Kimwolf Botnet Moves C2 to I2P, Hiding in IoT Networks
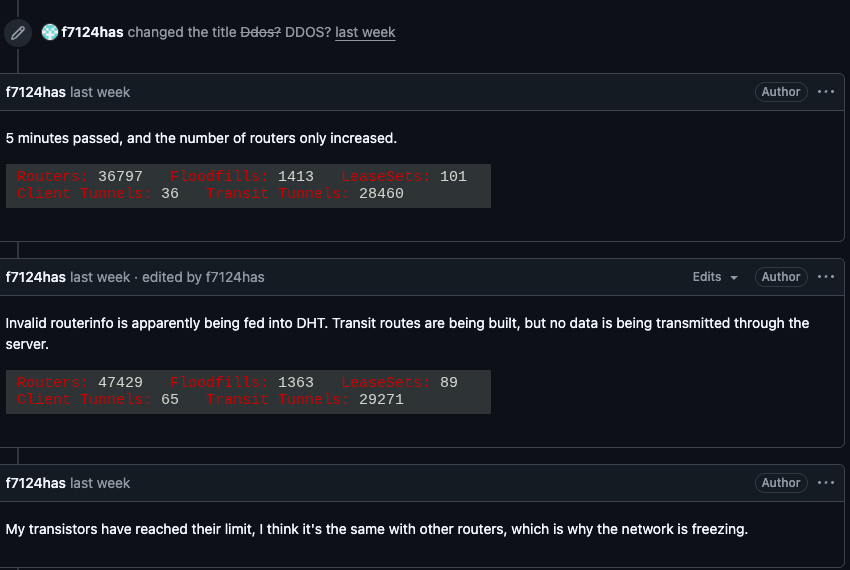
Security researchers have confirmed that the Kimwolf botnet, known for compromising consumer‑grade IoT devices, has migrated its command‑and‑control (C2) infrastructure onto the I2P anonymity network. By routing traffic through I2P’s encrypted tunnels, the botnet can issue instructions, download payloads, and exfiltrate data while evading traditional network‑based detection tools that rely on clear‑text IP or domain indicators.
The shift to I2P dramatically raises the risk profile for enterprise and ISP defenders. Standard DNS and IP reputation filters no longer reveal malicious endpoints, and traffic analysis becomes more complex due to I2P’s built‑in privacy features. Defenders must augment their monitoring with I2P‑specific heuristics, increase visibility into outbound encrypted traffic, and prioritize IoT device hardening and credential hygiene to prevent initial infection. Ignoring this evolution could allow the botnet to scale, amplify DDoS capabilities, and expand its foothold across critical infrastructure.
Categories: Threat Intelligence, Malware & Ransomware
Source: Read original article




Member discussion