Iranian Groups Weaponize IP Cameras for Real‑Time Battlefield Intel
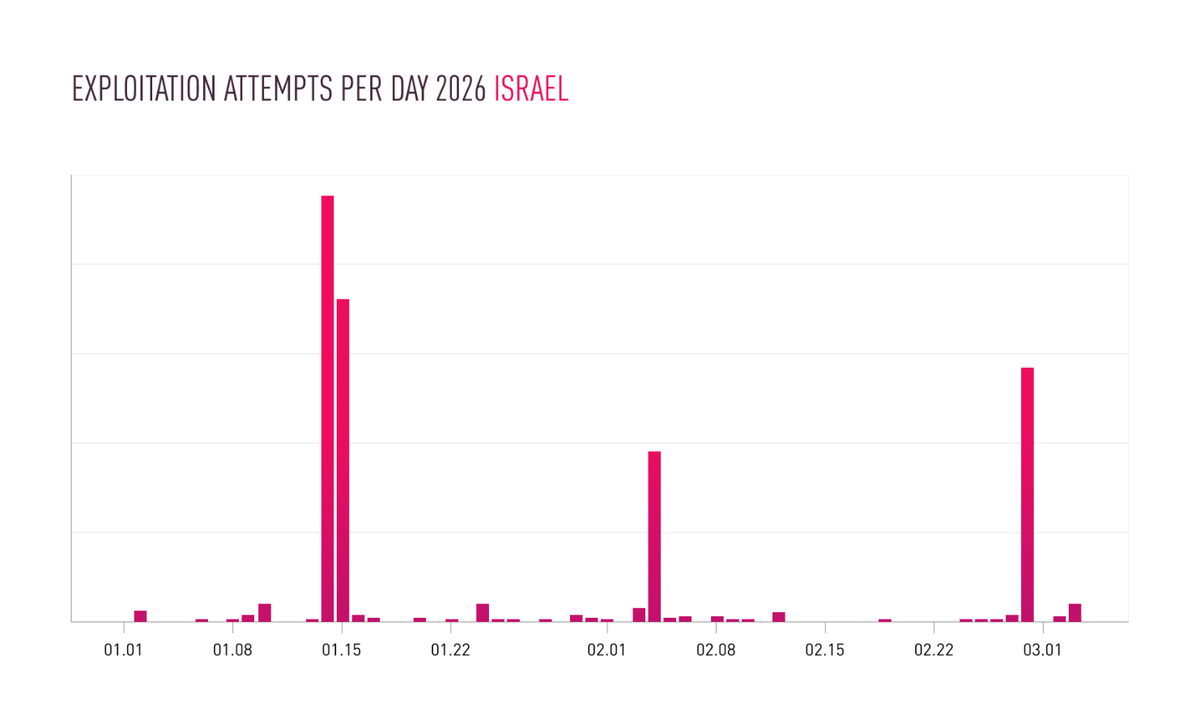
Check Point researchers have uncovered a coordinated campaign by Iranian‑affiliated threat actors that targets internet‑connected IP cameras across the region. The groups systematically scan for devices with default usernames and passwords, then exploit unpatched firmware to gain persistent access. Once compromised, the cameras are used to stream live video, providing attackers with visual intelligence that can be fused with kinetic operations on the ground.
The breach gives adversaries real‑time situational awareness of critical sites, troop movements, and civilian gatherings, effectively turning ordinary surveillance equipment into a force multiplier. Defenders must prioritize hardening all IoT endpoints: enforce unique, strong credentials, apply vendor security updates promptly, segment camera traffic from core networks, and continuously monitor for anomalous outbound streams. Failure to secure these devices not only leaks sensitive visuals but also opens a foothold for broader intrusion campaigns.
Categories: Threat Intelligence, Vulnerabilities & Exploits
Source: Read original article



Comments ()