Kimwolf Botnet Weaponizes I2P, Flooding Anonymity Network with Massive Traffic
The Kimwolf botnet has begun abusing the I2P anonymity network’s open routing architecture to inject a torrent of unwanted traffic. By leveraging compromised hosts worldwide, the operators are directing high‑volume packets through I2P tunnels, effectively using the network as a veil for their flood attacks while evading traditional IP‑based detection.
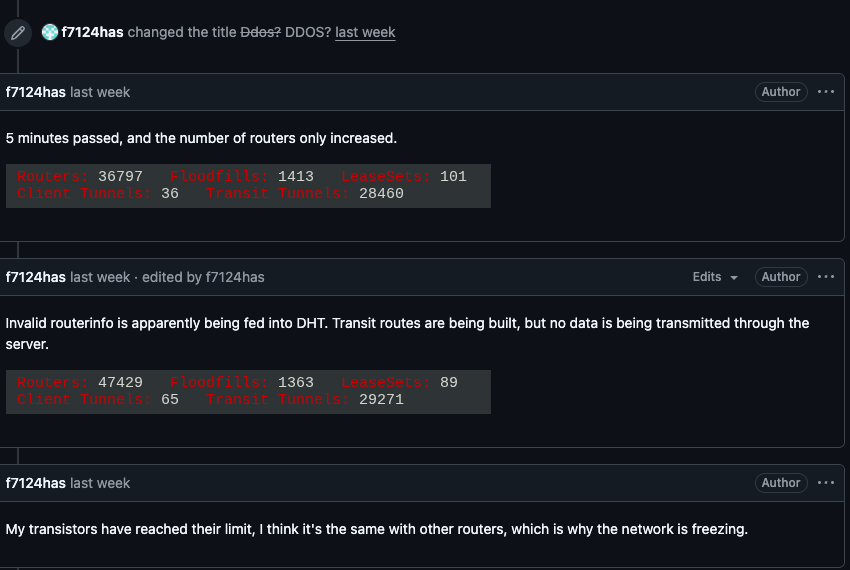
This surge in traffic is overwhelming I2P routers, leading to increased latency, reduced throughput, and intermittent denial‑of‑service conditions for legitimate users. The degradation threatens the reliability of privacy‑focused services that depend on I2P, and the botnet’s ability to hide behind the network complicates attribution and mitigation efforts.
Defenders must treat this as a dual‑front threat: both a botnet amplification vector and a risk to privacy infrastructure. Immediate actions include deploying traffic‑analysis sensors on I2P ingress points, updating IDS/IPS signatures to flag anomalous volume patterns, and coordinating with I2P maintainers to enforce rate‑limiting or blacklist malicious endpoints. Early detection and containment are essential to protect both enterprise networks and the broader anonymity ecosystem.
Categories: Threat Intelligence, AI Security & Threats, Malware & Ransomware
Source: Read original article




Member discussion