompt patch deployment and enforcing auto‑updates are essential to prevent compromise.
8️⃣ AWS Introduces AMI Lineage for Secure Image Lifecycle
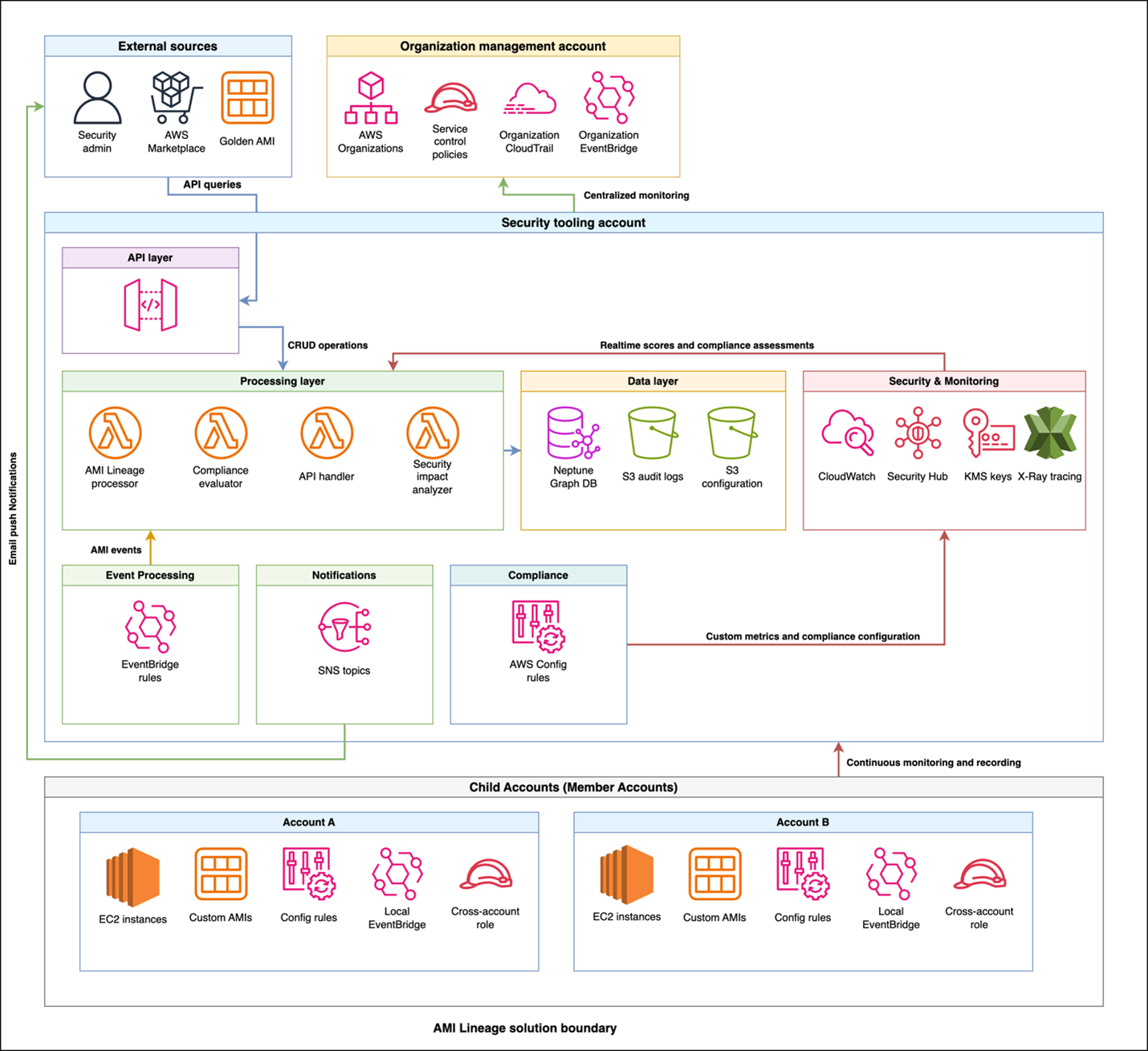
Key Points:
- Tracks creation, modification, and approval of AMIs across accounts.
- Provides audit‑ready lineage data for compliance reporting.
- Automates deprecation of vulnerable images based on policy rules.
- Integrates with AWS Security Hub for centralized visibility.
Description:
AWS launched AMI Lineage, a service that records the full history of Amazon Machine Images, including security scans, approvals, and changes. The solution offers dashboards and automated remediation workflows to maintain a hardened image inventory.
Why It Matters:
Maintaining provenance of AMIs helps organizations meet regulatory requirements and quickly eliminate outdated images that may contain known vulnerabilities, reducing the attack surface in cloud deployments.
9️⃣ Cloudflare AI Security for Apps Now Generally Available

Key Points:
- AI models analyze request patterns to block malicious traffic.
- Reduces token usage by over 98% compared to prior parsers.
- Provides real‑time risk scores for API endpoints and web apps.
- Integrated into Cloudflare dashboard for actionable insights.
Description:
Cloudflare announced the general availability of AI Security for Apps, a service that leverages machine‑learning to identify and mitigate API‑based attacks. The platform delivers high‑precision threat detection while dramatically lowering computational overhead.
Why It Matters:
Enterprises can now defend complex, high‑traffic applications with adaptive AI that evolves alongside emerging threats, improving security posture without sacrificing performance.
🔟 VirusTotal Explores OpenClaw AI Agents for Advanced Malware Evasion
Key Points:
- Shows reverse shells, semantic worms, and cognitive rootkits generated by AI.
- Demonstrates AI‑driven code that adapts to defensive tools.
- Provides proof‑of‑concept attacks using the OpenClaw framework.
- Calls for updated detection heuristics and AI‑aware defenses.
Description:
VirusTotal published a deep‑dive into OpenClaw, an AI‑enabled framework that can automatically generate sophisticated malware components, including semantic worms and cognitive rootkits. The article illustrates how AI can automate the creation of evasive techniques.
Why It Matters:
The emergence of AI‑crafted threats challenges traditional signature‑based defenses, urging security teams to adopt behavior‑based detection and invest in AI‑augmented threat‑intel capabilities.
Stay vigilant and keep your defenses ahead.






Member discussion