Iranian Hackers Exploit IP Cameras in Middle‑East Conflict for Espionage and Attacks
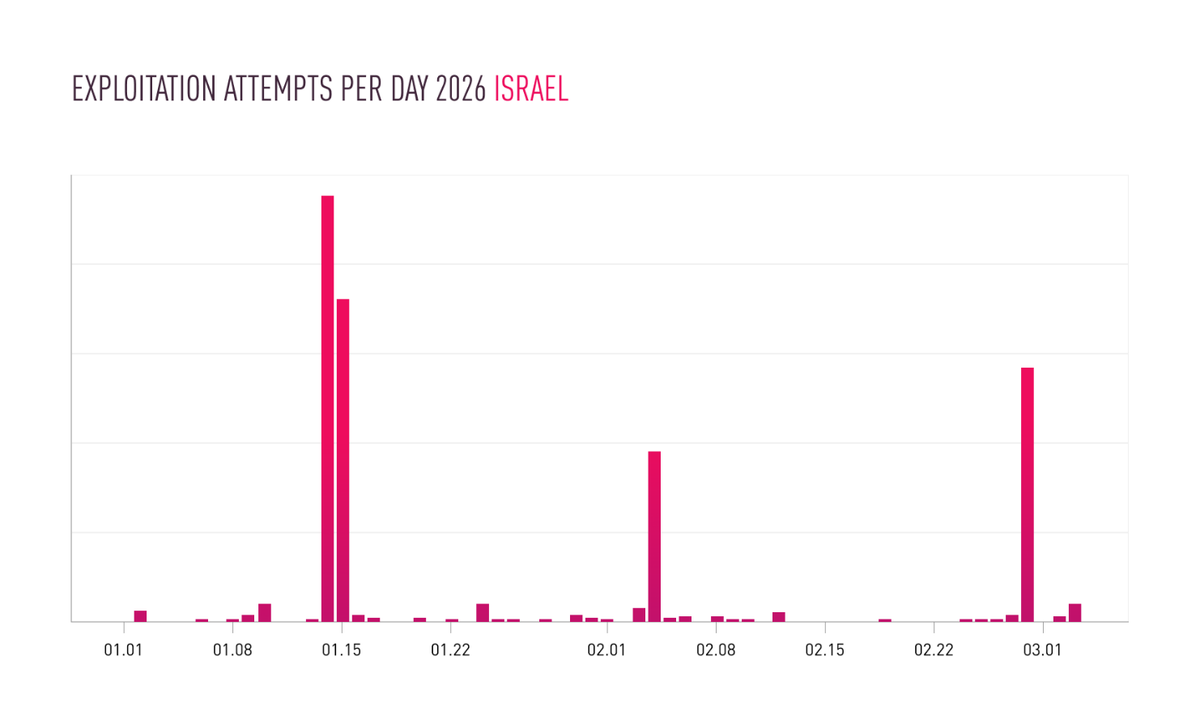
Checkpoint researchers have documented a sharp rise in compromise attempts against Internet‑protocol cameras deployed in active conflict zones across the Middle East. The intrusion chain points to Iranian‑linked threat actors who first gain access through default credentials or unpatched firmware, then hijack live video feeds. These feeds are being harvested for real‑time intelligence and, in several cases, used to coordinate kinetic operations against on‑ground targets.
The abuse of hardened IoT assets threatens both privacy and physical security, turning ordinary surveillance equipment into force multipliers for hostile actors. Defenders must treat IP cameras as critical infrastructure: enforce strong authentication, isolate them on dedicated VLANs, apply firmware updates promptly, and monitor for anomalous outbound streams. Failure to do so leaves organizations vulnerable to espionage, targeted sabotage, and broader escalation in volatile regions.
Categories: Threat Intelligence
Source: Read original article



Comments ()