Iranian Threat Actors Ramp Up IP‑Camera Hijacks to Fuel Kinetic Operations
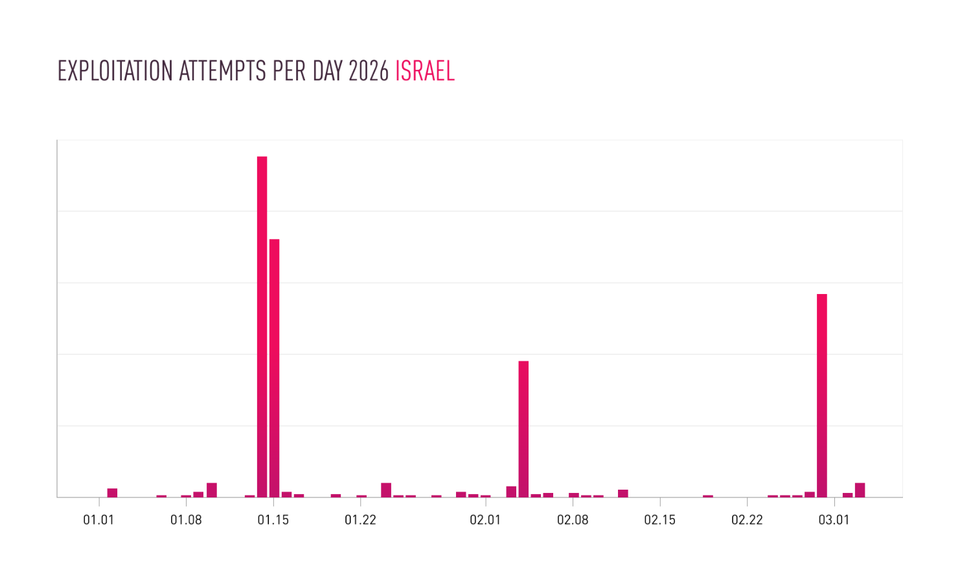
Checkpoint researchers have identified a coordinated surge in compromise of internet‑connected video cameras throughout the Middle East. The actors, linked to Iranian state‑aligned groups, are exploiting default credentials, outdated firmware, and unsecured network segments to gain persistent access to live feeds. The stolen footage is then repurposed to map troop movements, locate high‑value assets, and coordinate artillery or drone strikes, effectively blending cyber intrusion with kinetic battlefield actions.
Defenders must treat unsecured cameras as critical entry points rather than peripheral IoT devices. The abuse of visual streams provides adversaries with real‑time situational awareness that can shorten decision cycles for kinetic attacks, increasing collateral damage and operational surprise. Immediate mitigation steps include enforcing strong authentication, applying firmware updates, segregating camera traffic from core networks, and deploying continuous monitoring for anomalous video stream access. Ignoring these vectors leaves organizations vulnerable to both cyber espionage and indirect physical threats.
Categories: Threat Intelligence, Vulnerabilities & Exploits
Source: Read original article




Member discussion