Iranian Threat Actors Hijack IP Cameras in Middle East to Fuel Ops
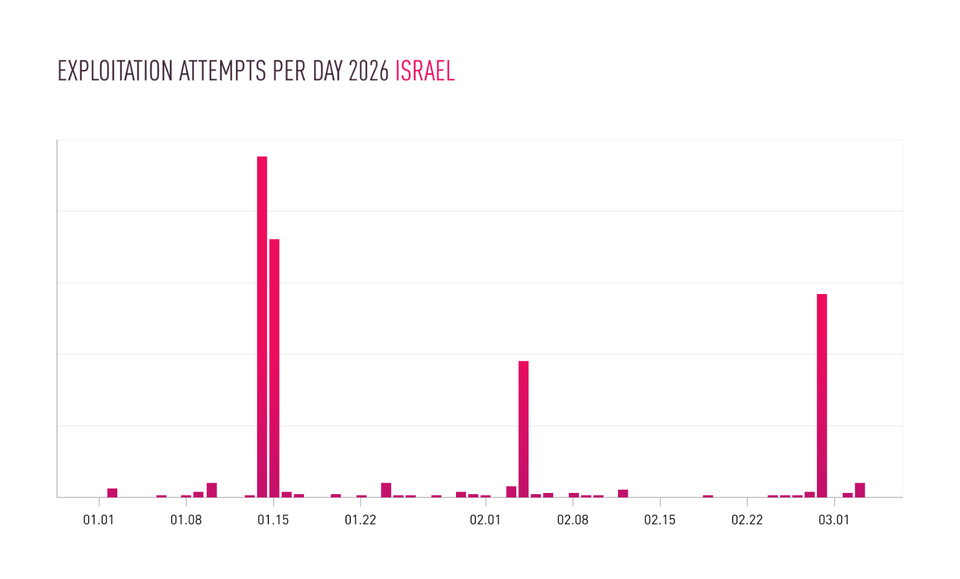
Check Point’s research team has documented a sharp increase in attacks linked to Iranian actors targeting unsecured IP cameras across the Middle East. The campaigns exploit default credentials and outdated firmware, allowing attackers to gain remote access, capture video feeds, and exfiltrate network information. By compromising these low‑cost, widely deployed devices, the threat group builds a picture of civilian and military activity without needing traditional espionage tools.
The compromised cameras are being used for real‑time reconnaissance to support kinetic operations, including targeting of infrastructure and coordination of ground forces. For defenders, the risk extends beyond privacy loss; compromised video streams can reveal defensive postures, movement patterns, and critical asset locations. Immediate actions—patching firmware, enforcing strong authentication, network segmentation, and continuous monitoring for anomalous camera traffic—are essential to deny the adversary this inexpensive intelligence source.
Categories: Threat Intelligence, Vulnerabilities & Exploits
Source: Read original article




Member discussion