Interlock Ransomware Hijacks Enterprise Firewalls for Persistent Access, AWS Alerts
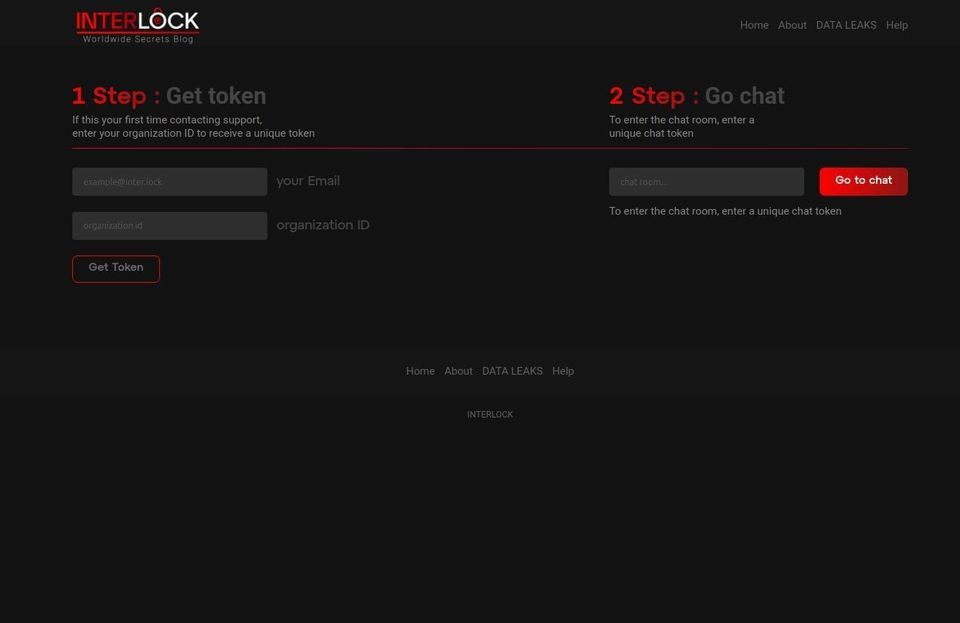
Amazon Web Services’ threat‑intelligence team has uncovered a new Interlock ransomware campaign that specifically compromises enterprise firewalls. By exploiting known and zero‑day vulnerabilities in firewall firmware and management interfaces, the actors achieve long‑term network persistence, install back‑door C2 channels, and only then deploy ransomware to encrypt data. The blog details the observed command‑and‑control infrastructure, including malicious domains, IP ranges, and the typical kill‑chain steps used by the group.
The compromise of firewalls erodes the very control plane that separates trusted and untrusted zones, giving attackers unfettered lateral movement and the ability to exfiltrate or encrypt critical assets at scale. Defenders must prioritize immediate firewall patching, enforce strict management‑plane access controls, monitor for anomalous outbound connections, and block identified C2 endpoints. Failure to act can result in widespread encryption, extended downtime, and significant ransom demands, making this a high‑priority threat for any organization relying on perimeter defenses.
Categories: Malware & Ransomware, Cloud & SaaS Security, Threat Intelligence
Source: Read original article




Member discussion