Kimwolf Botnet Hijacks I2P, Boosting Stealthy DDoS Threats
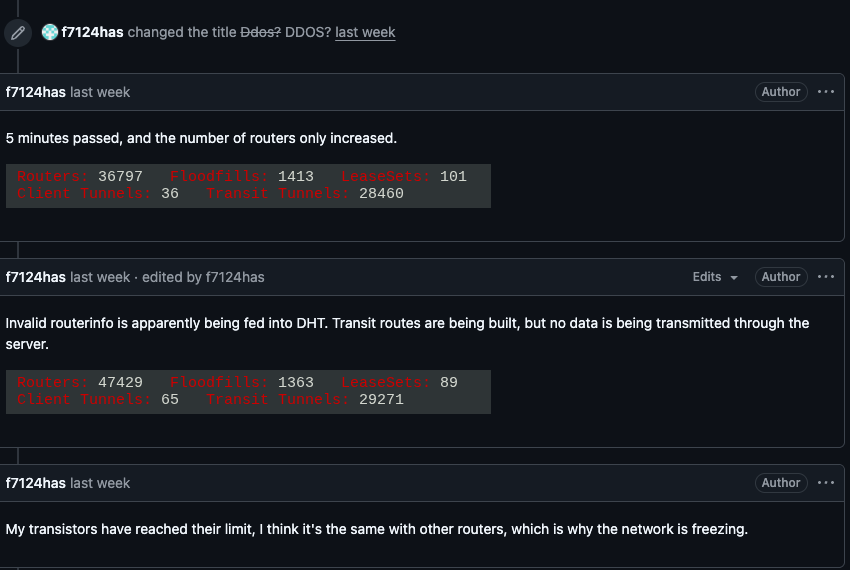
The Kimwolf botnet has started routing its command‑and‑control (C2) traffic through the I2P anonymity network. By embedding its C2 servers in I2P, the malware can issue high‑volume distributed denial‑of‑service (DDoS) commands while masking the origin of the traffic, making traditional network‑based detection and sink‑holing techniques far less effective.
Defenders must treat I2P traffic as a potential indicator of compromise, especially in environments that see unexplained spikes in outbound connections or inbound DDoS traffic. Monitoring for I2P handshake patterns, enforcing egress filtering, and integrating anonymizing‑network signatures into IDS/IPS rules will help mitigate the elevated risk posed by this more covert DDoS infrastructure.
Categories: Threat Intelligence, AI Security & Threats, Malware & Ransomware
Source: Read original article




Member discussion